In Verizon’s just-released 2023 Information Breach Investigations Report, cash is king, and denial of service and social engineering nonetheless maintain sway.

Verizon’s just-released 2023 Information Breach Investigations Report reveals the continued effectiveness of enterprise e mail compromises. The research, which tracked incidents occurring between November 1, 2021 and October 31, 2022, discovered that BEC assaults doubled and represented greater than 50% of social engineering assaults. The worldwide research included incidents within the Asia-Pacific areas, EMEA, North America, and Latin America.
BECs have developed to incorporate a number of refined gambits, together with one not too long ago reported by Avanan, a unit of Verify Level Software program, involving the usage of respectable companies, like Dropbox, to cover malware.
The research provided a broad take a look at actors, actions, traits and incidents throughout industries, noting that public administration (3,270 incidents), data (2,105), finance (1,829) and manufacturing (1,814) are the sectors that skilled the best numbers of incidents over the interval.
The report provided these main findings:
- 74% of all breaches included the human factor, with individuals being concerned both by way of error, privilege misuse, use of stolen credentials or social engineering.
- 83% of breaches concerned exterior actors, and the first motivation for assaults continues to be overwhelmingly financially pushed (95%).
- The three main methods by which attackers entry a company are stolen credentials, phishing and exploitation of vulnerabilities.
Bounce to:
Social engineering pretexts trick customers into dropping credentials
Constructed upon evaluation of 953,894 incidents, of which 254,968 are confirmed breaches, the Verizon research discovered that fifty% of all social engineering incidents through the research interval used pretexting, a phishing tactic that entails tricking somebody into giving up data that will lead to a breach. In response to the research, the follow, which is usually utilized in BEC assaults, doubled in quantity in comparison with the prior yr’s.
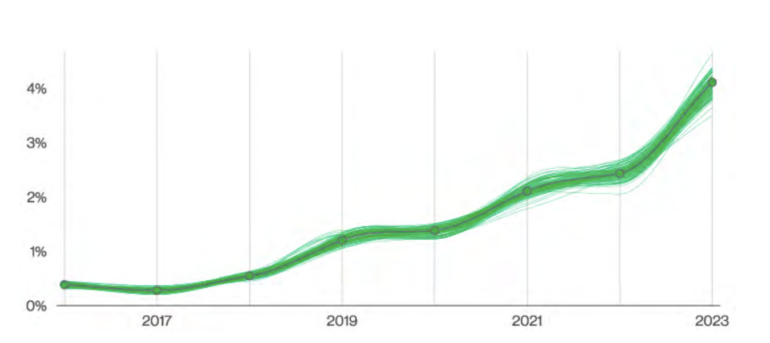
Verizon reported 1,700 social engineering incidents total, with attackers most frequently utilizing it to steal credentials (Determine A).
Determine A
SEE: Half of corporations tracked in a brand new research have been hit by spearphishing campaigns (TechRepublic)
Monetary acquire trumps politics in exploits
An uptick in espionage and state-aligned actors however, the Verizon research reported that monetary motives have been behind 94.6% of breaches, with organized crime being essentially the most prevalent risk actor.
The authors of the research additionally reported a fourfold improve this yr within the variety of breaches involving cryptocurrency in comparison with the prior yr’s recorded breaches. “That may be a far cry from the times of innocence in 2020 and earlier, after we received one or two instances most annually,” they wrote.
Verizon reported the chances of financially motivated assaults by class:
- System intrusions: 97%, with solely 3% geared toward espionage.
- Social engineering exploits: 89%, with 11% geared toward espionage.
- Fundamental internet utility assaults: 95%, with 4% geared toward espionage.
- Misplaced and stolen property: 100% monetary acquire.
DDoS tops the checklist of assault patterns
Verizon reported 6,248 distributed denial of service incidents. The research’s authors famous the brute power DDoS tactic known as DNS water torture reportedly grew in prevalence (Determine B).
Determine B
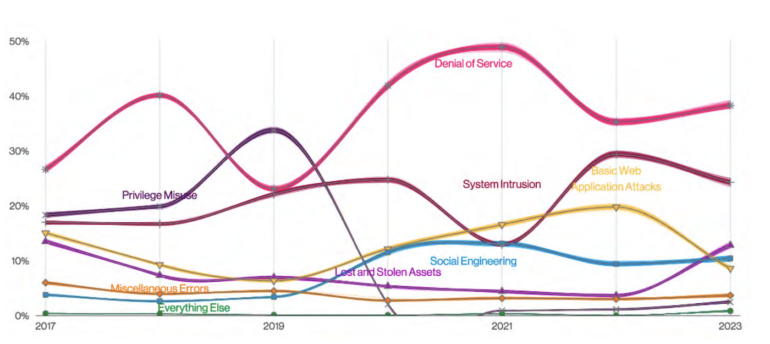
“A degree of consideration that a few of our companions delivered to us was the expansion of distributed DNS Water Torture assaults in, you guessed it, shared DNS infrastructure,” the research authors wrote, noting the assaults are a useful resource exhaustion assault finished by querying random identify prefixes on the DNS cache server so it at all times misses and forwards it to the authoritative server.
In response to the research, there have been 3,966 system intrusion incidents involving assaults utilizing malware to breach organizations, which frequently resulted within the supply of ransomware. In 34% of instances, information compromised was private in nature, adopted by system information, and eventually inner information.
SEE: Internet customers are usually not very conscious of their information footprints. (TechRepublic)
Use of stolen credentials drives internet utility assaults
About one quarter of Verizon’s dataset for its research concerned primary internet utility assaults, 86% of them utilizing stolen credentials, which attackers make use of to achieve entry to enterprises. The research reported 1,404 such incidents over its interval of statement, with 86% geared toward credential theft, 72% for private information and 41% searching for inner information.
Verizon additionally recorded 602 miscellaneous errors that embody misconfigurations typically dedicated by system directors and builders. The research reported that 99% of those errors have been inner, with 89% of compromises involving private information.
Insiders, sure, however largely exterior actors
Attackers on the surface have been accountable for 83% of breaches, whereas inner actors (intentionally or inadvertently) accounted for 19% of breaches, in keeping with Verizon. The report’s authors stated 62% of all incidents have been dedicated by organized crime.
Stolen credentials: The most typical motion
Almost half of breaches within the research interval concerned theft of credentials, with supply of ransomware being the central motion in simply over 20% of breaches. Phishing was the motion attackers took in 12% of exterior assaults, adopted by breaches, by which the actions attackers targeted on have been:
- Pretexting
- Exploiting vulnerabilities
- Creating misdeliveries
- Abusing privilege
- Putting in a backdoor
- Exfiltrating information
- Scanning networks
Attacked property led by internet servers
The overwhelming majority of assaults tracked by Verizon (83%) affected servers. Solely 20% of assaults affected individuals instantly. A decreasingly small proportion of assaults impacted media, kiosks and terminals, networks and embedded techniques.