Pakistan’s APT36 menace group is utilizing a brand new and improved model of its core ElizaRAT customized implant, in what seems to be a rising variety of profitable assaults on Indian authorities companies, army entities, and diplomatic missions over the previous 12 months.
The most recent ElizaRAT variant contains new evasion methods, enhanced command-and-control (C2) capabilities, and an extra dropper part that makes it more durable for defenders to detect the malware, researchers at Test Level Analysis (CPR) found when analyzing the group’s actions just lately. Heightening the menace is a brand new stealer payload dubbed ApoloStealer, which APT36 has begun utilizing to gather focused file varieties from compromised methods, retailer their metadata, and switch the knowledge to the attacker’s C2 server.
A Step-by-Step Cyberattack Functionality
“With the introduction of their new stealer, the group can now implement a ‘step-by-step’ strategy, deploying malware tailor-made to particular targets,” says Sergey Shykevich, menace intelligence group supervisor at Test Level Software program. “This ensures that even when defenders detect their actions, they primarily discover solely a phase of the general malware arsenal.”
Heightening the problem is the menace group’s utilizing of respectable software program, residing off the land binaries (LoLBins), and legit companies like Telegram, Slack, and Google Drive for C2 communications. Using these companies has considerably difficult the duty of monitoring malware communications in community site visitors, Shykevich says.
APT36, who safety distributors variously monitor as Clear Tribe, Operation C-Main, Earth Karkaddan, and Mythic Leopard, is a Pakistani menace group that. since round 2013, has primarily focused Indian authorities and army entities in quite a few intelligence gathering operations. Like many different tightly targeted menace teams, APT36s campaigns have often focused organizations in different international locations, together with Europe, Australia, and the US.
The menace actor’s present malware portfolio contains instruments for compromising Home windows, Android, and more and more, Linux units. Earlier this 12 months, BlackBerry reported an APT36 marketing campaign the place 65% of the group’s assaults concerned ELF binaries (Linkable Executable and Linkable Format) focusing on Maya OS, a Unix-like working system that India’s protection ministry has developed as an alternative choice to Home windows. And SentinelOne final 12 months reported observing APT36 utilizing romantic lures to unfold malware known as CopraRAT on Android units belonging to Indian diplomatic and army personnel.
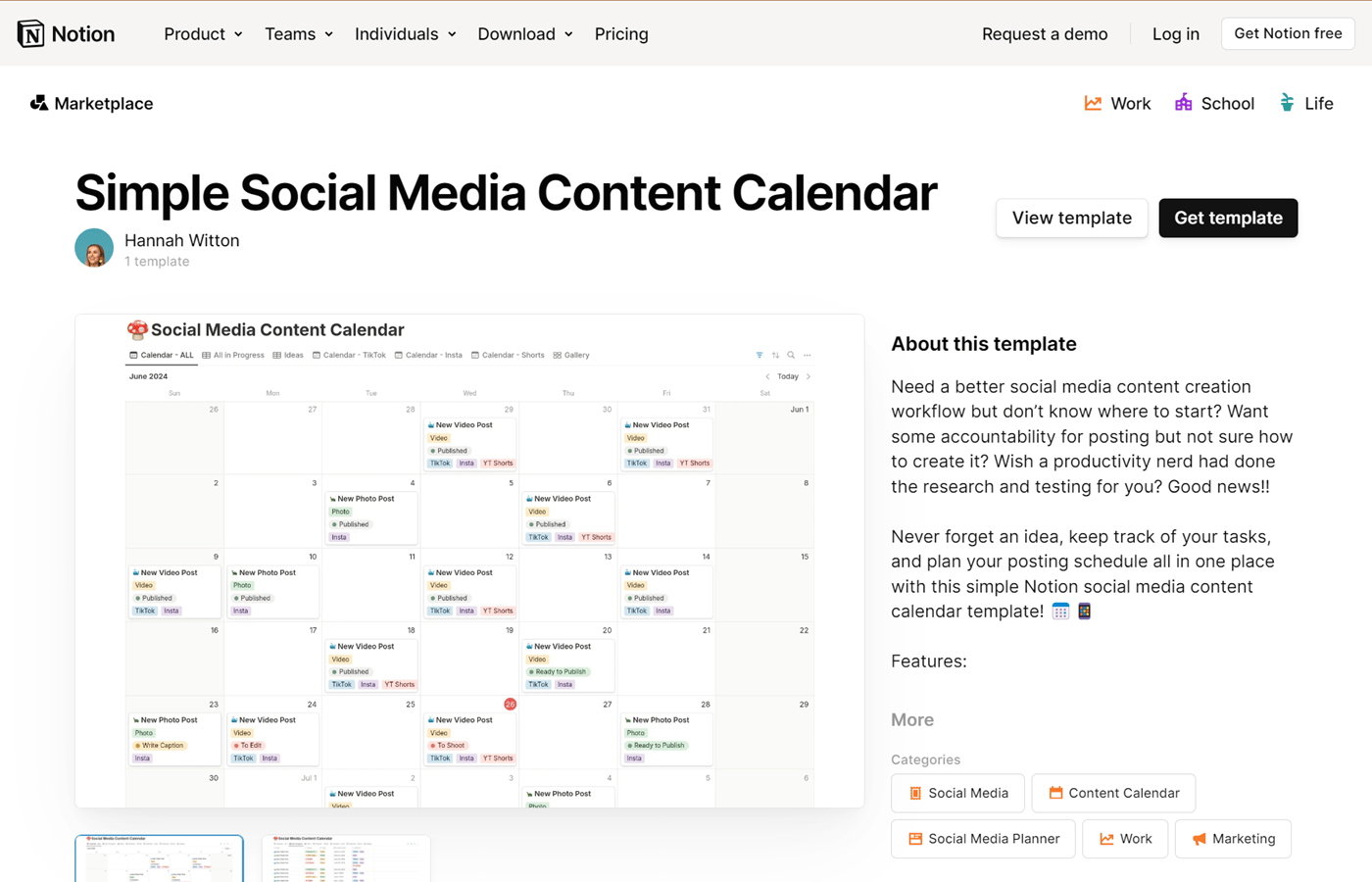
ElizaRAT is malware that the menace actor included into its assault equipment final September. The group has been distributing the malware by way of phishing emails containing hyperlinks to malicious Management Panel information (CPL) saved on Google Storage. When a person opens the CPL file, it runs code that initiates the malware an infection on their gadget, doubtlessly giving the attacker distant entry or management over the system.
Three Campaigns, Three Variations
Test Level researchers noticed APT36 actors utilizing not less than three totally different variations of ElizaRAT in three separate campaigns — all focusing on Indian entities — over the previous 12 months.
The primary was an ElizaRAT variant that used Slack channels as C2 infrastructure. APT36 started utilizing that variant someday late final 12 months and a couple of month later started deploying ApoloStealer with it. Beginning early this 12 months, the menace group switched to utilizing a dropper part to stealthily drop and unpack a compressed file containing a brand new and improved model of ElizaRAT. The brand new variant, like its predecessor first checked to confirm if the time zone of the machine it was on was set to Indian Customary Time earlier than executing and additional malicious exercise.
The most recent — third — model makes use of Google Drive for C2 communications. It lands on sufferer methods by way of malicious CPL information that act as a dropper for ElizaRAT. The CPL information execute quite a lot of duties together with making a working listing for the malware, establishing persistence and registering the sufferer with the C2 server. What units the newest model aside from the 2 earlier ElizaRAT iteration is its steady use of cloud companies like Google Cloud for its C2 communication, Shykevich says. As well as, the newest APT36 marketing campaign includes a new USB stealer known as ConnectX that the menace actor is utilizing to look at information on USBs and different exterior drives that may be hooked up to a compromised gadget, he says.
“Introducing new payloads corresponding to ApolloStealer marks a big growth of APT36’s malware arsenal and suggests the group is adopting a extra versatile, modular strategy to payload deployment,” CPR mentioned in its report. “These strategies primarily concentrate on knowledge assortment and exfiltration, underscoring their sustained emphasis on intelligence gathering and espionage.”