A monetary cybercrime group calling itself the Disneyland Group has been making liberal use of visually complicated phishing domains that spoof standard financial institution manufacturers utilizing Punycode, an Web normal that enables internet browsers to render domains with non-Latin alphabets like Cyrillic.
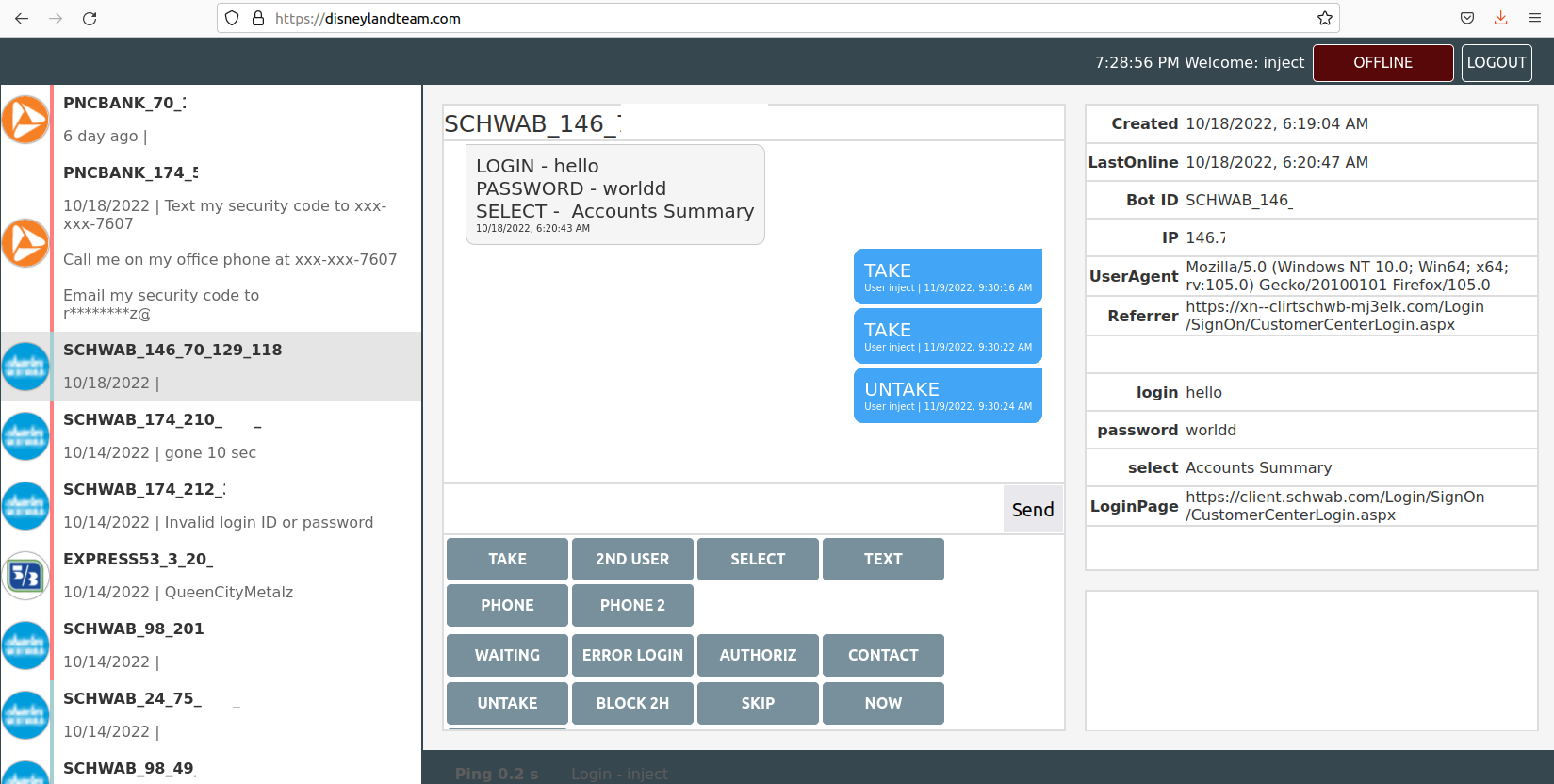
The Disneyland Group’s Internet interface, which permits them to work together with malware victims in actual time to phish their login credentials utilizing phony financial institution web sites.
The Disneyland Group makes use of widespread misspellings for prime financial institution manufacturers in its domains. For instance, one area the gang has used since March 2022 is ushank[.]com — which was created to phish U.S. Financial institution prospects.
However this group additionally normally makes use of Punycode to make their phony financial institution domains look extra legit. The U.S. monetary companies agency Ameriprise makes use of the area ameriprise.com; the Disneyland Group’s area for Ameriprise prospects is https://www.xn--meripris-mx0doj[.]com [brackets added to defang the domain], which shows within the browser URL bar as ạmeriprisẹ[.]com.
Look fastidiously, and also you’ll discover small dots beneath the “a” and the second “e”. You might be forgiven should you mistook one or each of these dots for a spec of mud in your pc display screen or cell gadget.
This candid view contained in the Disneyland Group comes from Alex Holden, founding father of the Milwaukee-based cybersecurity consulting agency Maintain Safety. Holden’s analysts gained entry to a Internet-based management panel the crime group has been utilizing to maintain observe of sufferer credentials (see screenshot above). The panel reveals the gang has been working dozens of Punycode-based phishing domains for the higher a part of 2022.
Take a look on the Punycode on this Disneyland Group phishing area: https://login2.xn--mirtesnbd-276drj[.]com, which reveals up within the browser URL bar as login2.ẹmirạtesnbd[.]com, a website concentrating on customers of Emirates NBD Financial institution in Dubai.
Right here’s one other area registered this yr by the Disneyland Group: https://xn--clientchwb-zxd5678f[.]com, which spoofs the login web page of economic advisor Charles Schwab with the touchdown web page of cliẹntșchwab[.]com. Once more, discover the dots beneath the letters “e” and “s”. One other Punycode area of theirs sends would-be victims to cliẹrtschwạb[.]com, which mixes a model misspelling with Punycode.
We see the identical dynamic with the Disneyland Group Punycode area https://singlepoint.xn--bamk-pxb5435b[.]com, which interprets to singlepoint.ụșbamk[.]com — once more phishing U.S. Financial institution prospects.
What’s occurring right here? Holden says the Disneyland Group is Russian-speaking — if not additionally primarily based in Russia — however it isn’t a phishing gang per se. Relatively, this group makes use of the phony financial institution domains along with malicious software program that’s already secretly put in on a sufferer’s pc.
Holden mentioned the Disneyland Group domains had been made to assist the group steal cash from victims contaminated with a robust pressure of Microsoft Home windows-based banking malware referred to as Gozi 2.0/Ursnif. Gozi focuses on accumulating credentials, and is especially used for assaults on client-side on-line banking to facilitate fraudulent financial institution transfers. Gozi additionally permits the attackers to hook up with a financial institution’s web site utilizing the sufferer’s pc.
In years previous, crooks like these would use custom-made “internet injects” to govern what Gozi victims see of their Internet browser after they go to their financial institution’s website. These internet injects allowed malware to rewrite the financial institution’s HTML code on the fly, and replica and/or intercept any information customers would enter right into a web-based kind, corresponding to a username and password.
Most Internet browser makers, nevertheless, have spent years including safety protections to dam such nefarious exercise. Because of this, the Disneyland Group merely tries to make their domains look as very similar to the actual factor as potential, after which funnel victims towards interacting with these imposter websites.
“The explanation that it’s infeasible for them to make use of in-browser injects embrace browser and OS safety measures, and difficulties manipulating dynamic pages for banks that require multi-factor authentication,” Holden mentioned.
In actuality, the pretend financial institution web site overlaid by the Disneyland Group’s malware relays the sufferer’s browser exercise by to the actual financial institution web site, whereas permitting the attackers to ahead any secondary login requests from the financial institution, corresponding to secret questions or multi-factor authentication challenges.
The Disneyland Group included directions for its customers, noting that when the sufferer enters their login credentials, he sees a 10-second spinning wheel, after which the message, “Awaiting again workplace approval on your request. Please don’t shut this window.”
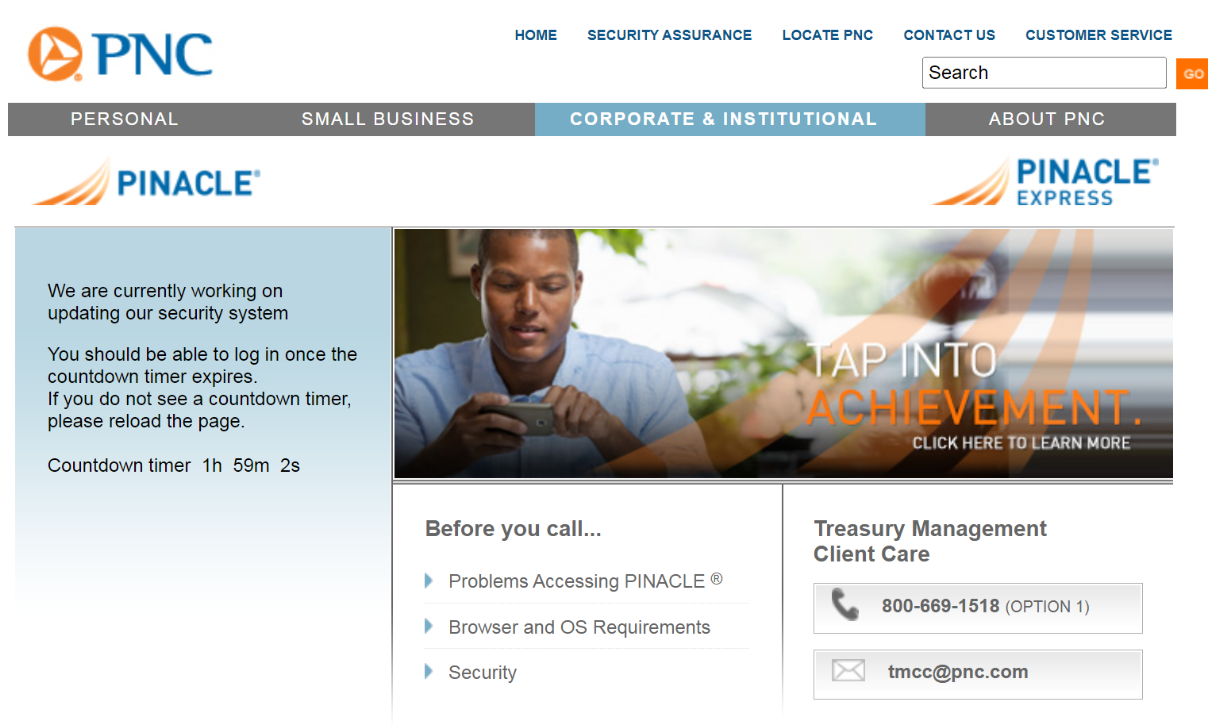
A pretend PNC web site overlay or “internet inject” displaying a message meant to briefly stop the consumer from accessing their account.
The “SKIP” button within the screenshot above sends the consumer to the actual financial institution login web page, “in case the account is just not fascinating to us,” the handbook explains. “Additionally, this redirect works if none of our operators are working on the time.”
The “TAKE” button within the Disneyland Group management panel permits customers or associates to assert possession over a selected contaminated machine or bot, which then excludes different customers from interacting with that sufferer.
Within the occasion that it someway takes a very long time to get the sufferer (bot) related to the Disneyland Group management panel, or whether it is essential to delay a transaction, customers can push a button that prompts the next message to look on the sufferer’s display screen:
“Your case ID quantity is 875472. A web based banking help consultant will get in contact shortly. Please present your case ID quantity, and DO NOT shut this web page.”
The Disneyland consumer handbook explains that the panel can be utilized to power the sufferer to log in once more in the event that they transmit invalid credentials. It additionally has different choices for stalling victims while their accounts are drained. One other pretend immediate the panel can produce reveals the sufferer a message saying, “We’re at present engaged on updating our safety system. You must have the ability to log in as soon as the countdown timer expires.”
The consumer handbook says this selection blocks the consumer from accessing their account for 2 hours. “It’s potential to dam for an hour with this button, on this case they get much less pissed off, inside the hours ddos will kill their community.”
Cybercrime teams will generally launch distributed denial-of-service (DDoS) assaults on the servers of the businesses they’re attempting to rob — which is normally meant to distract victims from their fleecing, though Holden mentioned it’s unclear if the Disneyland Group employs this tactic as nicely.
For a few years, KrebsOnSecurity tracked the day-to-day actions of the same malware crew that used internet injects and bots to steal tens of hundreds of thousands of {dollars} from small- to mid-sized companies throughout the USA.
On the finish of every story, I’d shut with a suggestion that anybody involved about malware snarfing their banking data ought to strongly take into account doing their on-line banking from a devoted, security-hardened system which is simply used for that objective. After all, the devoted system method works provided that you at all times use that devoted system for managing your account on-line.
These tales additionally noticed that for the reason that overwhelming majority of the malicious software program utilized in cyberheists is designed to run solely on Microsoft Home windows computer systems, it made sense to choose a non-Home windows pc for that devoted banking system, corresponding to a Mac or perhaps a model of Linux. I nonetheless stand by this recommendation.
In case anybody is , right here (PDF) is an inventory of all phishing domains at present and beforehand utilized by the Disneyland Group.







_Alexander-Yakimov_Alamy.jpg?disable=upscale&width=1200&height=630&fit=crop)
