Peter is an IT supervisor for a know-how producer that obtained hit with a Russian ransomware pressure known as “Zeppelin” in Might 2020. He’d been on the job lower than six months, and due to the best way his predecessor architected issues, the corporate’s knowledge backups additionally had been encrypted by Zeppelin. After two weeks of stalling their extortionists, Peter’s bosses had been able to capitulate and pay the ransom demand. Then got here the unlikely name from an FBI agent. “Don’t pay,” the agent stated. “We’ve discovered somebody who can crack the encryption.”
Peter, who spoke candidly concerning the assault on situation of anonymity, stated the FBI informed him to contact a cybersecurity consulting agency in New Jersey known as Unit 221B, and particularly its founder — Lance James. Zeppelin sprang onto the crimeware scene in December 2019, nevertheless it wasn’t lengthy earlier than James found a number of vulnerabilities within the malware’s encryption routines that allowed him to brute-force the decryption keys in a matter of hours, utilizing almost 100 cloud pc servers.
In an interview with KrebsOnSecurity, James stated Unit 221B was cautious of promoting its potential to crack Zeppelin ransomware keys as a result of it didn’t need to tip its hand to Zeppelin’s creators, who had been more likely to modify their file encryption method in the event that they detected it was by some means being bypassed.
This isn’t an idle concern. There are a number of examples of ransomware teams doing simply that after safety researchers crowed about discovering vulnerabilities of their ransomware code.
“The minute you announce you’ve obtained a decryptor for some ransomware, they alter up the code,” James stated.
However he stated the Zeppelin group seems to have stopped spreading their ransomware code progressively over the previous 12 months, presumably as a result of Unit 221B’s referrals from the FBI allow them to quietly assist almost two dozen sufferer organizations recuperate with out paying their extortionists.
In a weblog put up printed right this moment to coincide with a Black Hat Dubai speak on their discoveries, James and co-author Joel Lathrop stated they had been motivated to crack Zeppelin after the ransomware gang began attacking nonprofit and charity organizations.
“What motivated us probably the most through the leadup to our motion was the focusing on of homeless shelters, nonprofits and charity organizations,” the 2 wrote. “These mindless acts of focusing on those that are unable to reply are the motivation for this analysis, evaluation, instruments, and weblog put up. A normal Unit 221B rule of thumb round our places of work is: Don’t [REDACTED] with the homeless or sick! It is going to merely set off our ADHD and we’ll get into that hyper-focus mode that’s good should you’re a very good man, however not so nice if you’re an ***gap.”
The researchers stated their break got here after they understood that whereas Zeppelin used three various kinds of encryption keys to encrypt recordsdata, they may undo the entire scheme by factoring or computing simply one in every of them: An ephemeral RSA-512 public key that’s randomly generated on every machine it infects.
“If we will recuperate the RSA-512 Public Key from the registry, we will crack it and get the 256-bit AES Key that encrypts the recordsdata!” they wrote. “The problem was that they delete the [public key] as soon as the recordsdata are totally encrypted. Reminiscence evaluation gave us a couple of 5-minute window after recordsdata had been encrypted to retrieve this public key.”
Unit 221B in the end constructed a “Stay CD” model of Linux that victims may run on contaminated techniques to extract that RSA-512 key. From there, they might load the keys right into a cluster of 800 CPUs donated by internet hosting large Digital Ocean that may then begin cracking them. The corporate additionally used that very same donated infrastructure to assist victims decrypt their knowledge utilizing the recovered keys.
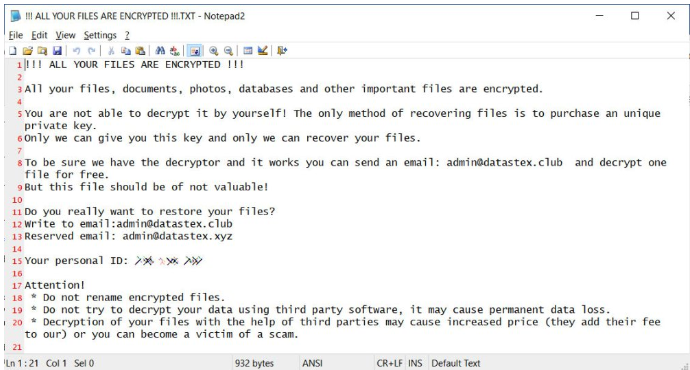
A typical Zeppelin ransomware be aware.
Jon is one other grateful Zeppelin ransomware sufferer who was aided by Unit 221B’s decryption efforts. Like Peter, Jon requested that his final identify and that of his employer be omitted from the story, however he’s accountable for IT for a mid-sized managed service supplier that obtained hit with Zeppelin in July 2020.
The attackers that savaged Jon’s firm managed to phish credentials and a multi-factor authentication token for some instruments the corporate used to help prospects, and in brief order they’d seized management over the servers and backups for a healthcare supplier buyer.
Jon stated his firm was reluctant to pay a ransom partly as a result of it wasn’t clear from the hackers’ calls for whether or not the ransom quantity they demanded would offer a key to unlock all techniques, and that it will accomplish that safely.
“They need you to unlock your knowledge with their software program, however you may’t belief that,” Jon stated. “You need to use your individual software program or another person who’s trusted to do it.”
In August 2022, the FBI and the Cybersecurity & Infrastructure Safety Company (CISA) issued a joint warning on Zeppelin, saying the FBI had “noticed situations the place Zeppelin actors executed their malware a number of occasions inside a sufferer’s community, ensuing within the creation of various IDs or file extensions, for every occasion of an assault; this ends in the sufferer needing a number of distinctive decryption keys.”
The advisory says Zeppelin has attacked “a spread of companies and demanding infrastructure organizations, together with protection contractors, instructional establishments, producers, know-how corporations, and particularly organizations within the healthcare and medical industries. Zeppelin actors have been recognized to request ransom funds in Bitcoin, with preliminary quantities starting from a number of thousand {dollars} to over one million {dollars}.”
The FBI and CISA say the Zeppelin actors acquire entry to sufferer networks by exploiting weak Distant Desktop Protocol (RDP) credentials, exploiting SonicWall firewall vulnerabilities, and phishing campaigns. Previous to deploying Zeppelin ransomware, actors spend one to 2 weeks mapping or enumerating the sufferer community to establish knowledge enclaves, together with cloud storage and community backups, the alert notes.
Jon stated he felt so fortunate after connecting with James and listening to about their decryption work, that he toyed with the concept of shopping for a lottery ticket that day.
“This simply doesn’t often occur,” Jon stated. “It’s one hundred pc like profitable the lottery.”
By the point Jon’s firm obtained round to decrypting their knowledge, they had been compelled by regulators to show that no affected person knowledge had been exfiltrated from their techniques. All informed, it took his employer two months to completely recuperate from the assault.
“I positively really feel like I used to be ill-prepared for this assault,” Jon stated. “One of many issues I’ve realized from that is the significance of forming your core workforce and having these individuals who know what their roles and duties are forward of time. Additionally, making an attempt to vet new distributors you’ve by no means met earlier than and construct belief relationships with them may be very tough to do when you’ve gotten prospects down laborious now and so they’re ready on you to assist them get again up.”
A extra technical writeup on Unit 221B’s discoveries (cheekily titled “0XDEAD ZEPPELIN”) is out there right here.










