Within the first a part of this sequence, we took a detailed have a look at CVSS and the way it works, concluding that whereas CVSS could supply some advantages, it’s not designed for use as a sole technique of prioritization. On this article, we’ll cowl some various instruments and programs for remediation prioritization, how they can be utilized, and their execs and cons.
EPSS, first revealed at Black Hat USA 2019, is (like CVSS) maintained by a FIRST Particular Curiosity Group (SIG). As famous within the whitepaper that accompanied the Black Hat speak, the creators of EPSS intention to fill a niche within the CVSS framework: predicting the likelihood of exploitation based mostly on historic information.
The unique model of EPSS used logistic regression: a statistical method to measure the likelihood of a binary end result by contemplating the contribution a number of unbiased variables make to that end result. As an example, if I wished to make use of logistic regression to measure the likelihood of a sure/no occasion occurring (say, whether or not a given individual will buy one in every of my merchandise), I’d look to gather a big pattern of historic advertising information for earlier clients and would-be clients. My unbiased variables can be issues like age, gender, wage, disposable earnings, occupation, locale, whether or not an individual already owned a rival product, and so forth. The dependent variable can be whether or not the individual purchased the product or not.
The logistic regression mannequin would inform me which of these variables make a major contribution to that end result, both constructive or adverse. So, for instance, I’d discover that age < 30 and wage > $50,000 are positively correlated to the end result, however already owns related product = true is, unsurprisingly, negatively correlated. By weighing up the contributions to those variables, we will feed new information into the mannequin and get an concept of the likelihood of any given individual wanting to purchase the product. It’s additionally essential to measure the predictive accuracy of logistic regression fashions (as they might lead to false positives or false negatives), which may be achieved with Receiver Working Attribute (ROC) curves.
The creators of EPSS analyzed over 25,000 vulnerabilities (2016 – 2018), and extracted 16 unbiased variables of curiosity together with the affected vendor, whether or not exploit code existed within the wild (both in Exploit-DB or in exploit frameworks like Metasploit and Canvas), and the variety of references within the revealed CVE entry. These have been the unbiased variables; the dependent variable was whether or not the vulnerability had really been exploited within the wild (based mostly on information from Proofpoint, Fortinet, AlienVault, and GreyNoise).
The authors discovered that the existence of weaponized exploits made probably the most important constructive contribution to the mannequin, adopted by Microsoft being the affected vendor (doubtless as a result of quantity and recognition of merchandise Microsoft develops and releases, and its historical past of being focused by menace actors); the existence of proof-of-concept code; and Adobe being the affected vendor.
Apparently, the authors additionally famous some adverse correlation, together with Google and Apple being the affected distributors. They surmised that this can be resulting from Google merchandise having many vulnerabilities, of which comparatively few have been exploited within the wild, and Apple being a closed platform that menace actors haven’t traditionally focused. The inherent traits of a vulnerability (i.e., the data mirrored in a CVSS rating) appeared to make little distinction to the end result – though, as one would possibly count on, distant code execution vulnerabilities have been extra prone to be exploited in comparison with, say, native reminiscence corruption bugs.
EPSS was initially carried out in a spreadsheet. It supplied an estimate of likelihood {that a} given vulnerability can be exploited throughout the subsequent 12 months. Subsequent updates to EPSS adopted a centralized structure with a extra refined machine studying mannequin, expanded the function set (together with variables akin to public vulnerability lists, Twitter / X mentions, incorporation into offensive safety instruments, correlation of exploitation exercise to vendor market share and set up base, and the age of the vulnerability), and estimated the likelihood of exploitation inside a 30-day window somewhat than 12 months.
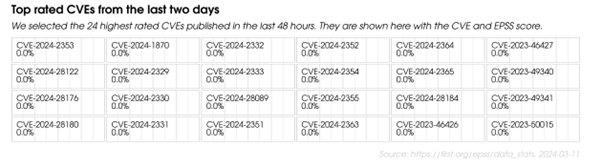
Determine 1: A screenshot from the EPSS Knowledge and Statistics web page, exhibiting the highest EPSS scores from the final 48 hours on the time the picture was captured. Observe that EPSS doesn’t conclude that many of those CVEs will find yourself being exploited
Whereas a easy on-line calculator is out there for v1.0, utilizing the newest model requires both downloading a each day CSV file from the EPSS Knowledge and Statistics web page, or utilizing the API. EPSS scores usually are not proven on the Nationwide Vulnerability Database (NVD), which favors CVSS scores, however they’re accessible on different vulnerability databases akin to VulnDB.
As famous in our earlier article on this sequence, CVSS scores haven’t traditionally been a dependable predictor of exploitation, so EPSS, in precept, looks as if a pure complement — it tells you in regards to the likelihood of exploitation, whereas CVSS tells you one thing in regards to the influence. For instance, say there’s a bug with a CVSS Base rating of 9.8, however an EPSS rating of 0.8% (i.e., whereas extreme whether it is exploited, the bug is lower than 1% prone to be exploited throughout the subsequent 30 days). Alternatively, one other bug might need a a lot decrease CVSS Base rating of 6.3, however an EPSS rating of 89.9% – during which case, you would possibly wish to prioritize it.
What you shouldn’t do (because the EPSS authors level out) is multiply CVSS scores by EPSS scores. Although this theoretically offers you a severity * menace worth, keep in mind that a CVSS rating is an ordinal rating. EPSS, its creators say, communicates totally different info from that of CVSS, and the 2 must be thought-about collectively however individually.
So is EPSS the proper companion to CVSS? Probably – like CVSS, it’s free to make use of, and affords helpful perception, but it surely does include some caveats.
What does EPSS really measure?
EPSS supplies a likelihood rating which signifies the chance of a given vulnerability being exploited typically. It doesn’t, and isn’t meant to, measure the chance of your group being focused particularly, or the influence of profitable exploitation, or any incorporation of an exploit into (as an illustration) a worm or a ransomware gang’s toolkit. The result it predicts is binary (exploitation both happens or it doesn’t – though word that it’s really extra nuanced than that: both exploitation happens or we don’t know if it has occurred), and so an EPSS rating tells you one factor: the likelihood of exploitation occurring throughout the subsequent 30 days. On a associated word, it’s value making a word of that point interval. EPSS scores ought to, by design, be recalculated, as they depend on temporal information. A single EPSS rating is a snapshot in time, not an immutable metric.
EPSS is a ‘pre-threat’ device
EPSS is a predictive, proactive system. For any given CVE, assuming the requisite info is out there, it is going to generate a likelihood that the related vulnerability might be exploited within the subsequent 30 days. You may then, if you happen to select to, issue on this likelihood for prioritization, supplied the vulnerability has not already been exploited. That’s, the system doesn’t present any significant perception if a vulnerability is being actively exploited, as a result of it’s a predictive measure. To return to our earlier instance of logistic regression, there’s little level working your information by means of my mannequin and attempting to promote you my product if you happen to already purchased it six weeks in the past. This appears apparent, but it surely’s nonetheless value making an allowance for: for vulnerabilities which have been exploited, EPSS scores can not add any worth to prioritization selections.
Lack of transparency
EPSS has an analogous problem to CVSS with regard to transparency, though for a special cause. EPSS is a machine studying mannequin, and the underlying code and information is just not accessible to most members of the FIRST SIG, not to mention most of the people. Whereas the maintainers of EPSS say that “bettering transparency is one in every of our objectives,” additionally they word that they can not share information as a result of “we have now a number of business companions who requested that we not share as a part of the information settlement. So far as the mannequin and code, there are numerous difficult facets to the infrastructure in place to assist EPSS.”
Assumptions and constraints
Jonathan Spring, a researcher at Carnegie Mellon College’s Software program Engineering Institute, factors out that EPSS depends on some assumptions which make it much less universally relevant than it might seem. EPSS’s web site claims that the system estimates “the chance (likelihood) {that a} software program vulnerability might be exploited within the wild.” Nonetheless, there are some generalizations right here. For instance, “software program vulnerability” refers to a broadcast CVE – however some software program distributors or bug bounty directors may not use CVEs for prioritization in any respect. As Spring notes, this can be as a result of a CVE has but to be revealed for a specific problem (i.e., a vendor is coordinating with a researcher on a repair, previous to publication), or as a result of the vulnerability is extra of a misconfiguration problem, which wouldn’t obtain a CVE in any case.
Likewise, “exploited” means exploitation makes an attempt that EPSS and its companions have been in a position to observe and file, and “within the wild” means the extent of their protection. The authors of the linked paper additionally word that, as a result of a lot of that protection depends on IDS signatures, there’s a bias in direction of network-based assaults in opposition to perimeter gadgets.
Numerical outputs
As with CVSS, EPSS produces a numerical output. And, as with CVSS, customers must be conscious that threat is just not reducible to a single numerical rating. The identical applies to any try to mix CVSS and EPSS scores. As an alternative, customers ought to take numerical scores into consideration whereas sustaining an consciousness of context and the programs’ caveats, which ought to influence how they interpret these scores. And, as with CVSS, EPSS scores are standalone numbers; there are not any suggestions or interpretation steering supplied.
Potential future disadvantages
The authors of EPSS word that attackers could adapt to the system. As an example, a menace actor could incorporate lower-scoring vulnerabilities into their arsenal, understanding that some organizations could also be much less prone to prioritize these vulnerabilities. On condition that EPSS makes use of machine studying, the authors additionally level out that attackers could sooner or later try to carry out adversarial manipulation of EPSS scores, by manipulating enter information (akin to social media mentions or GitHub repositories) to trigger overscoring of sure vulnerabilities.
SSVC, created by Carnegie Mellon College’s Software program Engineering Institute (SEI) in collaboration with CISA in 2019, could be very dissimilar to CVSS and EPSS in that it doesn’t produce a numerical rating as its output in any respect. As an alternative, it’s a decision-tree mannequin (within the conventional, logical sense, somewhat than in a machine studying sense). It goals to fill what its builders see as two main points with CVSS and EPSS: a) customers usually are not supplied with any suggestions or determination factors, however are anticipated to interpret numerical scores themselves; and b) CVSS and EPSS place the vulnerability, somewhat than the stakeholder, on the heart of the equation.
As per the SSVC whitepaper, the framework is meant to allow selections about prioritization, by following a call tree alongside a number of branches. From a vulnerability administration perspective, for instance, you begin by answering a query about exploitation: whether or not there’s no exercise, a proof-of-concept, or proof of lively exploitation. This results in selections about publicity (small, managed, or open), whether or not the kill chain is automatable, and ‘worth density’ (the sources {that a} menace actor would acquire after profitable exploitation). Lastly, there are two questions on security influence and mission influence. The ‘leaves’ of the tree are 4 attainable determination outcomes: defer, scheduled, out-of-cycle, or fast.

Determine 2: A pattern determination tree from the SSVC demo web site
Usefully, the newest model of SSVC additionally contains a number of different roles, together with patch suppliers, coordinators, and triage/publish roles (for selections about triaging and publishing new vulnerabilities), and in these instances the questions and determination outcomes are totally different. As an example, with coordination triage, the attainable outcomes are decline, monitor, and coordinate. The labels and weightings are additionally designed to be customizable relying on a company’s priorities and sector.
Having gone by means of the choice tree, you possibly can export a consequence to both JSON or PDF. The consequence additionally features a vector string, which might be acquainted to anybody who learn our evaluation of CVSS within the earlier article. Notably, this vector string incorporates a timestamp; some SSVC outcomes are meant to be recalculated, relying on the context. The authors of the SSVC whitepaper suggest recalculating scores which rely upon the ‘state of exploitation’ determination level as soon as a day, for instance, as a result of this could change quickly – whereas different determination factors, akin to technical influence, must be static.
Because the identify suggests, SSVC makes an attempt to place stakeholders on the heart of the choice by emphasizing stakeholder-specific points and decision-based outcomes, somewhat than numerical scores. One helpful end result of that is that you could apply the framework to vulnerabilities with out a CVE, or to misconfigurations; one other is that stakeholders from disparate sectors and industries can adapt the framework to swimsuit their very own wants. It’s additionally pretty easy to make use of (you possibly can strive it out right here), when you’ve obtained a deal with on the definitions.
To our data, there hasn’t been any unbiased empirical analysis into the effectiveness of SSVC, solely a small pilot examine carried out by SSVC’s creators. The framework additionally prefers simplicity over nuance in some respects. CVSS, for instance, has a metric for Assault Complexity, however SSVC has no equal determination level for ease or frequency of exploitation or something related; the choice level is solely whether or not or not exploitation has occurred and if a proof-of-concept exists.
And, presumably to keep away from over-complicating the choice tree, not one of the determination factors in any of the SSVC timber have an ‘unknown’ choice by default; as a substitute, customers are suggested to make a “cheap assumption” based mostly on prior occasions. In sure instances, this will likely skew the eventual determination, significantly close to determination factors exterior a company’s management (akin to whether or not a vulnerability is being actively exploited); analysts could also be uncomfortable with ‘guessing’ and err on the aspect of warning.
That being stated, it’s maybe no unhealthy factor that SSVC avoids numerical scores (though some customers may even see this as a draw back), and it has a number of different elements in its favor: It’s designed to be customizable; is absolutely open-source; and supplies clear suggestions as a remaining output. As with many of the instruments and frameworks we talk about right here, a strong method can be to mix it with others; inputting EPSS and CVSS particulars (and the KEV Catalog, mentioned beneath), the place relevant, right into a tailor-made SSVC determination tree is probably going to provide you an affordable indication of which vulnerabilities to prioritize.
The KEV Catalog, operated by the Cybersecurity and Infrastructure Safety Company (CISA), is a frequently up to date record of which CVEs menace actors are recognized to have actively exploited. As of December 2024, there are 1238 vulnerabilities on that record, with supplied particulars together with CVE-ID, vendor, product, a brief description, an motion to be taken (and a due date, which we’ll come to shortly), and a notes subject, usually containing a hyperlink to a vendor advisory.
As per CISA’s Binding Operational Directive 22-01, “federal, government department, departments and companies” are required to remediate relevant vulnerabilities within the KEV Catalog, together with another actions, inside a sure timeframe (six months for CVE-IDs assigned earlier than 2021, two weeks for all others). CISA’s justification for creating the KEV Catalog is just like factors we made in our earlier article: Solely a small minority of vulnerabilities are ever exploited, and attackers don’t seem to depend on severity rankings to develop and deploy exploits. Due to this fact, CISA argues, “recognized exploited vulnerabilities must be the highest precedence for remediation…[r]ather than have companies concentrate on hundreds of vulnerabilities which will by no means be utilized in a real-world assault.”
The KEV Catalog is just not up to date on a scheduled foundation, however inside 24 hours of CISA turning into conscious of a vulnerability that meets sure standards:
- A CVE-ID exists
- “There may be dependable proof that the vulnerability has been actively exploited within the wild”
- “There’s a clear remediation motion for the vulnerability”
In line with CISA, proof of lively exploitation – whether or not tried or profitable – comes from open-source analysis by its personal groups, in addition to “info instantly from safety distributors, researchers, and companions…info by means of US authorities and worldwide companions…and thru third-party subscription providers.” Observe that scanning exercise, or the existence of a proof-of-concept, usually are not enough for a vulnerability to be added to the Catalog.
Full disclosure: Sophos is a member of the JCDC, which is the a part of CISA that publishes the KEV Catalog
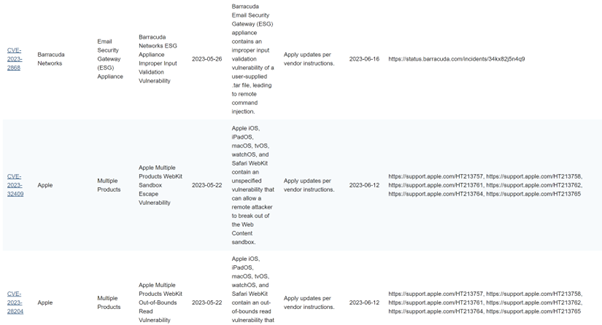
Determine 3: Among the entries within the KEV Catalog
Whereas primarily aimed toward US federal companies, many non-public sector organizations have adopted the record for prioritization. It’s not arduous to see why; the Catalog supplies a easy and manageable assortment of lively threats, in CSV or JSON codecs, which might simply be ingested and, as CISA suggests, integrated right into a vulnerability administration program for prioritization. Crucially, CISA is evident that organizations shouldn’t rely solely on the Catalog, however take different sources of knowledge into consideration
Like EPSS, the KEV Catalog relies on a binary end result: if a bug is on the record, it’s been exploited. If it’s not, it hasn’t (or, extra precisely, we don’t know if it has or not). However there’s a number of contextual info KEV doesn’t present, which might help organizations with prioritization, significantly sooner or later because the record continues to develop and turn out to be extra unwieldy (and it’ll; there is just one cause a vulnerability would ever be faraway from the record, which is that if a vendor replace causes an “unexpected problem with higher influence than the vulnerability itself”).
As an example, the Catalog doesn’t element the quantity of exploitation. Has a bug been exploited as soon as, or a handful of instances, or hundreds of instances? It doesn’t present any details about affected sectors or geographies, which could possibly be helpful information factors for prioritization. It doesn’t let you know what class of menace actor is exploiting the vulnerability (apart from ransomware actors), or when the vulnerability was final exploited. As with our dialogue of EPSS, there are additionally points round what is taken into account a vulnerability, and the transparency of information. Relating to the previous, a KEV Catalog entry will need to have a CVE – which can be much less helpful for some stakeholders – and concerning the latter, its exploitation protection is restricted to what CISA’s companions can observe, and that information is just not accessible for inspection or corroboration. Nonetheless, a curated record of vulnerabilities that are believed to have been actively exploited is probably going helpful for a lot of organizations, and supplies further info on which to base selections about remediation.
You’re maybe beginning to get a way of how a few of these totally different instruments and frameworks may be mixed to provide a greater understanding of threat, and result in extra knowledgeable prioritization. CVSS offers a sign of a vulnerability’s severity based mostly on its inherent traits; the KEV Catalog tells you which of them vulnerabilities menace actors have already exploited; EPSS offers you the likelihood of menace actors exploiting a vulnerability sooner or later; and SSVC will help you attain a call about prioritization by taking a few of that info into consideration inside a personalized, stakeholder-specific decision-tree.
To some extent, CVSS, EPSS, SSVC, and the KEV Catalog are the ‘large hitters.’ Let’s now flip to some lesser-known instruments and frameworks, and the way they stack up. (For readability, we’re not going to have a look at schemes like CWE, CWSS, CWRAF, and so forth, as a result of they’re particular to weaknesses somewhat than vulnerabilities and prioritization.)
Vendor-specific schemes
A number of business entities supply paid vulnerability rating providers and instruments designed to help with prioritization; a few of these could embody EPSS-like prediction information generated by proprietary fashions, or EPSS scores along side closed-source information. Others use CVSS, maybe combining scores with their very own scoring programs, menace intelligence, vulnerability intelligence, and/or details about a buyer’s belongings and infrastructure. Whereas these choices could present a extra full image of threat and a greater information to prioritization in comparison with, say, CVSS or EPSS alone, they’re not usually publicly accessible and so aren’t open to analysis and evaluation.
Some product distributors have devised their very own programs and make their scores public. Microsoft has two such programs for vulnerabilities in its personal merchandise: a Safety Replace Severity Ranking System which, like CVSS, supplies a information to the severity of a vulnerability (Microsoft states that its rankings are based mostly on “the worst theoretical end result have been that vulnerability to be exploited”); and the Microsoft Exploitability Index, which goals to offer an evaluation of the chance of a vulnerability being exploited. This seems to be based mostly on Microsoft’s evaluation of the vulnerability; how tough it will be to take advantage of; and previous exploitation traits, somewhat than a statistical mannequin, though not sufficient info is supplied to verify this.
Pink Hat additionally has a Severity Rankings system, comprising 4 attainable rankings together with a calculated CVSS Base rating. Just like the Microsoft programs, this solely pertains to vulnerabilities in proprietary merchandise, and the means by which the scores are calculated usually are not clear.
CVE Developments (RIP) and alternate options
CVE Developments, which on the time of writing is just not lively resulting from X’s restrictions on utilization of its API, is a crowdsourced dashboard of knowledge scraped from X, Reddit, GitHub, and NVD. It confirmed the ten most at the moment mentioned vulnerabilities based mostly on that information.

Determine 4: The CVE Developments dashboard
As proven within the screenshot above, the dashboard included CVSS and EPSS scores, CVE info, and pattern tweets and Reddit posts, in addition to ‘revealed’ dates and a measurement of debate exercise in the previous few days (or 24 hours).
Whereas CVE Developments could possibly be helpful for getting an concept of the present ‘taste of the month’ CVEs among the many safety neighborhood – and may be useful in acquiring breaking information about new vulnerabilities – it didn’t help in prioritization above and past new, high-impact bugs. It solely confirmed ten vulnerabilities at a time, and a few of these – together with Log4j, as you possibly can see within the screenshot – have been comparatively outdated, although nonetheless being mentioned due to their prevalence and notoriety.
As famous above, CVE Developments is at the moment inactive, and has been since mid-2023. As of this writing, guests to the positioning obtain the next message, which additionally appeared as the ultimate message on its creator’s Twitter feed:
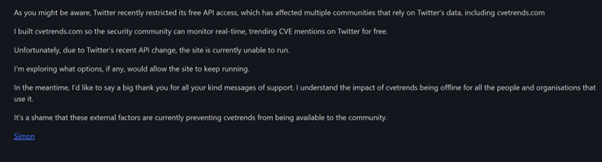
Determine 5: CVE Developments’ farewell message / tweet
It stays to be seen whether or not X will calm down its API utilization restrictions, or if the creator of CVE Developments, Simon J. Bell, might be able to discover different choices to revive the positioning’s performance.
After the demise of Bell’s web site, an organization known as Intruder developed their very own model of this device, in beta as of this writing, which can be known as ‘CVE Developments.’ It comes full with a 0-100 temperature-style ‘Hype rating’ based mostly on social media exercise.
SOCRadar additionally maintains an analogous service, known as ‘CVE Radar,’ which incorporates particulars of the variety of tweets, information experiences, and vulnerability-related repositories in its dashboard; in a touching gesture, it acknowledges Simon Bell’s CVE Developments work on its most important web page (as Intruder does on its About web page). Each CVE Radar and Intruder’s model of CVE Developments usefully incorporate the texts of associated tweets, offering an at-a-glance digest of the social media dialogue a couple of given bug. Whether or not the builders of both device intend to include different social media platforms, given the exodus from X, is unknown.
CVEMap
Launched in mid-2024, CVEMap is a comparatively new command-line interface device by ProjectDiscovery that goals to consolidate a number of facets of the CVE ecosystem – together with CVSS rating, EPSS rating, the age of the vulnerability, KEV Catalog entries, proof-of-concept information, and extra. CVEMap doesn’t supply or facilitate any new info or scores, because it’s solely an aggregation device. Nonetheless, the truth that it combines varied sources of vulnerability info right into a easy interface – whereas additionally permitting filtering by product, vendor, and so forth – could make it helpful for defenders searching for a method to make knowledgeable prioritization selections based mostly on a number of info sources.
Bug Alert
Bug Alert is a service designed to fill a particular hole for responders: It goals to alert customers solely to important, high-impact vulnerabilities (those that at all times appear to hit on a Friday afternoon or simply earlier than a public vacation) as shortly as attainable through electronic mail, SMS, or telephone notifications, with out having to attend for safety bulletins or CVE publication. It’s meant to be a community-driven effort, and depends on researchers submitting notices of latest vulnerabilities as pull requests to the GitHub repository. It’s not clear if Bug Alert’s writer remains to be sustaining it; on the time of writing, the final exercise on the Github repository was in October 2023.
As with CVE Developments, whereas Bug Alert could fill a helpful area of interest, it’s not designed for use for prioritization typically.
vPrioritizer
vPrioritizer is an open-source framework designed to permit customers to evaluate and perceive contextualized threat on a per-asset or per-vulnerability foundation, thereby merging asset administration with prioritization. That is achieved through the use of CVSS scores along with “neighborhood analytics” and outcomes from vulnerability scanners. Sadly, regardless of being talked about within the SSVC whitepaper in 2019 and offered on the Black Hat USA Arsenal in 2020, it isn’t clear if vPrioritizer’s developer nonetheless maintains the mission; as of this writing, the final decide to the GitHub repository was in October 2020.
Vulntology
Vulntology is a NIST-led effort to characterize vulnerabilities (the identify is a portmanteau of ‘vulnerability’ and ‘ontology’) in accordance with how they are often exploited, the potential influence of exploitation, and mitigating elements. Its acknowledged objectives embody the standardization of description of vulnerabilities (for instance, in vendor advisories and safety bulletins); bettering the extent of element in such descriptions; and enabling simpler sharing of vulnerability info throughout language limitations. An instance of a ‘vulntological illustration’ is out there right here.
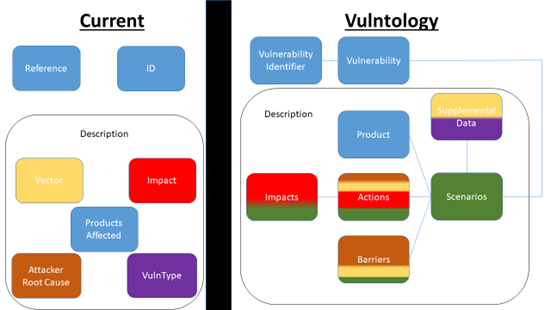
Determine 6: An illustration of Vulntology’s proposed work, taken from the mission’s GitHub repository
Vulntology is subsequently not a scoring framework, or perhaps a determination tree. As an alternative, it’s a small step in direction of a standard language, and one which can, if it turns into widely-adopted, be of serious worth on the subject of vulnerability administration. A standardized method to describing vulnerabilities would definitely be of use when evaluating a number of vendor safety advisories, vulnerability intelligence feeds, and different sources. We point out it right here as a result of it does have some implications for vulnerability prioritization, albeit within the long-term, and it’s making an attempt to unravel an issue throughout the vulnerability administration subject. The final decide to the mission’s Github seems to have occurred in spring 2023.
Legal market information
Lastly, a fast phrase on prison market information and the way future analysis would possibly put it to use for prioritization. Again in 2014, researchers from the College of Trento carried out a examine on whether or not CVSS scores are a superb predictor for exploitation. They concluded that CVSS scores don’t match the charges of exploitation, however they did conclude that remediation “in response to take advantage of presence in black markets yields the most important threat discount.” It might be an attention-grabbing avenue of analysis to see if the identical remains to be true at the moment; exploit markets have elevated in dimension since 2014, and there’s a giant underground financial system devoted to the advertising and promoting of exploits.
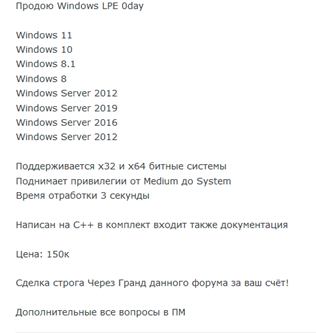
Determine 7: A person affords a Home windows native privilege escalation exploit on the market on a prison discussion board
Trying not solely on the existence of exploits in prison marketplaces, but in addition at costs, ranges of curiosity, and buyer suggestions, could possibly be additional helpful information factors in informing prioritization efforts.
The problem, in fact, is the issue of accessing these marketplaces and scraping information; many are closed to registration and solely accessible through referral, fee, or status. And whereas the underground financial system has elevated in dimension, it’s additionally arguably much less centralized than it as soon as was. Distinguished boards could function an preliminary place to promote wares, however lots of the salient particulars – together with costs – are typically solely accessible to potential consumers through non-public messages, and the precise negotiations and gross sales usually happen in out-of-band channels like Jabber, Tox, and Telegram. Additional analysis on this problem is required to find out if it could possibly be a possible supply of information for prioritization.
Having examined CVSS, EPSS, SSVC, and the KEV Catalog in depth – and another instruments and frameworks extra briefly – you gained’t be stunned to be taught that we didn’t discover a magic answer, or perhaps a magic mixture of options, that can remedy all prioritization issues. Nonetheless, a mixture is nearly at all times higher than utilizing a single framework. Extra information factors imply a extra knowledgeable view, and whereas this would possibly require some technical effort up entrance, the outputs of many of the instruments and frameworks we’ve mentioned are designed to be simply ingested in an automatic method (and instruments like CVEMap have carried out a few of the heavy lifting already).
In addition to combining outputs, customization can be actually essential. That is usually neglected, however prioritization isn’t simply in regards to the vulnerabilities, and even the exploits. After all, they’re an enormous a part of the problem, however the important thing level is {that a} vulnerability, from a remediation perspective, doesn’t exist in isolation; contemplating its inherent properties could also be useful in some circumstances, however the one actually important information level is how that vulnerability might influence you.
Furthermore, each group treats prioritization in a different way, relying on what it does, the way it works, what its price range and sources appear to be, and what its urge for food is for threat.
Single, one-size-fits-all scores and suggestions don’t usually make a lot logical sense from the attitude of assessing frameworks, however they make even much less sense from the attitude of particular person organizations attempting to prioritize remediation. Context is all the pieces. So no matter instruments or frameworks you employ, put your group – not a rating or a rating – on the heart of the equation. Chances are you’ll even wish to do that at a extra granular stage, relying on the scale and construction of your group: prioritizing and contextualizing per division, or division. In any case, customise as a lot as you possibly can, and keep in mind that nonetheless outstanding and standard a framework could also be, its outputs are solely a information.
With some programs, like CVSS or SSVC, there are built-in choices to customise and tailor outputs. With others, like EPSS and the KEV Catalog, customization isn’t actually the purpose, however you possibly can nonetheless add context to these outcomes your self, maybe by feeding that info into different instruments and frameworks and looking out on the complete image as a lot as attainable.
Prioritization additionally goes past the instruments we talk about right here, in fact. We’ve centered on them on this sequence as a result of they’re an attention-grabbing part of vulnerability administration, however the info that ought to feed into prioritization selections will ideally come from quite a lot of different sources: menace intelligence, weaknesses, safety posture, controls, threat assessments, outcomes from pentests and safety audits, and so forth.
To reiterate some extent from our first article, whereas we’ve identified a few of the downsides to those instruments and frameworks, we don’t intend in in any option to denigrate their builders or their efforts, and we’ve tried to be honest and even-handed in our assessments. Creating frameworks like these is a number of arduous work and requires appreciable thought and planning – and so they’re there for use, so it’s best to use them when and the place it is smart to take action. We hope that this sequence will permit you to do that in a secure, knowledgeable, and efficient method.









