Builders are more and more underneath assault by way of the instruments that they use to collaborate and to supply code — corresponding to Docker, Kubernetes, and Slack — as cybercriminals and nation-state actors intention to entry the dear software program that builders work on on daily basis.
For example, an attacker claimed on Sept. 18 to have used stolen Slack credentials to entry and replica greater than 90 movies representing the early growth of Grand Theft Auto 6, a preferred sport from Take-Two Interactive’s Rockstar Video games. And every week earlier, safety agency Development Micro found that attackers have been systematically looking for and trying to compromise misconfigured Docker containers.
Neither assault concerned vulnerabilities within the software program packages, however safety missteps or misconfiguration aren’t unusual on the a part of builders, who typically fail to take the care essential to safe their assault floor space, says Mark Loveless, a workers safety engineer at GitLab, a DevOps platform supplier.
“Lots of builders do not consider themselves as targets as a result of they’re considering that the completed code, the tip outcome, is what attackers are going after,” he says. “Builders typically take safety dangers — corresponding to organising check environments at house or taking down all the safety controls — to allow them to check out new issues, with the intent of including safety later.”
He provides, “Sadly, these habits grow to be replicated and grow to be tradition.”
Assaults towards the software program provide chain — and the builders who produce and deploy software program — have grown rapidly previously two years. In 2021, for instance, assaults that aimed to compromise builders’ software program — and the open supply parts extensively utilized by builders — grew by 650%, in keeping with the “2021 State of the “Software program Provide Chain” report, printed by software program safety agency Sonatype.
Developer Pipelines & Collaboration within the Sights
Total, safety specialists preserve that the quick tempo of steady integration and steady deployment environments (CI/CD) that kind the foundations of DevOps-style approaches pose vital dangers, as a result of they’re typically missed in relation to implementing hardened safety.
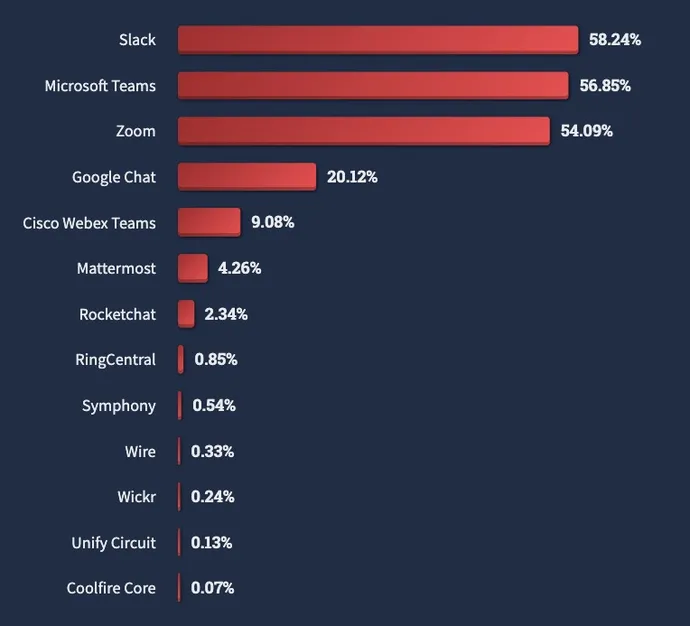
This impacts a wide range of instruments utilized by builders of their efforts to create extra environment friendly pipelines. Slack, for instance, is the preferred synchronous collaboration instruments in use amongst skilled builders, with Microsoft Groups and Zoom coming in a detailed second and third, in keeping with the 2022 StackOverflow Developer Survey. As well as, greater than two-thirds of builders use Docker and one other quarter use Kubernetes throughout growth, the survey discovered.
Breaches of instruments like Slack may be “nasty,” as a result of such instruments typically carry out crucial capabilities and normally solely have perimeter defenses, Matthew Hodgson, CEO and cofounder of messaging-platform Component, mentioned in a press release despatched to Darkish Studying.
“Slack will not be end-to-end encrypted, so it’s just like the attacker getting access to the corporate’s total physique of information,” he mentioned. “An actual fox-in-the-henhouse state of affairs.”
Past Misconfigs: Different Safety Woes for Builders
Cyberattackers, it must be famous, do not simply probe for misconfigurations or lax safety in relation to going after builders. In 2021, for instance, a risk group’s entry to Slack by way of the gray-market buy of a login token led to a breach of sport large Digital Arts, permitting the cybercriminals to repeat almost 800GB of supply code and knowledge from the agency. And a 2020 investigation into Docker pictures discovered that greater than half of the newest builds have crucial vulnerabilities that put any utility or service primarily based on the containers in danger.
Phishing and social engineering are additionally plagues within the sector. Simply this week, builders utilizing two DevOps companies — CircleCI and GitHub — have been focused with phishing assaults.
And, there is no such thing as a proof that the attackers concentrating on Rockstar Video games exploited a vulnerability in Slack — solely the claims of the purported attacker. As a substitute, social engineering was probably strategy to bypass safety measures, a Slack spokesperson mentioned in a press release.
“Enterprise-grade safety throughout id and system administration, knowledge safety, and knowledge governance is constructed into each side of how customers collaborate and get work executed in Slack,” the spokesperson mentioned, including: “These [social engineering] techniques have gotten more and more widespread and complicated, and Slack recommends all prospects observe robust safety measures to protect their networks towards social engineering assaults, together with safety consciousness coaching.”
Gradual Safety Enhancements, Extra Work to Do
Builders have solely slowly accepted safety as utility safety professionals name for higher controls, nevertheless. Many builders proceed to leak “secrets and techniques” — together with passwords and API keys — in code pushed to repositories. Thus, growth groups ought to concentrate on not simply defending their code and stopping the importing of untrusted parts but in addition making certain that the crucial capabilities of their pipelines aren’t compromised, GitLab’s Loveless says.
“The entire zero-trust half, which is usually about figuring out individuals and issues like that, there additionally must be the identical rules that ought to apply to your code,” he says. “So do not belief the code; it must be checked. Having individuals or processes in place that assumes the worst — I am not going to belief it robotically — significantly when the code is doing one thing crucial, like construct a challenge.”
As well as, many builders nonetheless don’t use primary measures to strengthen authentication, corresponding to utilizing multifactor authentication (MFA). There are adjustments afoot, nevertheless. More and more, the varied open supply software program package deal ecosystems have all began requiring that main initiatives undertake multifactor authentication.
By way of instruments to concentrate on, Slack has gained consideration due to the newest main breaches, however builders ought to attempt for a baseline degree of safety management throughout all of their instruments, Loveless says.
“There are ebbs and flows, however it’s no matter works for the attackers,” he says. “Talking from my expertise of sporting every kind of hats of various colours, as an attacker, you search for the simplest approach in, so if one other approach turns into simpler, you then say, ‘I’ll attempt that first.'”
GitLab has seen this follow-the-leader habits in its personal bug bounty packages, Loveless notes.
“We see when individuals ship in bugs, all of the sudden one thing — a brand new approach — will grow to be widespread, and an entire slew of submissions ensuing from that approach will are available in,” he says. “They undoubtedly are available in waves.”