Threat mitigation suggestions are supplied for every of those cybersecurity threats.
Cybersecurity firm ESET launched its H2 2023 risk report, and we’re highlighting three notably fascinating matters in it: the abuse of the ChatGPT identify by cybercriminals, the rise of the Lumma Stealer malware and the Android SpinOk SDK spy ware.
Bounce to:
ChatGPT identify is being abused by cybercriminals
Within the second half of 2023, ESET has blocked 650,000 makes an attempt to entry malicious domains whose names embody “chatgpt” or comparable string in an obvious reference to the ChatGPT chatbot.
One of many frauds resides within the OpenAI API for ChatGPT. The API wants a personal API key that have to be rigorously protected and by no means uncovered by customers, but some apps ask customers to supply their API keys so the purposes can use ChatGPT. As written by ESET researchers, “if the app sends your key to the developer’s server, there could also be little to no assure that your key is not going to be leaked or misused, even when the decision to the OpenAI API can also be made.”
A “ChatGPT Subsequent Internet” internet software taken for example by ESET has been put in on 7,000 servers. It’s unknown if this app was created as an effort in a ChatGPT API keys phishing marketing campaign or uncovered on the web for one more purpose.
The usage of the API secret is billed by OpenAI. So as soon as in possession of somebody’s non-public API key and relying on the customers or firm’s subscription, an attacker would possibly use it for their very own wants with out paying; the attacker may additionally resell it to different cybercriminals.
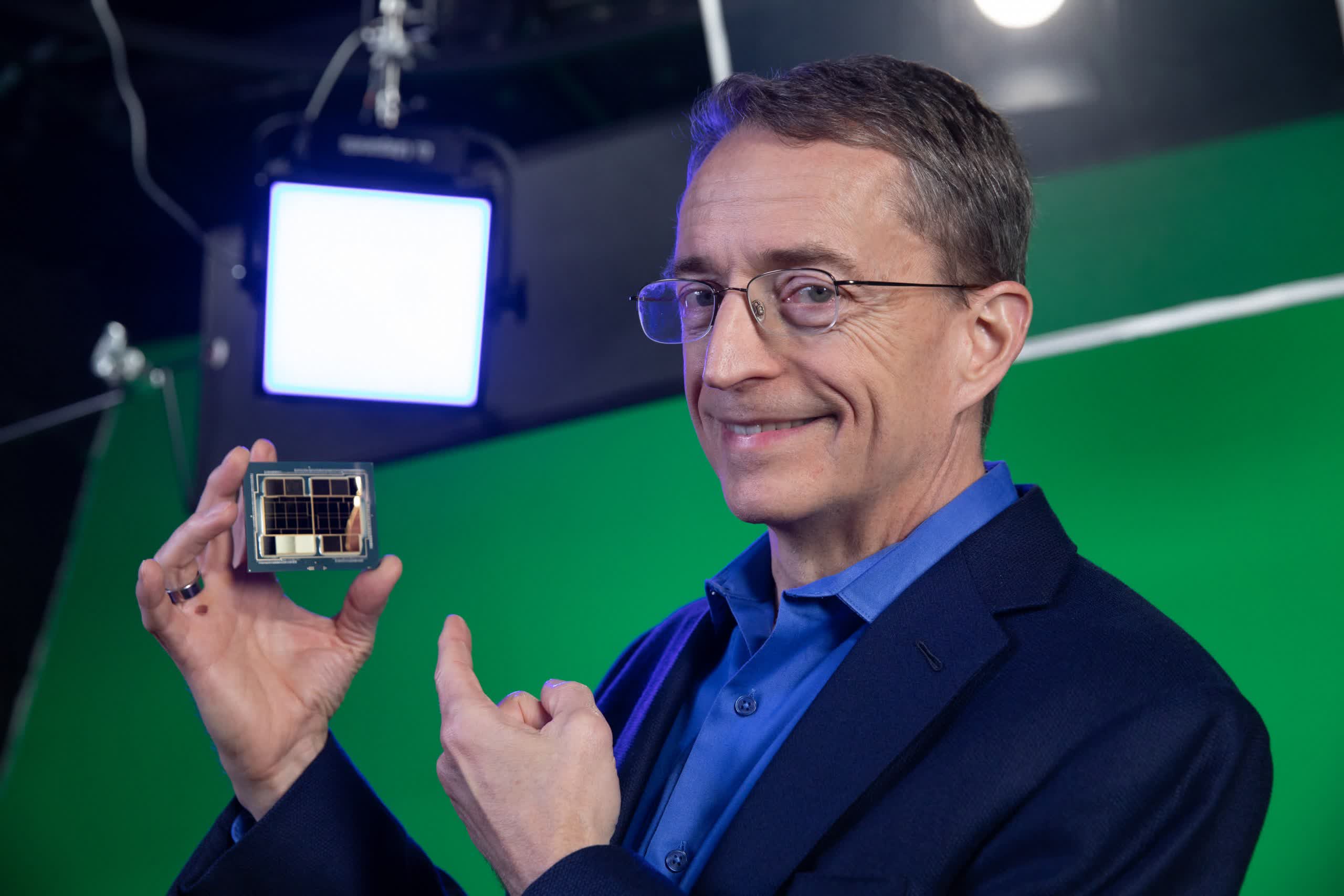
As well as, the second half of 2023 noticed loads of ChatGPT-inspired domains all resulting in malicious Google Chrome browser extensions detected as “JS/Chromex.Agent.BZ”. One instance is gptforchrome(.)com, resulting in such a malicious extension (Determine A).
Determine A
Suggestions associated to those ChatGPT safety threats
Customers must be educated to detect such threats and keep away from searching suspicious web sites associated to ChatGPT. They have to safe their non-public ChatGPT API key and by no means share it.
Lumma Stealer malware-as-a-service goes sturdy
In H2 2023, malicious cryptominers declined by 21% within the cryptocurrencies malware risk panorama, in line with ESET; nevertheless, cryptostealers are on the rise by greater than 68% for a similar interval, wrote the researchers.
This sturdy augmentation was brought on by a single particular risk: Lumma Stealer, which is also referred to as LummaC2 Stealer. This malware-as-a-service risk targets a number of cryptocurrency wallets in addition to customers’ credentials and two-factor authentication browser extensions. It additionally has exfiltration capabilities, rendering it a software that could be used for monetary fraud in addition to for cyberespionage functions.
In response to ESET, the deployment of Lumma Stealer tripled between H1 and H2 2023. A number of tiers are supplied for the malware with costs starting from $250 USD to $20,000 USD. The best choice permits the customer to get entry to the total C supply code for the malware. The customer can also be allowed to resell the malware independently of its developer.
The Lumma Stealer malware shares a standard code base with the notorious Mars, Arkei, and Vidar info stealers and may be very more likely to be developed by the identical writer, according to cybersecurity company Sekoia.
Numerous distribution vectors are used for spreading Lumma Stealer; ESET noticed these strategies within the wild: cracked installations of software program, YouTube, faux browser replace campaigns, content material supply community of Discord and set up through third-party malware loader Win/TrojanDownloader.Rugmi.
Ideas for safeguarding towards such malware threats
It’s extremely beneficial to all the time preserve working techniques and their software program updated and patched to keep away from being compromised by any widespread vulnerability that might result in malware an infection. And, customers ought to by no means be allowed to obtain and set up software program with out correct evaluation from the group’s IT staff.
Android SpinOk SDK is a spy ware standout
A cell advertising and marketing software program growth package recognized because the SpinOk spy ware by ESET climbed to being the seventh most detected Android risk for H2 2023 and essentially the most prevalent sort of spy ware for the interval.
The SpinOk SDK supplied builders a gaming platform meant to monetize software site visitors. A number of builders included the SDK of their apps, together with apps already accessible on official Android marketplaces. As soon as operating, the appliance begins to behave as spy ware and connects to a command & management server earlier than beginning to extract information from the Android gadget, together with probably delicate clipboard content material, in line with ESET.
The malicious code has options to attempt to keep undetected. It makes use of the gadget’s gyroscope and magnetometer to find out whether it is operating in a digital or lab atmosphere; if that’s the case, it modifications its habits in an try to keep away from being detected by researchers.
The SDK has been included into varied reputable Android purposes. In actual fact, 101 Android apps have used the malicious SDK, with greater than 421 million cumulated downloads, as reported in Might 2023 by cybersecurity firm Physician Internet, who contacted Google; then, Google eliminated all these purposes from the Google Play Retailer. The corporate accountable for SpinOk contacted Physician Internet and up to date its module to model 2.4.2, which eliminated all of the spy ware options.
An organization referred to as Roaster Earn defined how they ended up putting in the SDK in their very own software. Mainly, they’ve been approached by the OkSpin firm accountable for the SpinOk SDK with a “income development program,” which they accepted, earlier than Google notified them of their app elimination as a result of it contained spy ware. This case as soon as is as soon as once more a reminder of the complicated drawback of incorporating third-party code in software program that’s more and more abused by cybercriminals.
The right way to mitigate the danger of utilizing third-party code in software program
- Analyze the third-party code for any anomalies, when attainable. This would possibly assist to keep away from falling for code containing malicious content material or functionalities.
- Use static evaluation instruments to detect potential vulnerabilities or habits.
- Monitor community site visitors for any suspicious or surprising site visitors.
- Scrutinize the repute of the code supplier and suggestions in regards to the group, in addition to safety certifications or audits the supplier would possibly share.
Disclosure: I work for Pattern Micro, however the views expressed on this article are mine.