Cisco Talos analyzed the highest 14 ransomware teams between 2023 and 2024 to show their assault chain and spotlight attention-grabbing Techniques,Strategies and Protocols. The safety firm additionally uncovered essentially the most leveraged vulnerabilities being triggered by ransomware actors.
Ransomware assault chain: What Cisco Talos researchers realized
Ransomware actors practically all use the identical assault chain.
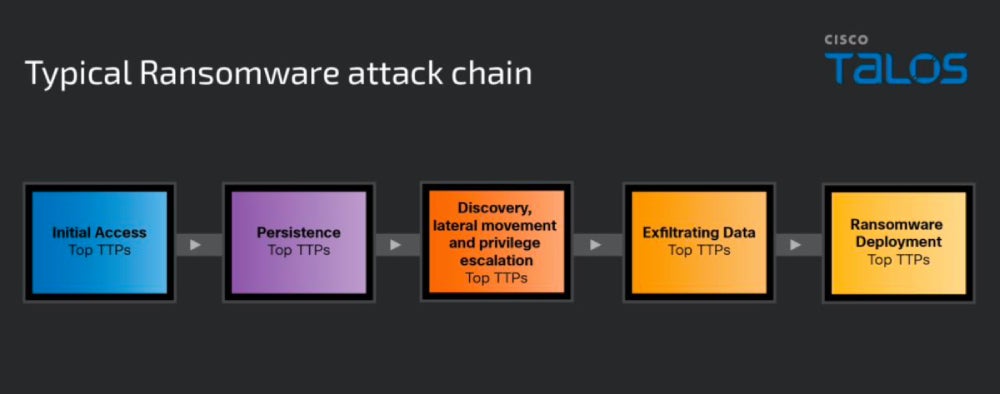
The 1st step for ransomware actors
Step one for the menace actor consists of having access to the focused entity. To realize that purpose, ransomware actors use completely different strategies — one of the vital frequent strategies is to social engineer their targets by sending emails containing malicious recordsdata or hyperlinks that can run malware on the focused system. The malware will then enable the attacker to deploy extra instruments and malware to succeed in their objectives. Multifactor authentication may be bypassed at the moment utilizing numerous strategies, both due to poor MFA implementation or due to proudly owning legitimate credentials already.
Talos additionally reported that an rising variety of ransomware associates scan internet-facing techniques for vulnerabilities or misconfigurations that might enable them to compromise the system. Unpatched or legacy software program is a very excessive danger.
Step two for ransomware actors
The second step is to achieve persistence in case the preliminary vector of compromise will get found; that persistence on techniques is usually achieved by modifying Home windows registry keys or enabling autostart execution of the malicious code upon system boot. Native, area and/or cloud accounts may additionally be created for persistence.
Step three for ransomware actors
Within the third step, the menace actor scans the community atmosphere to get a greater understanding of the inside components of the infrastructure. Information of worth that can be utilized for ransom is recognized at this step. To efficiently entry all components of the community, attackers usually use instruments to raise their privileges to administrator degree, along with utilizing instruments that enable community scanning. Widespread instruments for these duties are Residing Off the Land binaries AKA LOLbins, as a result of they’re executable recordsdata native to the working system and fewer inclined to boost alerts.
Step 4 for ransomware actors
The attacker is able to gather and steal delicate information, which they usually compress with utilities (equivalent to 7-Zip or WinRAR) earlier than exfiltrating the info to attacker-controlled servers through the use of Distant Monitoring and Administration instruments or extra customized ones, equivalent to StealBit or Exabyte for instance, created by LockBit and BlackByte ransomware teams.
Attainable step 5 for ransomware actors
If the purpose is information theft or extortion, the operation is over. If the purpose is to encrypt information, the attacker wants to check the ransomware within the atmosphere — that’s, checking the supply mechanisms and the communications between the ransomware and the C2 server — earlier than launching it to encrypt the community and notify the sufferer they’ve been breached and have to pay the ransom.
Three most abused vulnerabilities
Cisco Talos reported that three vulnerabilities on public-facing purposes are generally exploited by ransomware menace actors.
- CVE-2020-1472 AKA Zerologon exploits a flaw within the Netlogon Distant Protocol that permits attackers to bypass authentication and alter laptop passwords inside a site controller’s Lively Listing. This exploit is broadly utilized by ransomware actors as a result of it allows them to achieve entry to a community with out authentication.
- CVE-2018-13379, a Fortinet FortiOS SSL VPN vulnerability, allows path traversal that permits an attacker to entry system recordsdata by sending specifically crafted HTTP packets. VPN session tokens may be accessed this fashion, which can be utilized to achieve unauthenticated entry to the community.
- CVE-2023-0669, a GoAnywhere MFT vulnerability, permits attackers to execute arbitrary code on a focused server that makes use of the GoAnywhere Managed File Switch software program. That is the newest vulnerability listed by Cisco Talos in its report.
All these vulnerabilities enable ransomware actors to get preliminary entry and manipulate techniques to run extra malicious payloads, set up persistence or facilitate lateral actions inside compromised networks.
DOWNLOAD: Cybersecurity’s Advantages and Greatest Practices from TechRepublic Premium
Notable TTPs of 14 ransomware teams
Cisco Talos noticed the TTPs utilized by 14 of essentially the most prevalent ransomware teams primarily based on their quantity of assault, influence to prospects and atypical conduct.

One of many key findings concerning the TTPs signifies lots of the most outstanding teams prioritize establishing preliminary compromise and evading defenses of their assault chains.
Ransomware menace actors usually obfuscate their malicious code by packing and compressing it and modify the techniques registry to disable safety alerts on the endpoint or server. They could additionally block sure restoration choices for the customers.
The Cisco Talos researchers highlighted that essentially the most prevalent credential entry approach is the dumping of the LSASS reminiscence contents to extract plaintext passwords, hashed passwords or authentication tokens saved in reminiscence.
One other pattern in C2 actions is the usage of commercially accessible instruments equivalent to RMM purposes. These purposes are usually trusted by the atmosphere and permit the attacker to mix in with the company community site visitors.
Find out how to mitigate the ransomware menace
For starters, it’s obligatory to use patches and updates to all techniques and software program; this fixed upkeep is important to cut back the danger of being compromised by an exploit.
Strict password insurance policies and MFA have to be carried out. Complicated and distinctive passwords have to be set for each person and MFA enforced, so an attacker possessing legitimate credentials remains to be not capable of entry the focused community.
Greatest practices to harden all techniques and environments must be utilized. Pointless companies and options must be disabled to cut back the assault floor. Additionally, publicity to the web have to be lowered by limiting the variety of public-facing companies as a lot as potential.
Networks must be segmented utilizing VLANs or comparable applied sciences. Delicate information and techniques have to be remoted from different networks to stop lateral actions from an attacker.
Endpoints have to be monitored by a Safety Data and Occasion Administration system, and Endpoint Detection and Response or Prolonged Detection and Response instruments must be deployed.
Disclosure: I work for Pattern Micro, however the views expressed on this article are mine.