The Sophos X-Ops Incident Response staff has been analyzing the ways of a ransomware group known as Mad Liberator. This can be a pretty new menace actor, first rising in mid-July 2024. On this article, we’ll have a look at sure strategies the group is utilizing, involving the favored remote-access software Anydesk. We’ll doc the fascinating social-engineering ways the group has used and supply steering each as to tips on how to reduce your danger of turning into a sufferer and, for investigators, to tips on how to see potential exercise by this group.
Earlier than we begin, we should always be aware that Anydesk is reliable software program that the attackers are abusing on this state of affairs. The attackers misuse that software within the method we’ll present under, however presumably any distant entry program would go well with their functions. Additionally, we’ll be aware up entrance that SophosLabs has a detection in place, Troj/FakeUpd-Ok, for the binary described.
What’s Mad Liberator?
The exercise that Sophos X-Ops has noticed to date signifies that Mad Liberator focuses on information exfiltration; in our personal expertise, we have now not but seen any incidents of knowledge encryption traceable to Mad Liberator. That stated, info on watchguard.com does counsel that the group makes use of encryption sometimes, and in addition undertakes double extortion (stealing information, then encrypting the sufferer’s programs and threatening to launch the stolen information if the sufferer doesn’t pay to decrypt).
Typical of menace actors who carry out information exfiltration, Mad Liberator operates a leak web site on which it publishes sufferer particulars, in an effort to place extra stress on victims to pay. The positioning claims that the information could be downloaded “without cost.”
Determine 1: Mad Liberator’s disclosure web site
Apparently, Mad Liberator makes use of social engineering strategies to acquire surroundings entry, focusing on victims who use distant entry instruments put in on endpoints and servers. Anydesk, as an example, is popularly utilized by IT groups to handle their environments, significantly when working with distant customers or gadgets.
How the assault works
Anydesk works by allocating a novel ID, on this a case a ten-digit deal with, to every gadget it’s put in on. As soon as the appliance is put in on a tool, a consumer can both request to entry a distant gadget to take management by coming into the ID, or a consumer can invite one other consumer to take management of their gadget by way of a distant session.
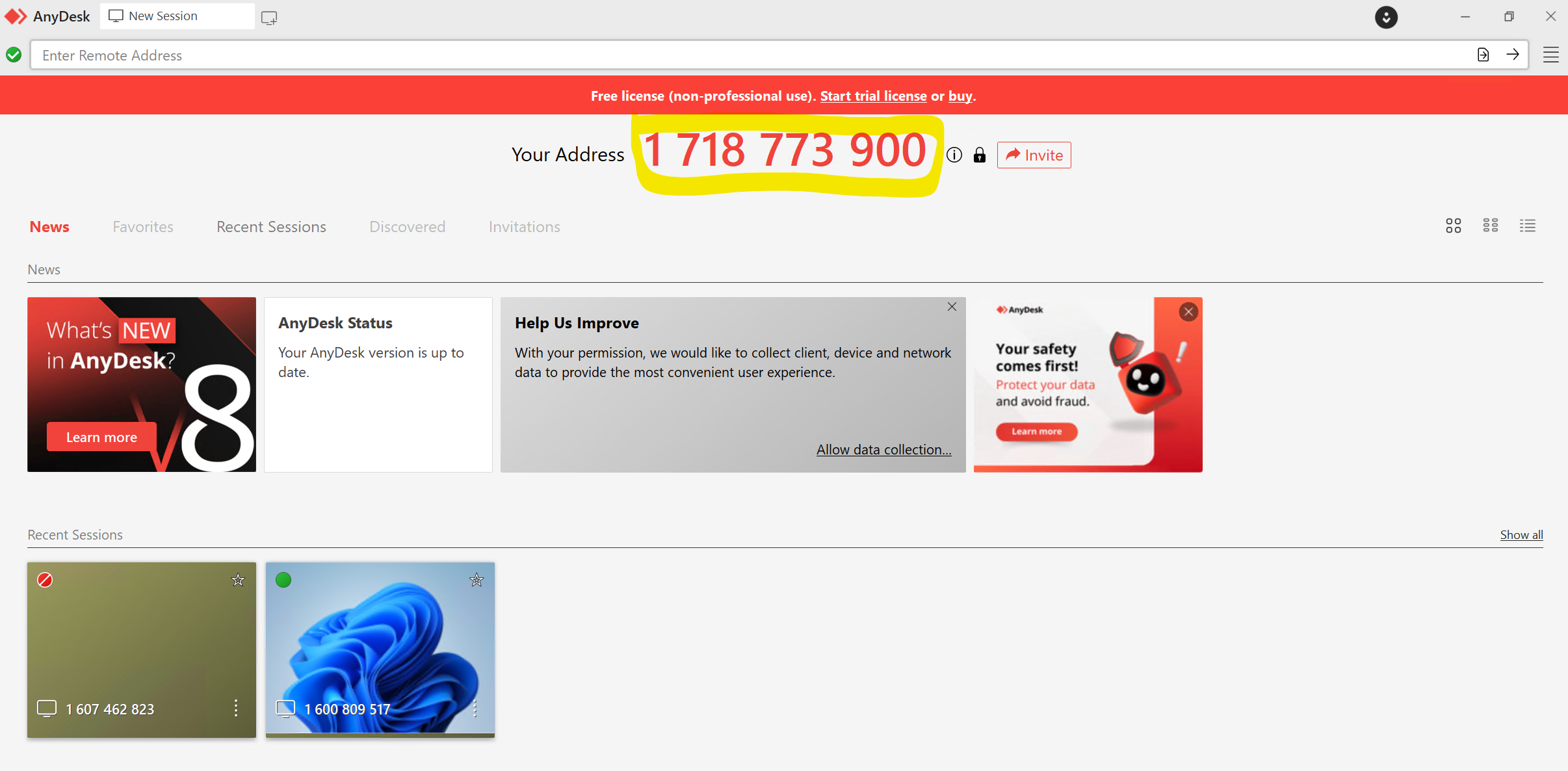
Determine 2: An Anydesk session with the ten-digit deal with prominently displayed
We don’t know at this level how, or if, the attacker targets a specific Anydesk ID. In idea it’s attainable to simply cycle by way of potential addresses till somebody accepts a connection request; nonetheless, with probably 10 billion 10-digit numbers, this appears considerably inefficient. In an occasion that the Incident Response staff investigated, we discovered no indications of any contact between the Mad Liberator attacker and the sufferer previous to the sufferer receiving an unsolicited Anydesk connection request. The consumer was not a outstanding or publicly seen member of workers and there was no identifiable purpose for them to be particularly focused.
When an Anydesk connection request is acquired, the consumer sees the pop-up proven in Determine 3. The consumer should authorize the connection earlier than it may be totally established.
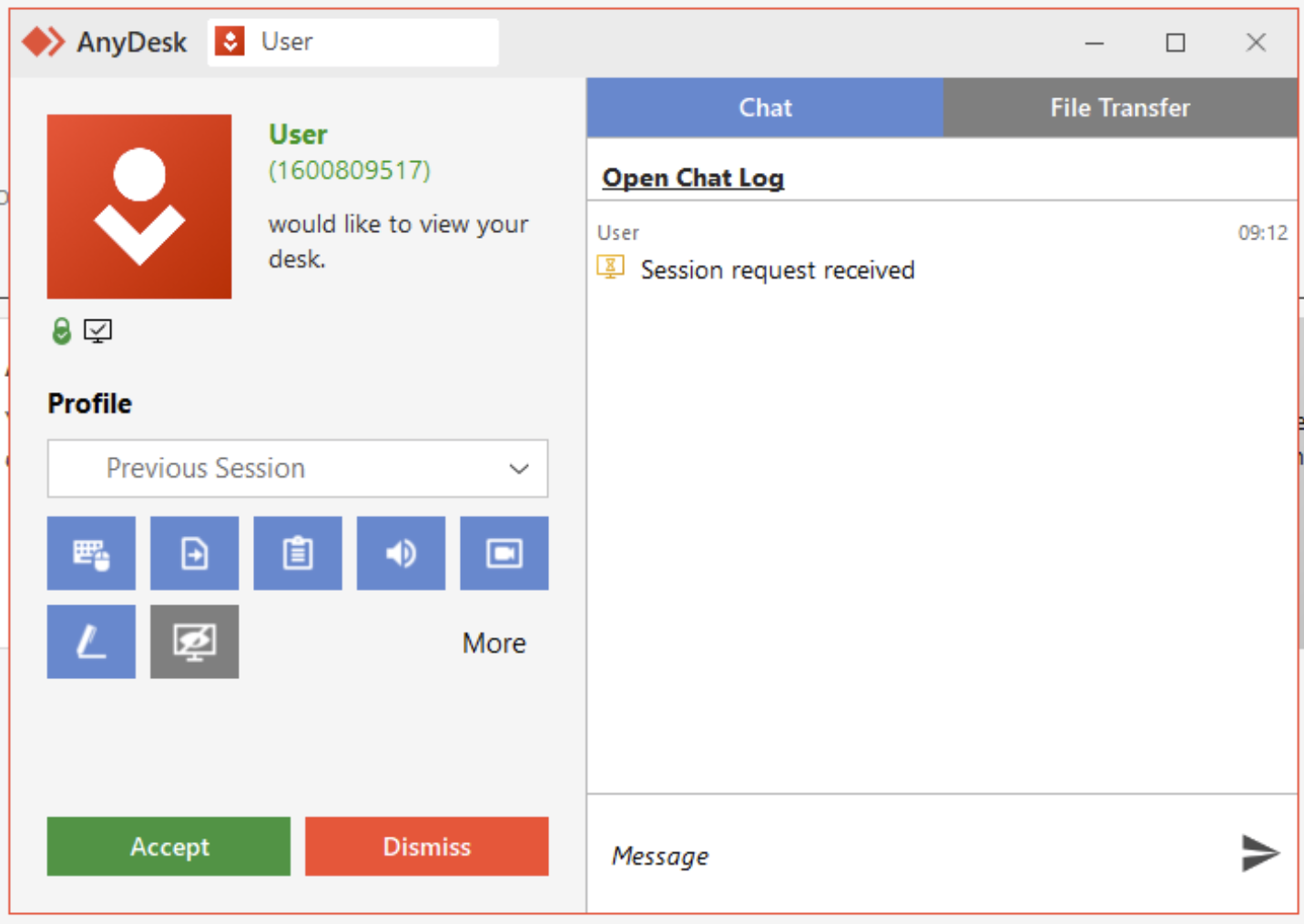
Determine 3: A request from “Consumer” to attach by way of Anydesk; as Anydesk admins know however finish customers could not, anybody can select any username when organising Anydesk, so an attacker may even name itself “Tech Help” or one thing comparable
Within the case our IR staff dealt with, the sufferer was conscious that Anydesk was utilized by their firm’s IT division. They due to this fact assumed that the incoming connection request was only a ordinary occasion of the IT division performing upkeep, and so clicked Settle for.
As soon as the connection was established, the attacker transferred a binary to the sufferer’s gadget and executed it. In our investigations this file has been titled “Microsoft Home windows Replace,” with the SHA256 hash:
f4b9207ab2ea98774819892f11b412cb63f4e7fb4008ca9f9a59abc2440056fe
This binary was a quite simple program that displayed a splash display mimicking a Home windows Replace display. The display was animated, making it seem that the system was updating, as proven in Determine 4.
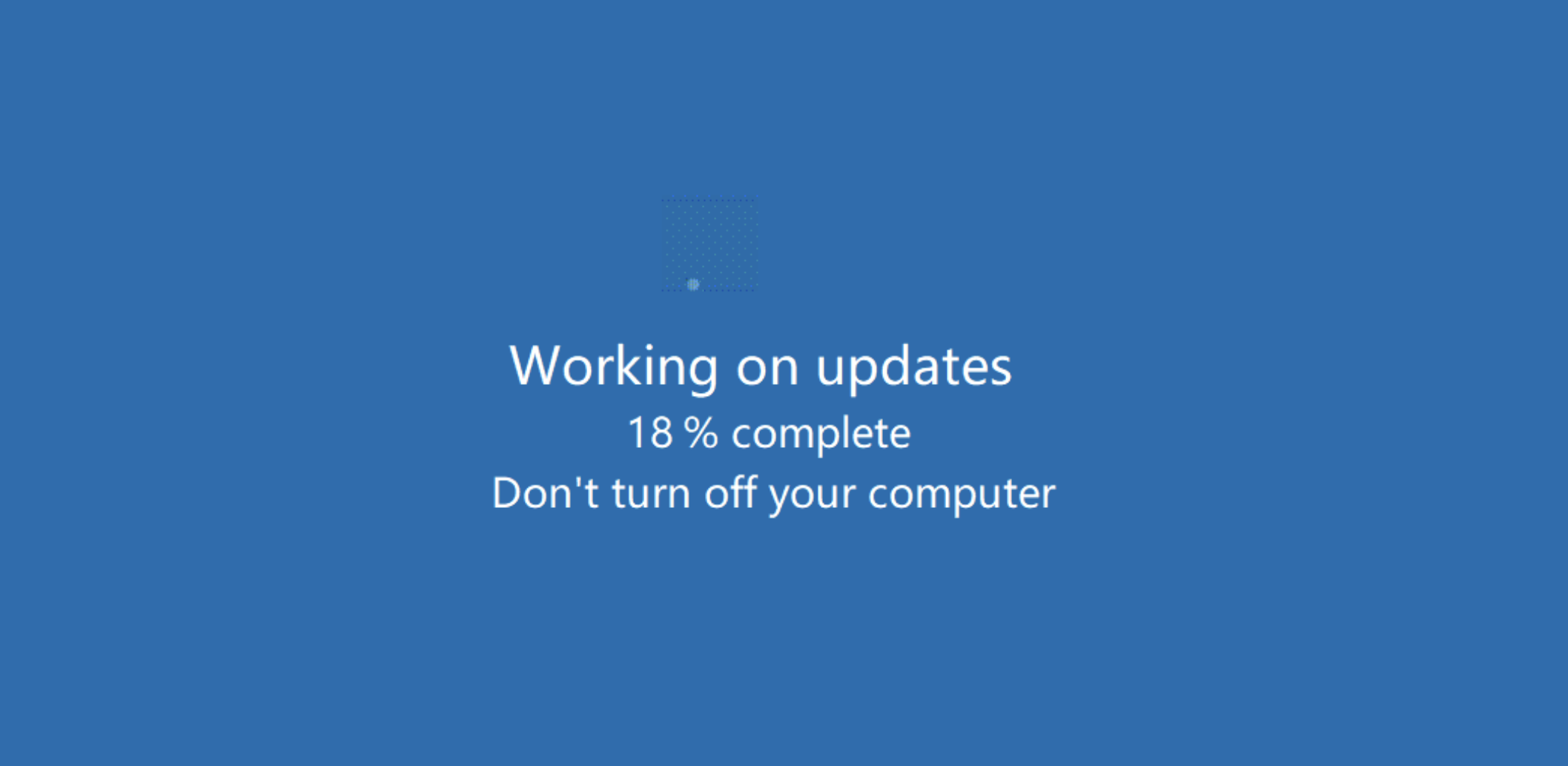
Determine 4: An all-too-unremarkable Home windows Replace display… or is it?
This program didn’t carry out some other exercise, which made it unlikely to be instantly detected as malicious by most antimalware packages. (Sophos has developed a detection [Troj/FakeUpd-K] for this explicit binary and can proceed to watch developments on this.)
At this level, to guard the ruse from being found and stopped, the attacker took an additional step. Since this straightforward program may have been exited ought to the consumer occur to press the “Esc” key, the attacker utilized a function inside Anydesk to disable enter from the consumer’s keyboard and mouse.
For the reason that sufferer was now not ready to make use of their keyboard, and for the reason that above display seemed to be one thing unremarkable to any Home windows consumer, they had been unaware of the exercise that the attacker was performing within the background – and couldn’t have stopped it simply even when they had been suspicious.
The attacker proceeded to entry the sufferer’s OneDrive account, which was linked to the gadget, in addition to information that had been saved on a central server and accessible by way of a mapped community share. Utilizing the Anydesk FileTransfer facility, the attacker stole and exfiltrated these firm information. The attacker then used Superior IP Scanner to find out if there have been different gadgets of curiosity that might be exploited inside the similar subnet. (They didn’t, ultimately, laterally transfer to some other gadgets.)
As soon as the stolen information had been beneath its management, the attacker then ran one other program that created quite a few ransom notes. Apparently, these ransom notes had been generated in a number of areas on a shared community location which was mapped to the gadget, relatively than on the sufferer’s gadget itself. These ransom notes introduced that information had been stolen and offered particulars as to how the sufferer ought to pay the ransom to stop disclosure of these stolen information. (Ways comparable to these shall be all too acquainted to readers of our investigation of stress ways presently in use by ransomware gangs.)
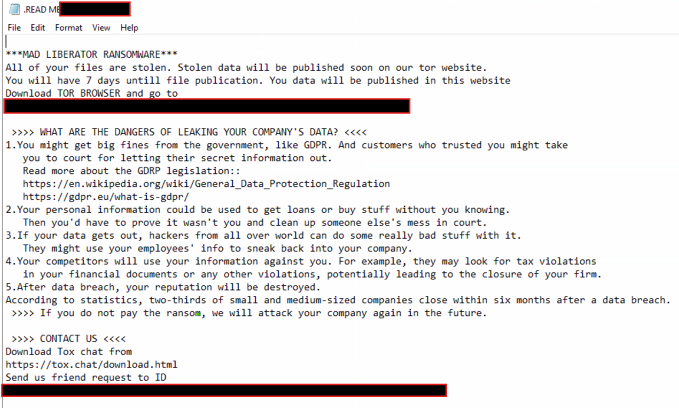 Determine 5: The ransom be aware acquired by the sufferer; be aware the threats of reputational and regulatory harm, and be aware additionally that no ransom quantity is cited
Determine 5: The ransom be aware acquired by the sufferer; be aware the threats of reputational and regulatory harm, and be aware additionally that no ransom quantity is cited
The faux Home windows Replace display shielded the attacker’s actions from being seen on the sufferer’s display. The assault lasted virtually 4 hours, on the conclusion of which the attacker terminated the faux replace display and ended the Anydesk session, giving management of the gadget again to the sufferer. We did be aware that the binary was manually triggered by the attacker; with no scheduled activity or automation in place to execute it once more as soon as the menace actor was gone, the file merely remained on the affected system.
Classes and mitigations
This was an easy assault that relied on the sufferer believing that the Anydesk request was a part of day-to-day exercise. So far as our investigators may decide, the assault didn’t contain any extra social engineering efforts by the attacker — no electronic mail contact, no phishing makes an attempt, and so forth. As such it highlights the significance of ongoing, up-to-date workers coaching, and it signifies that organizations ought to set and make recognized a transparent coverage relating to how IT departments will contact and prepare distant classes.
Past consumer schooling, we extremely advocate that directors implement the Anydesk Entry Management Lists to solely permit connections from particular gadgets so as to significantly reduce the danger of the sort of assault, AnyDesk present some very precious steering and the way to do that in addition to extra safety measures within the following hyperlink:
With extra recommendation accessible right here:
Procedural notes for investigators observe the conclusion of this text.
Conclusion
Ransomware teams rise and fall continuously, and Mad Liberator could show to be a big new participant, or simply one other flash within the pan. Nevertheless, the social-engineering ways the group used within the case described above are noteworthy – however they don’t seem to be distinctive. Attackers will at all times proceed to develop and make use of a wide range of ways to attempt to exploit each the human component and the technical safety layers.
It may be a tough activity to stability safety towards usability when implementing instruments inside an surroundings, particularly when these instruments assist facilitate distant entry for the very individuals tasked with caring for business-critical programs. Nevertheless, we at all times advocate that when functions are deployed throughout a community, particularly ones that may be leveraged to acquire distant entry to gadgets, that cautious overview of the safety suggestions by the seller is taken into account. The place these suggestions aren’t adopted, that selection must be documented as a part of your danger administration course of in order that it may be regularly reviewed, or so different mitigations could be put in place to make sure it stays inside the danger urge for food of your group.
Appendix: Investigating Mad Liberator
In case you are investigating an incident during which you watched that attackers could have leveraged Anydesk, search for helpful occasion and connection information saved within the following information:
- C:ProgramDataAnyDeskconnection_trace.txt
- C:ProgramDataAnyDeskad_svc.hint
- C:UserspercentAppDataRoamingAnyDeskad.hint
The connection_trace.txt file solely accommodates the Tackle ID of current connections and will not be all that helpful by itself. But it surely does a minimum of can help you slim down the offending ID.
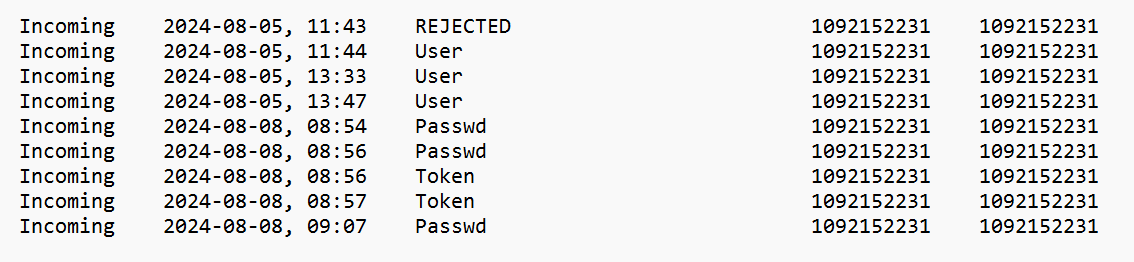
Determine 6: A have a look at connection_trace.txt, with info on the results of every occasion
There are 4 attainable states for every connection:
- REJECTED – the end-user rejected a connection request
- Consumer – the end-user accepted a connection request
- Passwd – password entered by the distant system to realize entry
- Token – ‘Login Routinely’ choice checked by the distant system
The ad_svc.hint and advert.hint information include numerous granular element. These could be opened and considered with a textual content editor comparable to Notepad and together with different occasions additionally accommodates connection information. The ad_svc.hint file accommodates particulars of the supply IP addresses of distant connections.
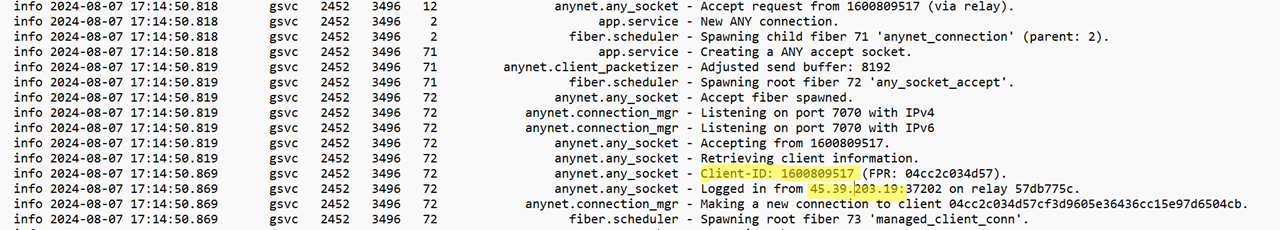
Determine 7: A have a look at ad_svc.hint; a questionable connection is highlighted within the picture
The advert.hint file accommodates logs referring to file transfers, and occasions comparable to the place consumer enter is disabled.
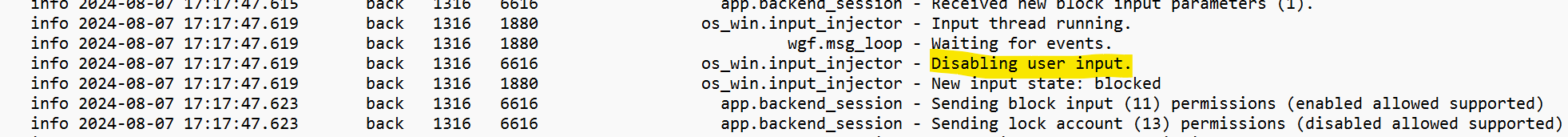
Determine 8: The consumer’s enter choices are disabled
![]()
Determine 9: The file-transfer occasions
Though the logs will point out the folder and what number of information had been transferred throughout information exfiltration, sadly the logs won’t element every file identify.
You probably have Sophos Intercept X put in, gathering this information is simplified. The next OSquery can be utilized inside Dwell Uncover within the Sophos Central Dashboard:
SELECT
strftime('%Y-%m-%dTpercentH:%M:%S', substr(grep.line, instr(grep.line, 'data') + 5, 19)) AS Datetime,
grep.path,
CASE
WHEN grep.sample = 'Logged in from' THEN 'Login'
WHEN grep.sample = 'Making ready information' THEN 'File Switch from this Host'
WHEN grep.sample = 'Accepting from' THEN 'Accepted Connection Request'
WHEN grep.sample = 'Incoming session request:' THEN 'Incoming Session Request'
WHEN grep.sample = 'Distant OS:' THEN 'Distant OS'
WHEN grep.sample = 'Disabling consumer enter.' THEN 'Disable Mouse and Keyboard'
WHEN grep.sample = 'Obtain began' THEN 'File Switch to this Host'
WHEN grep.sample = 'Obtained a sysinfo request.' THEN 'System Data Request'
WHEN grep.sample = 'Authenticated with everlasting token' THEN 'Authenticated with Token'
WHEN grep.sample = 'Authenticated with appropriate passphrase' THEN 'Authenticated with Password'
WHEN grep.sample = 'Profile was used:' THEN 'Profile Assigned'
END AS 'Operation',
grep.line as Information
FROM file
CROSS JOIN grep ON (grep.path = file.path)
WHERE
(
file.path LIKE 'C:ProgramDataAnyDeskad_svc.hint'
OR file.path LIKE 'C:UserspercentAppDataRoamingAnyDeskad.hint'
)
AND
(
--AnyDesk
grep.sample = 'Logged in from'
OR grep.sample = 'Making ready information'
OR grep.sample = 'Accepting from'
OR grep.sample = 'Incoming session request:'
OR grep.sample = 'Distant OS:'
OR grep.sample = 'Disabling consumer enter.'
OR grep.sample = 'Obtain began'
OR grep.sample = 'Obtained a sysinfo request.'
OR grep.sample = 'Authenticated with everlasting token'
OR grep.sample = 'Authenticated with appropriate passphrase'
OR grep.sample = 'Profile was used:'
)
ORDER BY Datetime DESC
The question even helps to type the info right into a usable desk, as seen in Determine 10.
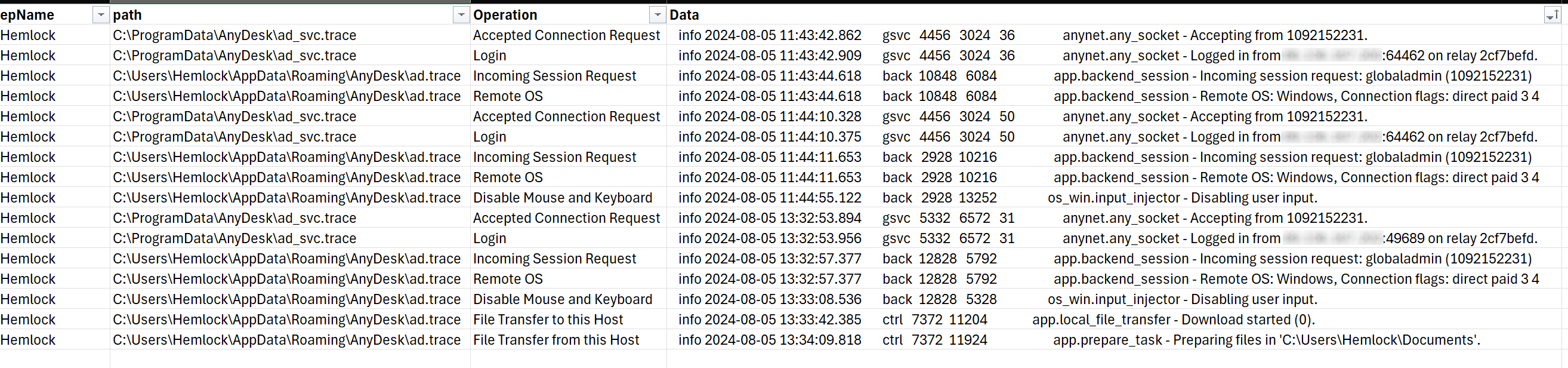
Determine 10: The output of the OSquery proven above, in helpful tabular format
Acknowledgements
Harshal Gosalia, Ollie Jones, and Andy French contributed to this analysis.










