A cybercrook who has been establishing web sites that mimic the self-destructing message service privnote.com by accident uncovered the breadth of their operations lately once they threatened to sue a software program firm. The disclosure revealed a worthwhile community of phishing websites that behave and appear to be the actual Privnote, besides that any messages containing cryptocurrency addresses shall be routinely altered to incorporate a unique cost tackle managed by the scammers.
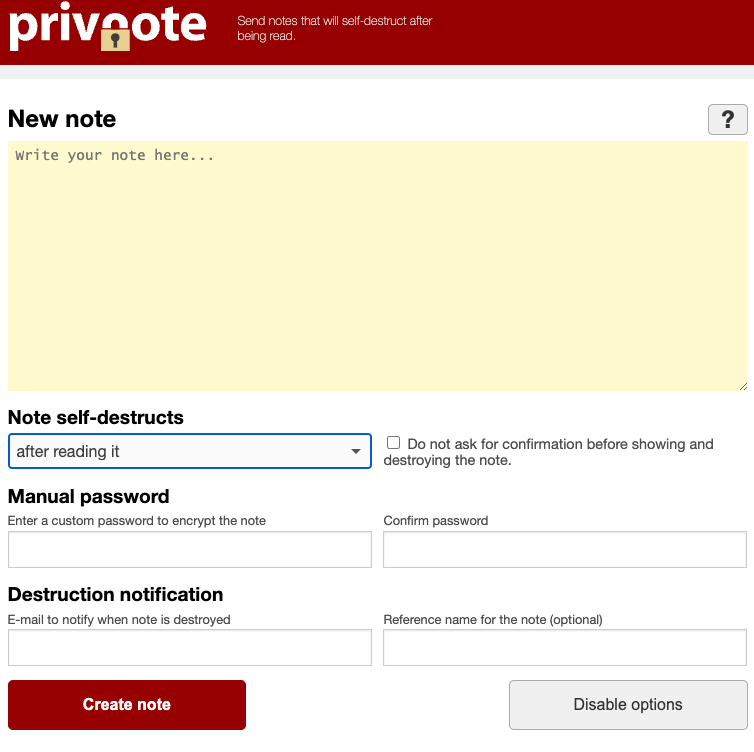
The true Privnote, at privnote.com.
Launched in 2008, privnote.com employs know-how that encrypts every message in order that even Privnote itself can not learn its contents. And it doesn’t ship or obtain messages. Making a message merely generates a hyperlink. When that hyperlink is clicked or visited, the service warns that the message shall be gone perpetually after it’s learn.
Privnote’s ease-of-use and recognition amongst cryptocurrency lovers has made it a perennial goal of phishers, who erect Privnote clones that operate roughly as marketed but in addition quietly inject their very own cryptocurrency cost addresses when a word is created that comprises crypto wallets.
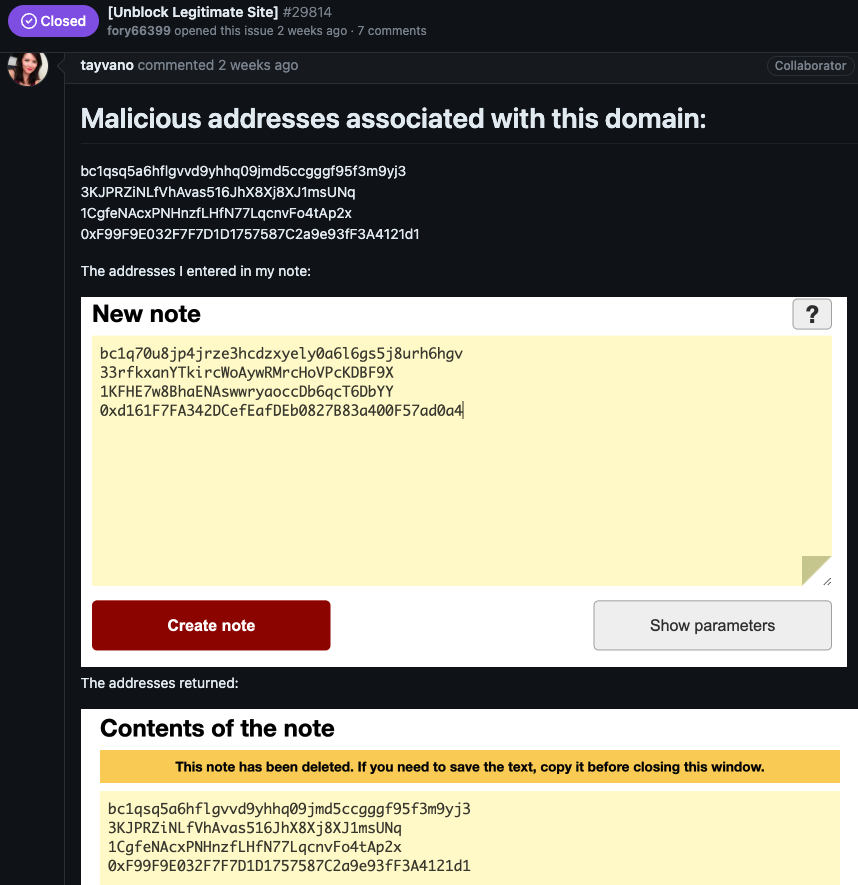
Final month, a brand new consumer on GitHub named fory66399 lodged a criticism on the “points” web page for MetaMask, a software program cryptocurrency pockets used to work together with the Ethereum blockchain. Fory66399 insisted that their web site — privnote[.]co — was being wrongly flagged by MetaMask’s “eth-phishing-detect” listing as malicious.
“We filed a lawsuit with a lawyer for dishonestly including a web site to the block listing, damaging status, in addition to ignoring the moderation division and ignoring solutions!” fory66399 threatened. “Present proof or I’ll demand compensation!”
MetaMask’s lead product supervisor Taylor Monahan replied by posting a number of screenshots of privnote[.]co displaying the positioning did certainly swap out any cryptocurrency addresses.
After being advised the place they might ship a duplicate of their lawsuit, Fory66399 appeared to change into flustered, and proceeded to say various different attention-grabbing domains:
You despatched me screenshots from another web site! It’s pink!!!!
The tornote.io web site has a unique colour altogether
The privatenote,io web site additionally has a unique colour! What’s incorrect?????
A search at DomainTools.com for privatenote[.]io reveals it has been registered to 2 names over as a few years, together with Andrey Sokol from Moscow and Alexandr Ermakov from Kiev. There isn’t a indication these are the actual names of the phishers, however the names are helpful in pointing to different websites focusing on Privnote since 2020.
DomainTools says different domains registered to Alexandr Ermakov embrace pirvnota[.]com, privatemessage[.]internet, privatenote[.]io, and tornote[.]io.
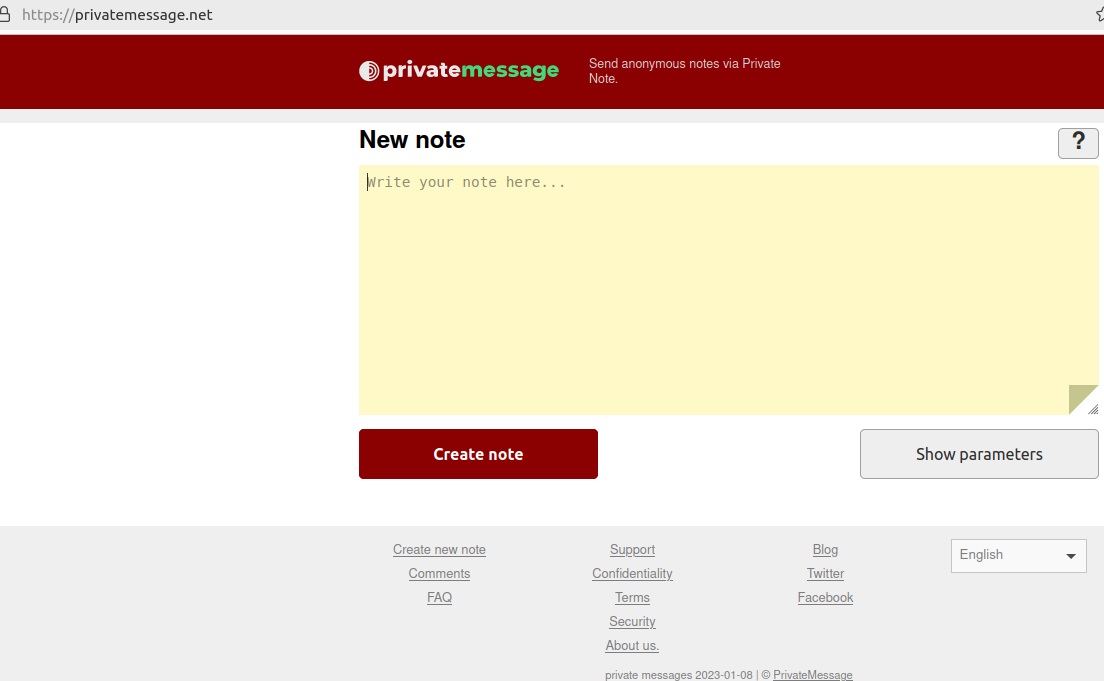
A screenshot of the phishing area privatemessage dot internet.
The registration information for pirvnota[.]com at one level had been up to date from Andrey Sokol to “BPW” because the registrant group, and “Tambov district” within the registrant state/province subject. Looking out DomainTools for domains that embrace each of those phrases reveals pirwnote[.]com.
Different Privnote phishing domains that additionally phoned house to the identical Web tackle as pirwnote[.]com embrace privnode[.]com, privnate[.]com, and prevnóte[.]com. Pirwnote[.]com is presently promoting safety cameras made by the Chinese language producer Hikvision, by way of an Web tackle primarily based in Hong Kong.
It seems somebody has gone to nice lengths to make tornote[.]io appear to be a reputable web site. For instance, this account at Medium has authored greater than a dozen weblog posts prior to now yr singing the praises of Tornote as a safe, self-destructing messaging service. Nonetheless, testing reveals tornote[.]io will even change any cryptocurrency addresses in messages with their very own cost tackle.
These malicious word websites appeal to guests by gaming search engine outcomes to make the phishing domains seem prominently in search outcomes for “privnote.” A search in Google for “privnote” presently returns tornote[.]io because the fifth outcome. Like different phishing websites tied to this community, Tornote will use the identical cryptocurrency addresses for roughly 5 days, after which rotate in new cost addresses.
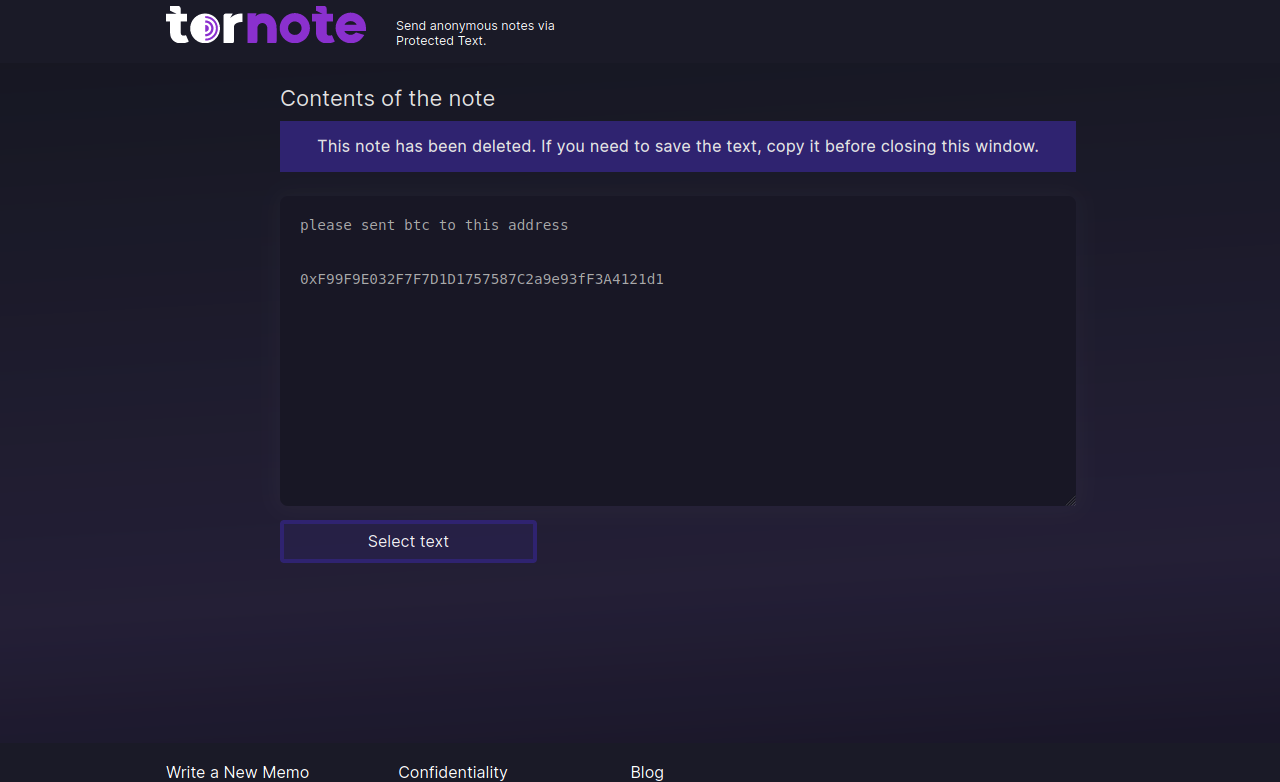
Tornote modified the cryptocurrency tackle entered right into a take a look at word to this tackle managed by the phishers.
All through 2023, Tornote was hosted with the Russian supplier DDoS-Guard, on the Web tackle 186.2.163[.]216. A overview of the passive DNS information tied to this tackle reveals that aside from subdomains devoted to tornote[.]io, the primary different area at this tackle was hkleaks[.]ml.
In August 2019, a slew of internet sites and social media channels dubbed “HKLEAKS” started doxing the identities and private data of pro-democracy activists in Hong Kong. Based on a report (PDF) from Citizen Lab, hkleaks[.]ml was the second area that appeared because the perpetrators started to broaden the listing of these doxed.

HKleaks, as listed by The Wayback Machine.
DomainTools reveals there are greater than 1,000 different domains whose registration information embrace the group title “BPW” and “Tambov District” as the situation. Nearly all of these domains had been registered by means of one among two registrars — Hong Kong-based Nicenic and Singapore-based WebCC — and nearly all seem like phishing or pill-spam associated.
Amongst these is rustraitor[.]information, a web site erected after Russia invaded Ukraine in early 2022 that doxed Russians perceived to have helped the Ukrainian trigger.
An archive.org copy of Rustraitor.
In line with the general theme, these phishing domains seem targeted on stealing usernames and passwords to a few of the cybercrime underground’s busiest outlets, together with Brian’s Membership. What do all of the phished websites have in frequent? All of them settle for cost by way of digital currencies.
It seems MetaMask’s Monahan made the proper resolution in forcing these phishers to tip their hand: Among the many web sites at that DDoS-Guard tackle are a number of MetaMask phishing domains, together with metarrnask[.]com, meternask[.]com, and rnetamask[.]com.
How worthwhile are these non-public word phishing websites? Reviewing the 4 malicious cryptocurrency cost addresses that the attackers swapped into notes handed by means of privnote[.]co (as pictured in Monahan’s screenshot above) reveals that between March 15 and March 19, 2024, these tackle raked in and transferred out almost $18,000 in cryptocurrencies. And that’s simply one among their phishing web sites.










