U.S. and U.Okay. authorities have seized the darknet web sites run by LockBit, a prolific and damaging ransomware group that has claimed greater than 2,000 victims worldwide and extorted over $120 million in funds. As a substitute of itemizing information stolen from ransomware victims who didn’t pay, LockBit’s sufferer shaming web site now gives free restoration instruments, in addition to information about arrests and prison prices involving LockBit associates.
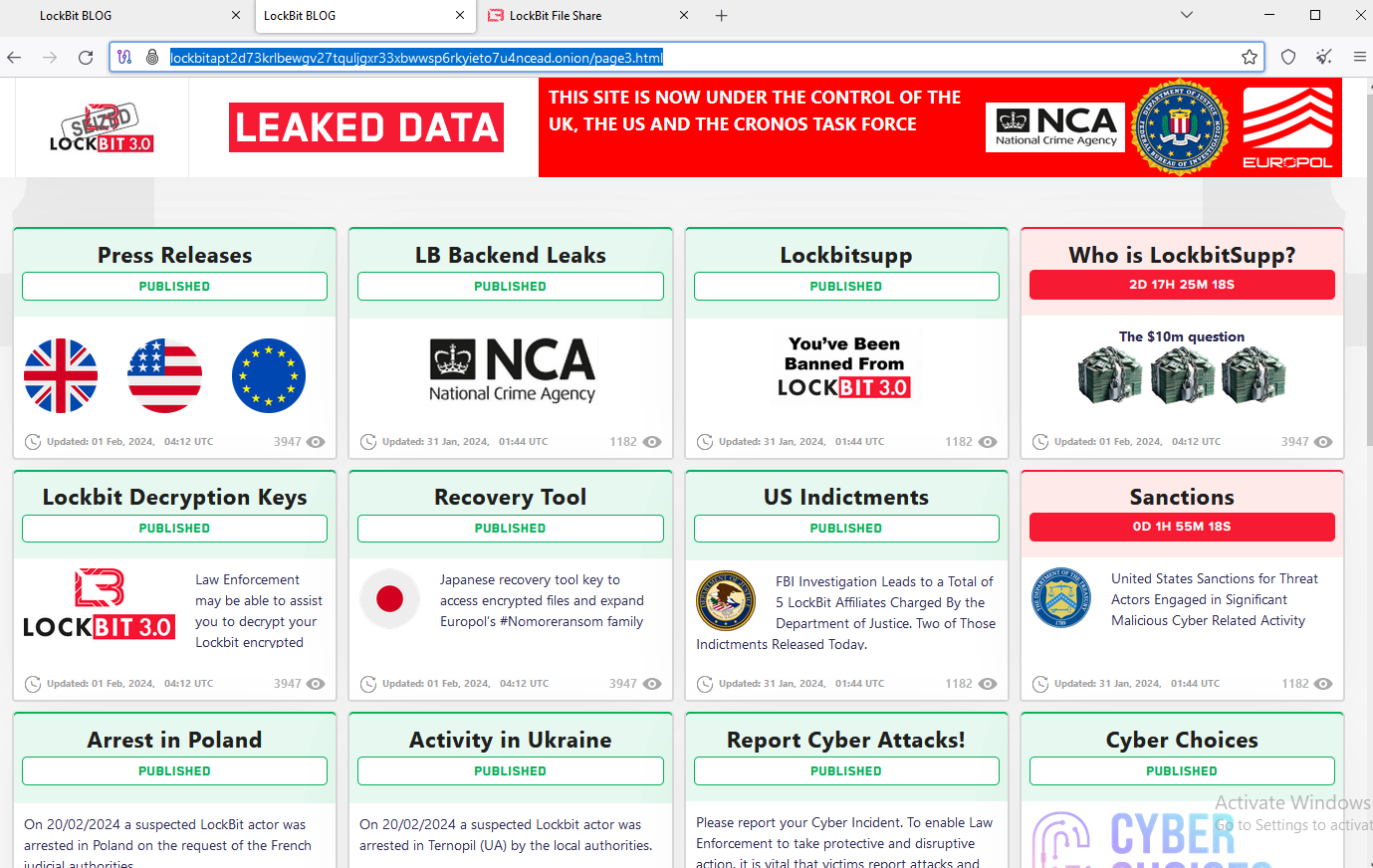
Investigators used the present design on LockBit’s sufferer shaming web site to function press releases and free decryption instruments.
Dubbed “Operation Cronos,” the regulation enforcement motion concerned the seizure of practically three-dozen servers; the arrest of two alleged LockBit members; the unsealing of two indictments; the discharge of a free LockBit decryption device; and the freezing of greater than 200 cryptocurrency accounts regarded as tied to the gang’s actions.
LockBit members have executed assaults in opposition to 1000’s of victims in america and world wide, in response to the U.S. Division of Justice (DOJ). First surfacing in September 2019, the gang is estimated to have made a whole bunch of thousands and thousands of U.S. {dollars} in ransom calls for, and extorted over $120 million in ransom funds.
LockBit operated as a ransomware-as-a-service group, whereby the ransomware gang takes care of the whole lot from the bulletproof internet hosting and domains to the event and upkeep of the malware. In the meantime, associates are solely accountable for discovering new victims, and might reap 60 to 80 % of any ransom quantity finally paid to the group.
A press release on Operation Cronos from the European police company Europol mentioned the months-long infiltration resulted within the compromise of LockBit’s major platform and different crucial infrastructure, together with the takedown of 34 servers within the Netherlands, Germany, Finland, France, Switzerland, Australia, america and the UK. Europol mentioned two suspected LockBit actors have been arrested in Poland and Ukraine, however no additional info has been launched about these detained.
The DOJ right now unsealed indictments in opposition to two Russian males alleged to be lively members of LockBit. The federal government says Russian nationwide Artur Sungatov used LockBit ransomware in opposition to victims in manufacturing, logistics, insurance coverage and different corporations all through america.
Ivan Gennadievich Kondratyev, a.ok.a. “Bassterlord,” allegedly deployed LockBit in opposition to targets in america, Singapore, Taiwan, and Lebanon. Kondratyev can also be charged (PDF) with three prison counts arising from his alleged use of the Sodinokibi (aka “REvil“) ransomware variant to encrypt information, exfiltrate sufferer info, and extort a ransom cost from a company sufferer primarily based in Alameda County, California.
With the indictments of Sungatov and Kondratyev, a complete of 5 LockBit associates now have been formally charged. In Might 2023, U.S. authorities unsealed indictments in opposition to two alleged LockBit associates, Mikhail “Wazawaka” Matveev and Mikhail Vasiliev.
Vasiliev, 35, of Bradford, Ontario, Canada, is in custody in Canada awaiting extradition to america (the criticism in opposition to Vasiliev is at this PDF). Matveev stays at giant, presumably nonetheless in Russia. In January 2022, KrebsOnSecurity revealed Who’s the Community Entry Dealer ‘Wazawaka,’ which adopted clues from Wazawaka’s many pseudonyms and phone particulars on the Russian-language cybercrime boards again to a 31-year-old Mikhail Matveev from Abaza, RU.

An FBI wished poster for Matveev.
In June 2023, Russian nationwide Ruslan Magomedovich Astamirov was charged in New Jersey for his participation within the LockBit conspiracy, together with the deployment of LockBit in opposition to victims in Florida, Japan, France, and Kenya. Astamirov is presently in custody in america awaiting trial.
LockBit was recognized to have recruited associates that labored with a number of ransomware teams concurrently, and it’s unclear what impression this takedown could have on competing ransomware affiliate operations. The safety agency ProDaft mentioned on Twitter/X that the infiltration of LockBit by investigators offered “in-depth visibility into every affiliate’s constructions, together with ties with different infamous teams equivalent to FIN7, Wizard Spider, and EvilCorp.”
In a prolonged thread in regards to the LockBit takedown on the Russian-language cybercrime discussion board XSS, one of many gang’s leaders mentioned the FBI and the U.Okay.’s Nationwide Crime Company (NCA) had infiltrated its servers utilizing a recognized vulnerability in PHP, a scripting language that’s extensively utilized in Net growth.
A number of denizens of XSS questioned aloud why the PHP flaw was not flagged by LockBit’s vaunted “Bug Bounty” program, which promised a monetary reward to associates who might discover and quietly report any safety vulnerabilities threatening to undermine LockBit’s on-line infrastructure.
This prompted a number of XSS members to start out posting memes taunting the group in regards to the safety failure.
“Does it imply that the FBI offered a pentesting service to the associates program?,” one denizen quipped. “Or did they resolve to participate within the bug bounty program? :):)”
Federal investigators additionally seem like trolling LockBit members with their seizure notices. LockBit’s information leak website beforehand featured a countdown timer for every sufferer group listed, indicating the time remaining for the sufferer to pay a ransom demand earlier than their stolen recordsdata could be revealed on-line. Now, the highest entry on the shaming website is a countdown timer till the general public doxing of “LockBitSupp,” the unofficial spokesperson or figurehead for the LockBit gang.
In January 2024, LockBitSupp informed XSS discussion board members he was disenchanted the FBI hadn’t provided a reward for his doxing and/or arrest, and that in response he was putting a bounty on his personal head — providing $10 million to anybody who might uncover his actual identify.
“My god, who wants me?,” LockBitSupp wrote on Jan. 22, 2024. “There may be not even a reward out for me on the FBI web site. By the best way, I wish to use this opportunity to extend the reward quantity for an individual who can inform me my full identify from USD 1 million to USD 10 million. The one that will discover out my identify, inform it to me and clarify how they have been capable of finding it out will get USD 10 million. Please take be aware that when searching for criminals, the FBI makes use of unclear wording providing a reward of UP TO USD 10 million; because of this the FBI pays you USD 100, as a result of technically, it’s an quantity UP TO 10 million. Then again, I’m keen to pay USD 10 million, no extra and no much less.”
Mark Stockley, cybersecurity evangelist on the safety agency Malwarebytes, mentioned that by taking up the LockBit website and utilizing it in the best way that it has, the NCA is clearly trolling the LockBit group and its chief, LockBitSupp.
“I don’t suppose that is an accident—that is how ransomware teams discuss to one another,” Stockley mentioned. “That is regulation enforcement taking the time to get pleasure from its second, and humiliate LockBit in its personal vernacular, presumably so it loses face.”
In a press convention right now, the FBI mentioned Operation Cronos included investigative help from the Gendarmerie-C3N in France; the State Felony Police Workplace L-Okay-A and Federal Felony Police Workplace in Germany; Fedpol and Zurich Cantonal Police in Switzerland; the Nationwide Police Company in Japan; the Australian Federal Police; the Swedish Police Authority; the Nationwide Bureau of Investigation in Finland; the Royal Canadian Mounted Police; and the Nationwide Police within the Netherlands.
The Justice Division mentioned victims focused by LockBit ought to contact the FBI at https://lockbitvictims.ic3.gov/ to find out whether or not affected techniques might be efficiently decrypted. As well as, the Japanese Police, supported by Europol, have launched a restoration device designed to get better recordsdata encrypted by the LockBit 3.0 Black Ransomware.










