On Jan. 9, 2024, U.S. authorities arrested a 19-year-old Florida man charged with wire fraud, aggravated identification theft, and conspiring with others to make use of SIM-swapping to steal cryptocurrency. Sources near the investigation inform KrebsOnSecurity the accused was a key member of a legal hacking group blamed for a string of cyber intrusions at main U.S. expertise corporations in the course of the summer season of 2022.
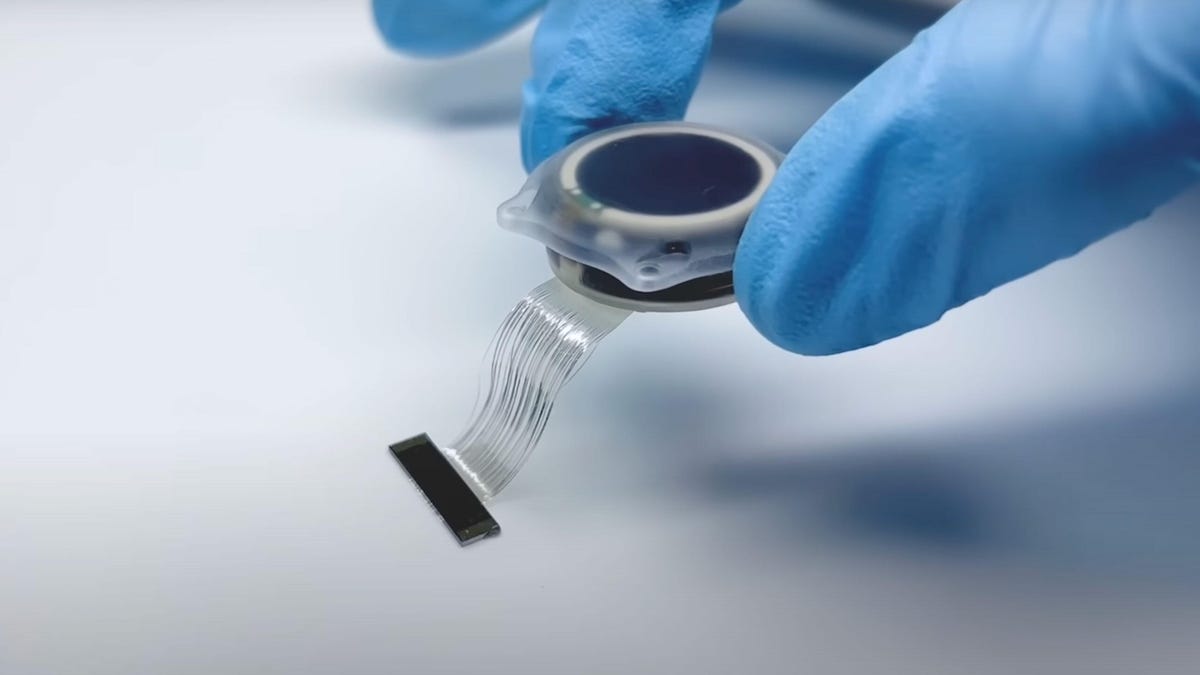
A graphic depicting how 0ktapus leveraged one sufferer to assault one other. Picture credit score: Amitai Cohen of Wiz.
Prosecutors say Noah Michael City of Palm Coast, Fla., stole at the very least $800,000 from at the very least 5 victims between August 2022 and March 2023. In every assault, the victims noticed their e mail and monetary accounts compromised after struggling an unauthorized SIM-swap, whereby attackers transferred every sufferer’s cell phone quantity to a brand new system that they managed.
The federal government says City glided by the aliases “Sosa” and “King Bob,” amongst others. A number of trusted sources advised KrebsOnSecurity that Sosa/King Bob was a core member of a hacking group behind the 2022 breach at Twilio, an organization that gives providers for making and receiving textual content messages and cellphone calls. Twilio disclosed in Aug. 2022 that an intrusion had uncovered a “restricted quantity” of Twilio buyer accounts by a classy social engineering assault designed to steal worker credentials.
Shortly after that disclosure, the safety agency Group-IB printed a report linking the attackers behind the Twilio intrusion to separate breaches at greater than 130 organizations, together with LastPass, DoorDash, Mailchimp, and Plex. A number of safety companies quickly assigned the hacking group the nickname “Scattered Spider.”
Group-IB dubbed the gang by a distinct title — 0ktapus — which was a nod to how the legal group phished workers for credentials. The missives requested customers to click on a hyperlink and log in at a phishing web page that mimicked their employer’s Okta authentication web page. Those that submitted credentials have been then prompted to supply the one-time password wanted for multi-factor authentication.

A reserving picture of Noah Michael City launched by the Volusia County Sheriff.
0ktapus used newly-registered domains that usually included the title of the focused firm, and despatched textual content messages urging workers to click on on hyperlinks to those domains to view details about a pending change of their work schedule. The phishing websites used a Telegram instantaneous message bot to ahead any submitted credentials in real-time, permitting the attackers to make use of the phished username, password and one-time code to log in as that worker at the actual employer web site.
0ktapus typically leveraged info or entry gained in a single breach to perpetrate one other. As documented by Group-IB, the group pivoted from its entry to Twilio to assault at the very least 163 of its prospects. Amongst these was the encrypted messaging app Sign, which stated the breach may have let attackers re-register the cellphone quantity on one other system for about 1,900 customers.
On July 28 and once more on Aug. 7, a number of workers at e mail supply agency Mailchimp supplied their distant entry credentials to this phishing group. In keeping with an Aug. 12 weblog submit, the attackers used their entry to Mailchimp worker accounts to steal information from 214 prospects concerned in cryptocurrency and finance.
On August 25, 2022, the password supervisor service LastPass disclosed a breach through which attackers stole some supply code and proprietary LastPass technical info, and weeks later LastPass stated an investigation revealed no buyer information or password vaults have been accessed.
Nonetheless, on November 30, 2022 LastPass disclosed a much more severe breach that the corporate stated leveraged information stolen within the August breach. LastPass stated legal hackers had stolen encrypted copies of some password vaults, in addition to different private info.
In February 2023, LastPass disclosed that the intrusion concerned a extremely advanced, focused assault in opposition to a DevOps engineer who was one in all solely 4 LastPass workers with entry to the company vault. In that incident, the attackers exploited a safety vulnerability in a Plex media server that the worker was operating on his residence community, and succeeded in putting in malicious software program that stole passwords and different authentication credentials. The vulnerability exploited by the intruders was patched again in 2020, however the worker by no means up to date his Plex software program.
Because it occurs, Plex introduced its personal information breach someday earlier than LastPass disclosed its preliminary August intrusion. On August 24, 2022, Plex’s safety crew urged customers to reset their passwords, saying an intruder had accessed buyer emails, usernames and encrypted passwords.
KING BOB’S GRAILS
The Justice Division says City glided by glided by the nicknames “Sosa,” “Elijah,” and “King Bob.” A evaluate of hundreds of messages that these customers posted to a number of public boards and Discord servers over the previous two years reveals that the particular person behind these identities was primarily centered on two issues: Sim-swapping, and buying and selling in stolen, unreleased rap music recordings from well-liked artists.
Certainly, these messages present Sosa/King Bob was obsessive about discovering new “grails,” the slang time period utilized in some cybercrime dialogue channels to explain recordings from well-liked artists which have by no means been formally launched. It stands to motive that King Bob was SIM-swapping essential folks within the music business to acquire these information, though there’s little to assist this conclusion from the general public chat data accessible.
“I received probably the most music within the com,” King Bob bragged in a Discord server in November 2022. “I received hundreds of grails.”
King Bob’s chats present he was notably enamored of stealing the unreleased works of his favourite artists — Lil Uzi Vert, Playboi Carti, and Juice Wrld. When one other Discord consumer requested if he has Eminem grails, King Bob stated he was not sure.
“I’ve two folders,” King Bob defined. “One with Uzi, Carti, Juicewrld. After which I’ve ‘each different artist.’ Each different artist is unorganized as fuck and has hundreds of random shit.”
King Bob’s posts on Discord present he shortly grew to become a celeb on Leaked[.]cx, one in all most lively boards for buying and selling, shopping for and promoting unreleased music from well-liked artists. The extra grails that customers share with the Leaked[.]cx group, the extra their standing and entry on the discussion board grows.
The final cache of Leaked dot cx listed by the archive.org on Jan. 11, 2024.
And King Bob shared numerous his purloined tunes with this group. Nonetheless others he tried to promote. It’s unclear what number of of these gross sales have been ever consummated, however it isn’t uncommon for a prized grail to promote for wherever from $5,000 to $20,000.
In mid-January 2024, a number of Leaked[.]cx regulars started complaining that they hadn’t seen King Bob shortly and have been actually lacking his grails. On or round Jan. 11, the identical day the Justice Division unsealed the indictment in opposition to City, Leaked[.]cx began blocking individuals who have been making an attempt to go to the location from the US.
Days later, annoyed Leaked[.]cx customers speculated about what could possibly be the reason for the blockage.
“Probs blocked as a part of king bob investigation i believe?,” wrote the consumer “Plsdontarrest.” “Doubt he solely hacked US artists/ppl which is why it’s taking place in a number of international locations.”
FORESHADOWING
On Sept. 21, 2022, KrebsOnSecurity advised the story of a “Foreshadow,” the nickname chosen by a Florida teenager who was working for a SIM-swapping crew when he was kidnapped, crushed and held for a $200,000 ransom. A rival SIM-swapping group claimed that Foreshadow and his associates had robbed them of their fair proportion of the earnings from a current SIM-swap.
In a video launched by his abductors on Telegram, a bloodied, battered Foreshadow was made to say they’d kill him until the ransom was paid.
As I wrote in that story, Foreshadow seems to have served as a “holder” — a time period used to explain a low-level member of any SIM-swapping group who agrees to hold out the riskiest and least rewarding function of the crime: Bodily conserving and managing the varied cell gadgets and SIM playing cards which can be utilized in SIM-swapping scams.
KrebsOnSecurity has since realized that Foreshadow was a holder for a very lively SIM-swapper who glided by “Elijah,” which was one other nickname that prosecutors say City used.

Shortly after Foreshadow’s hostage video started circulating on Telegram and Discord, a number of identified actors within the SIM-swapping house advised everybody within the channels to delete any earlier messages with Foreshadow, claiming he was totally cooperating with the FBI.
This was not the primary time Sosa and his crew have been hit with violent assaults from rival SIM-swapping teams. In early 2022, a video surfaced on a well-liked cybercrime channel purporting to indicate attackers hurling a brick by a window at an handle that matches the spacious and upscale residence of City’s mother and father in Sanford, Fl.
“Brickings” are among the many “violence-as-a-service” choices broadly accessible on many cybercrime channels. SIM-swapping and adjoining cybercrime channels are replete with job provides for in-person assignments and duties that may be discovered if one searches for posts titled, “If you happen to reside close to,” or “IRL job” — quick for “in actual life” job.
Numerous these categorised adverts are in service of performing brickings, the place somebody is employed to go to a selected handle and toss a brick by the goal’s window. Different typical IRL job provides contain tire slashings and even drive-by shootings.
THE COM
Sosa was identified to be a high member of the broader cybercriminal group on-line referred to as “The Com,” whereby hackers boast loudly about high-profile exploits and hacks that nearly invariably start with social engineering — tricking folks over the cellphone, e mail or SMS into making a gift of credentials that permit distant entry to company inner networks.
Sosa additionally was lively in a very damaging group of achieved legal SIM-swappers referred to as “Star Fraud.” Cyberscoop’s AJ Vicens reported final 12 months that people inside Star Fraud have been seemingly concerned within the high-profile Caesars Leisure an MGM Resorts extortion assaults.
“ALPHV, a longtime ransomware-as-a-service operation considered primarily based in Russia and linked to assaults on dozens of entities, claimed accountability for Caesars and MGM assaults in a word posted to its web site earlier this month,” Vincens wrote. “Specialists had stated the assaults have been the work of a bunch tracked variously as UNC 3944 or Scattered Spider, which has been described as an affiliate working with ALPHV made up of individuals in the US and Britain who excel at social engineering.”
In February 2023, KrebsOnSecurity printed information taken from the Telegram channels for Star Fraud and two different SIM-swapping teams displaying these crooks centered on SIM-swapping T-Cellular prospects, and that they collectively claimed entry to T-Cellular on 100 separate events over a 7-month interval in 2022.
The SIM-swapping teams have been capable of swap focused cellphone numbers to a different system on demand as a result of they always phished T-Cellular workers into giving up credentials to employee-only instruments. In every of these circumstances the objective was the identical: Phish T-Cellular workers for entry to inner firm instruments, after which convert that entry right into a cybercrime service that could possibly be employed to divert any T-Cellular consumer’s textual content messages and cellphone calls to a different system.
Allison Nixon, chief analysis officer on the New York cybersecurity consultancy Unit 221B, stated the growing brazenness of many Com members is a operate of how lengthy it has taken federal authorities to go after guys like Sosa.
“These incidents present what occurs when it takes too lengthy for cybercriminals to get arrested,” Nixon stated. “If governments fail to prioritize this supply of menace, violence originating from the Web will have an effect on common folks.”
NO FIXED ADDRESS
The Daytona Seaside Information-Journal experiences that City was arrested Jan. 9 and his trial is scheduled to start within the trial time period beginning March 4 in Jacksonville. The publication stated the choose overseeing City’s case denied bail as a result of the defendant was a robust flight danger.
At City’s arraignment, it emerged that he had no mounted handle and had been utilizing an alias to remain at an Airbnb. The choose reportedly stated that when a search warrant was executed at City’s residence, the defendant was downloading applications to delete laptop information.
What’s extra, the choose defined, regardless of telling authorities in Might that he wouldn’t have any extra contact together with his co-conspirators and wouldn’t have interaction in cryptocurrency transactions, he did so anyway.
City entered a plea of not responsible. City’s court-appointed lawyer stated her consumer would don’t have any remark right now.
Prosecutors charged City with eight counts of wire fraud, one depend of conspiracy to commit wire fraud, and 5 counts of aggravated identification theft. In keeping with the federal government, if convicted City faces as much as 20 years in federal jail on every wire fraud cost. He additionally faces a minimal obligatory penalty of two years in jail for the aggravated identification offenses, which can run consecutive to some other jail sentence imposed.