The runaway success of Kubernetes adoption by enterprise software program builders has created motivation for attackers to focus on these installations with particularly designed exploits that leverage its reputation. Attackers have grow to be higher at hiding their malware, avoiding the virtually trivial safety controls, and utilizing frequent strategies equivalent to privilege escalation and lateral community motion to unfold their exploits throughout enterprise networks. Whereas strategies for implementing Kubernetes safety finest practices exist, they aren’t universally well-known and require specialised information, instruments, and ways which are very completely different from securing extraordinary cloud and digital machine use instances.
The proof of accelerating Kubernetes-focused assaults comes from direct telemetry, bolstered by anecdotal studies. Safety distributors equivalent to Palo Alto Networks, Wiz, and Aqua Safety all have put in place Kubernetes honeypots that see fast makes an attempt at compromising new clusters, with a newly created cluster being attacked inside minutes or a couple of hours. These assaults scan well-known TCP/IP ports 10250-9 utilized by containers to speak with one another, for instance. These pre-attack scans occur dozens of instances every day, a sign of automated and programmatic efforts to compromise the underlying code.
Let’s study the menace panorama, what exploits safety distributors are detecting, and ways in which enterprises can higher harden their Kubernetes installations and defend themselves.
Kubernetes menace panorama
A report from the Cloud Native Computing Basis illustrates the complexity of the panorama, with an interlocking assortment of knowledge flows, dependencies, and processes. These parts require their very own protecting strategies to encrypt communications, authenticate containers, storage repositories and customers appropriately, and shield containers from being exploited. The diagram beneath (from the Basis, interpreted by Development Micro) exhibits that there’s a steep studying curve to know all of the relationships and the way the assorted components match collectively.
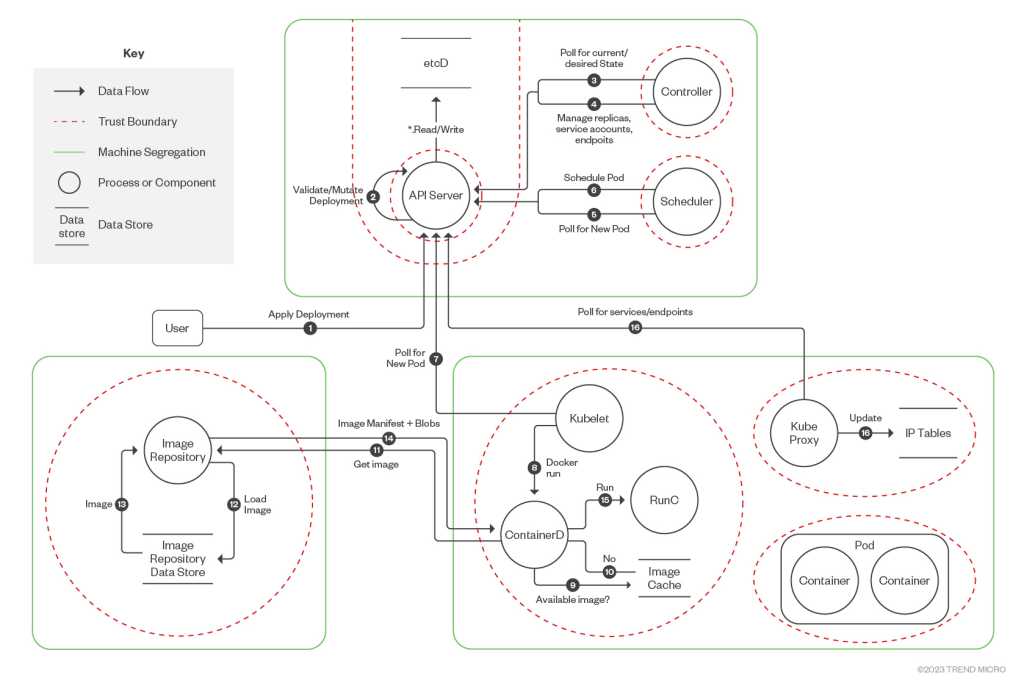
Kubernetes knowledge move diagram by CNCF Monetary Companies Person Group
Development Micro
The complexity of this structure was carried out intentionally, as a result of Kubernetes “was designed to permit customers to have plenty of freedom and used an open structure and a default safety mannequin of being open by default,” Assaf Morag, a knowledge analyst with Aqua Safety, tells CSO. However despair not: “The truth that Kubernetes is such a sprawling platform with so many integrations presents a chance. It makes it simple to construct an automatic, systematic set of processes that bakes safety into the core of the Kubernetes construct and deployment course of,” as Palo Alto Networks’ current “Full Information to Kubernetes Safety” mentions in its introduction. Nonetheless, the inherent openness of Kubernetes signifies that there is no such thing as a single safety toolset that does all the pieces.
Going again to safety fundamentals
Typically, primary community safety postures equivalent to not exposing secret encryption keys, utilizing advanced and non-default administrative passwords, deploying varied segmentation schemes and following least privilege entry rights are seemingly forgotten in terms of how containers are secured. “Now we have reverted again to the threats we noticed throughout our Nineteen Nineties networks,” Palo Alto Networks supervisor of cloud menace intelligence Nathaniel Quist tells CSO.









