The proliferation of latest top-level domains (TLDs) has exacerbated a well known safety weak point: Many organizations arrange their inner Microsoft authentication techniques years in the past utilizing domains in TLDs that didn’t exist on the time. Which means, they’re constantly sending their Home windows usernames and passwords to domains they don’t management and that are freely out there for anybody to register. Right here’s a have a look at one safety researcher’s efforts to map and shrink the dimensions of this insidious drawback.

At challenge is a well known safety and privateness menace known as “namespace collision,” a scenario the place domains supposed for use completely on an inner firm community find yourself overlapping with domains that may resolve usually on the open Web.
Home windows computer systems on a personal company community validate different issues on that community utilizing a Microsoft innovation known as Energetic Listing, which is the umbrella time period for a broad vary of identity-related companies in Home windows environments. A core a part of the best way this stuff discover one another includes a Home windows characteristic known as “DNS identify devolution,” a type of community shorthand that makes it simpler to seek out different computer systems or servers with out having to specify a full, professional area identify for these assets.
Take into account the hypothetical non-public community internalnetwork.instance.com: When an worker on this community needs to entry a shared drive known as “drive1,” there’s no have to sort “drive1.internalnetwork.instance.com” into Home windows Explorer; getting into “drive1” alone will suffice, and Home windows takes care of the remaining.
However issues can come up when a corporation has constructed their Energetic Listing community on prime of a website they don’t personal or management. Whereas that will sound like a bonkers option to design a company authentication system, remember the fact that many organizations constructed their networks lengthy earlier than the introduction of a whole lot of latest top-level domains (TLDs), like .community, .inc, and .llc.
For instance, an organization in 2005 builds their Microsoft Energetic Listing service across the area firm.llc, maybe reasoning that since .llc wasn’t even a routable TLD, the area would merely fail to resolve if the group’s Home windows computer systems have been ever used exterior of its native community.
Alas, in 2018, the .llc TLD was born and commenced promoting domains. From then on, anybody who registered firm.llc would be capable to passively intercept that group’s Microsoft Home windows credentials, or actively modify these connections in a roundabout way — corresponding to redirecting them someplace malicious.
Philippe Caturegli, founding father of the safety consultancy Seralys, is one in every of a number of researchers looking for to chart the dimensions of the namespace collision drawback. As knowledgeable penetration tester, Caturegli has lengthy exploited these collisions to assault particular targets that have been paying to have their cyber defenses probed. However over the previous yr, Caturegli has been step by step mapping this vulnerability throughout the Web by on the lookout for clues that seem in self-signed safety certificates (e.g. SSL/TLS certs).
Caturegli has been scanning the open Web for self-signed certificates referencing domains in a wide range of TLDs more likely to attraction to companies, together with .advert, .associates, .heart, .cloud, .consulting, .dev, .digital, .domains, .e-mail, .world, .gmbh, .group, .holdings, .host, .inc, .institute, .worldwide, .it, .llc, .ltd, .administration, .ms, .identify, .community, .safety, .companies, .web site, .srl, .help, .techniques, .tech, .college, .win and .zone, amongst others.
Seralys discovered certificates referencing greater than 9,000 distinct domains throughout these TLDs. Their evaluation decided many TLDs had way more uncovered domains than others, and that about 20 p.c of the domains they discovered ending .advert, .cloud and .group stay unregistered.
“The size of the difficulty appears larger than I initially anticipated,” Caturegli mentioned in an interview with KrebsOnSecurity. “And whereas doing my analysis, I’ve additionally recognized authorities entities (international and home), vital infrastructures, and so on. which have such misconfigured property.”
REAL-TIME CRIME
A number of the above-listed TLDs usually are not new and correspond to country-code TLDs, like .it for Italy, and .advert, the country-code TLD for the tiny nation of Andorra. Caturegli mentioned many organizations little doubt seen a website ending in .advert as a handy shorthand for an inner Active Directory setup, whereas being unaware or unworried that somebody might truly register such a website and intercept all of their Home windows credentials and any unencrypted visitors.
When Caturegli found an encryption certificates being actively used for the area memrtcc.advert, the area was nonetheless out there for registration. He then realized the .advert registry requires potential prospects to point out a sound trademark for a website earlier than it may be registered.
Undeterred, Caturegli discovered a website registrar that may promote him the area for $160, and deal with the trademark registration for one more $500 (on subsequent .advert registrations, he situated an organization in Andorra that might course of the trademark utility for half that quantity).
Caturegli mentioned that instantly after organising a DNS server for memrtcc.advert, he started receiving a flood of communications from a whole lot of Microsoft Home windows computer systems making an attempt to authenticate to the area. Every request contained a username and a hashed Home windows password, and upon looking the usernames on-line Caturegli concluded all of them belonged to cops in Memphis, Tenn.
“It seems to be like all the police vehicles there have a laptop computer within the vehicles, they usually’re all connected to this memrtcc.advert area that I now personal,” Caturegli mentioned, noting wryly that “memrtcc” stands for “Memphis Actual-Time Crime Middle.”
Caturegli mentioned organising an e-mail server file for memrtcc.advert brought about him to start receiving automated messages from the police division’s IT assist desk, together with hassle tickets concerning town’s Okta authentication system.
Mike Barlow, info safety supervisor for the Metropolis of Memphis, confirmed the Memphis Police’s techniques have been sharing their Microsoft Home windows credentials with the area, and that town was working with Caturegli to have the area transferred to them.
“We’re working with the Memphis Police Division to not less than considerably mitigate the difficulty within the meantime,” Barlow mentioned.
Area directors have lengthy been inspired to make use of .native for inner domains, as a result of this TLD is reserved to be used by native networks and can’t be routed over the open Web. Nonetheless, Caturegli mentioned many organizations appear to have missed that memo and gotten issues backwards — organising their inner Energetic Listing construction across the completely routable area native.advert.
Caturegli mentioned he is aware of this as a result of he “defensively” registered native.advert, which he mentioned is at the moment utilized by a number of giant organizations for Energetic Listing setups — together with a European cell phone supplier, and the Metropolis of Newcastle in the UK.
ONE WPAD TO RULE THEM ALL
Caturegli mentioned he has now defensively registered quite a lot of domains ending in .advert, corresponding to inner.advert and schema.advert. However maybe essentially the most harmful area in his steady is wpad.advert. WPAD stands for Net Proxy Auto-Discovery Protocol, which is an historical, on-by-default characteristic constructed into each model of Microsoft Home windows that was designed to make it easier for Home windows computer systems to mechanically discover and obtain any proxy settings required by the native community.
Bother is, any group that selected a .advert area they don’t personal for his or her Energetic Listing setup could have an entire bunch of Microsoft techniques always making an attempt to succeed in out to wpad.advert if these machines have proxy automated detection enabled.
Safety researchers have been beating up on WPAD for greater than twenty years now, warning again and again how it may be abused for nefarious ends. At this yr’s DEF CON safety convention in Las Vegas, for instance, a researcher confirmed what occurred after they registered the area wpad.dk: Instantly after switching on the area, they obtained a flood of WPAD requests from Microsoft Home windows techniques in Denmark that had namespace collisions of their Energetic Listing environments.
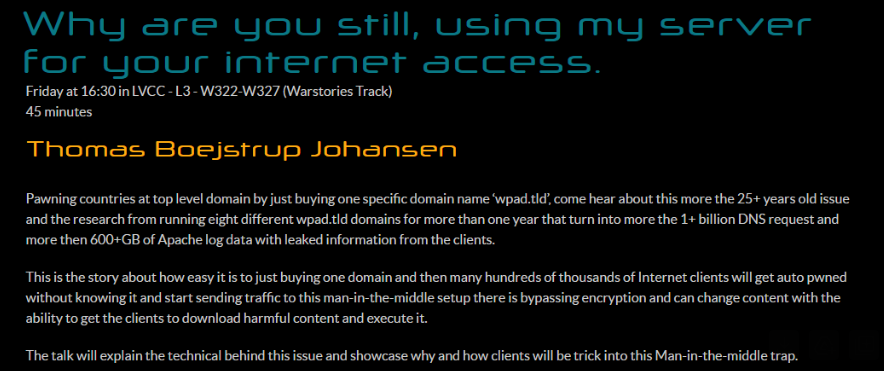
Picture: Defcon.org.
For his half, Caturegli arrange a server on wpad.advert to resolve and file the Web tackle of any Home windows techniques making an attempt to succeed in Microsoft Sharepoint servers, and noticed that over one week it obtained greater than 140,000 hits from hosts all over the world making an attempt to attach.
The basic drawback with WPAD is similar with Energetic Listing: Each are applied sciences initially designed for use in closed, static, trusted workplace environments, and neither was constructed with right now’s cellular gadgets or workforce in thoughts.
Most likely one massive cause organizations with potential namespace collision issues don’t repair them is that rebuilding one’s Energetic Listing infrastructure round a brand new area identify might be extremely disruptive, pricey, and dangerous, whereas the potential menace is taken into account comparatively low.
However Caturegli mentioned ransomware gangs and different cybercrime teams might siphon enormous volumes of Microsoft Home windows credentials from fairly just a few firms with only a small up-front funding.
“It’s a straightforward option to acquire that preliminary entry with out even having to launch an precise assault,” he mentioned. “You simply look forward to the misconfigured workstation to hook up with you and ship you their credentials.”
If we ever study that cybercrime teams are utilizing namespace collisions to launch ransomware assaults, no one can say they weren’t warned. Mike O’Connor, an early area identify investor who registered quite a lot of alternative domains corresponding to bar.com, place.com and tv.com, warned loudly and sometimes again in 2013 that then-pending plans so as to add greater than 1,000 new TLDs would massively increase the variety of namespace collisions. O’Connor was so involved about the issue that he provided $50,000, $25,000 and $10,000 prizes for researchers who might suggest the perfect options for mitigating it.
Mr. O’Connor’s most well-known area is corp.com, as a result of for a number of a long time he watched in horror as a whole lot of hundreds of Microsoft PCs constantly blasted his area with credentials from organizations that had arrange their Energetic Listing surroundings across the area corp.com.
It turned out that Microsoft had truly used corp.com for instance of how one may arrange Energetic Listing in some editions of Home windows NT. Worse, a number of the visitors going to corp.com was coming from Microsoft’s inner networks, indicating some a part of Microsoft’s personal inner infrastructure was misconfigured. When O’Connor mentioned he was able to promote corp.com to the best bidder in 2020, Microsoft agreed to purchase the area for an undisclosed quantity.
“I type of think about this drawback to be one thing like a city [that] knowingly constructed a water provide out of lead pipes, or distributors of these initiatives who knew however didn’t inform their prospects,” O’Connor instructed KrebsOnSecurity. “This isn’t an inadvertent factor like Y2K the place all people was stunned by what occurred. Individuals knew and didn’t care.”

/cdn.vox-cdn.com/uploads/chorus_asset/file/25301216/STK463_SCOTUS_C.jpg)








