Scammers are flooding Fb with teams that purport to supply video streaming of funeral providers for the lately deceased. Family and friends who comply with the hyperlinks for the streaming providers are then requested to cough up their bank card data. Just lately, these scammers have branched out into providing pretend streaming providers for almost any type of occasion marketed on Fb. Right here’s a better have a look at the scale of this scheme, and a few findings about who could also be accountable.
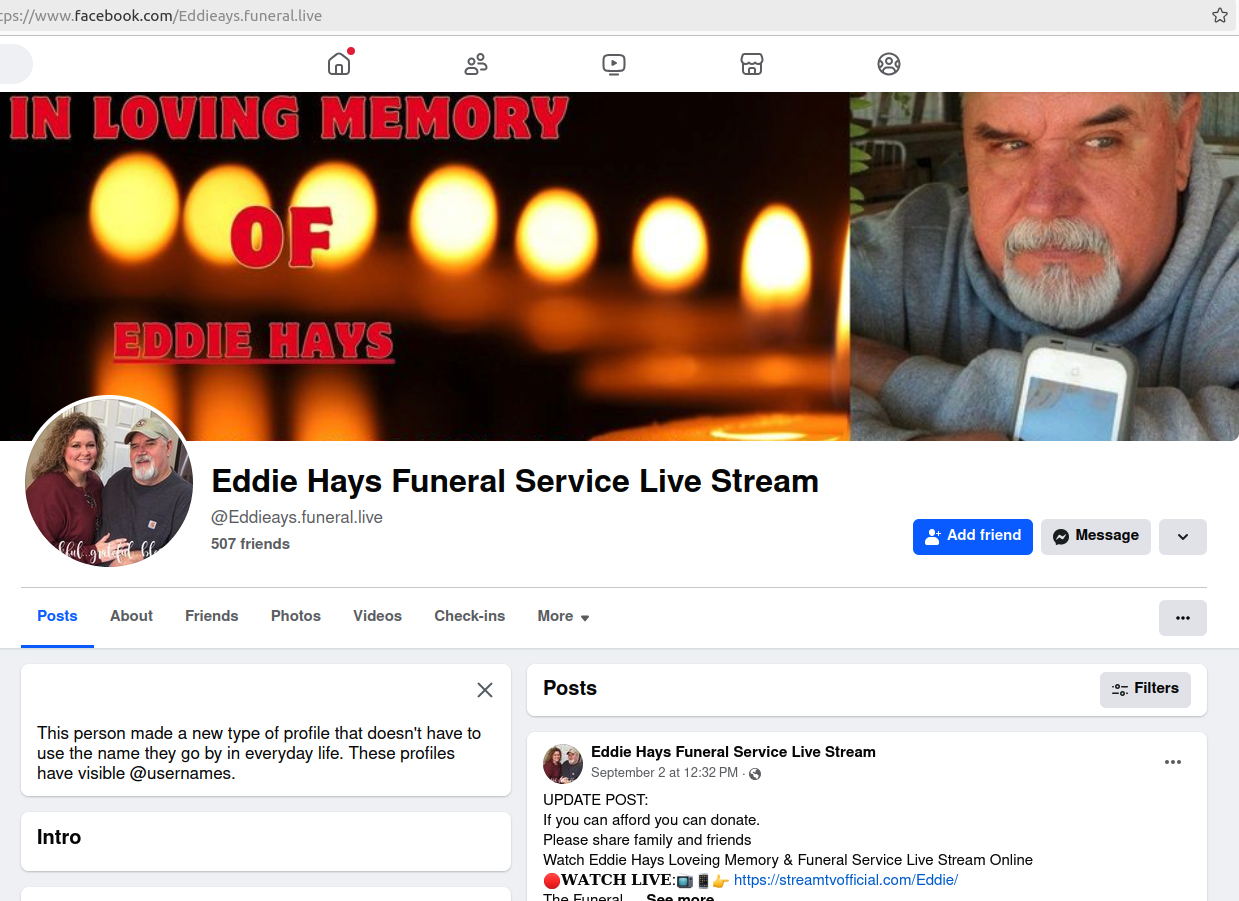
One of many many rip-off funeral group pages on Fb. Clicking to view the “dwell stream” of the funeral takes one to a newly registered web site that requests bank card data.
KrebsOnSecurity lately heard from a reader named George who mentioned a pal had simply handed away, and he seen {that a} Fb group had been created in that pal’s reminiscence. The web page listed the proper time and date of the funeral service, which it claimed may very well be streamed over the Web by following a hyperlink that led to a web page requesting bank card data.
“After I posted concerning the website, a buddy of mine indicated [the same thing] occurred to her when her pal handed away two weeks in the past,” George mentioned.
Looking Fb/Meta for just a few easy key phrases like “funeral” and “stream” reveals numerous funeral group pages on Fb, a few of them for providers prior to now and others erected for an upcoming funeral.
All of those teams embrace photos of the deceased as their profile picture, and search to funnel customers to a handful of newly-registered video streaming web sites that require a bank card fee earlier than one can proceed. Much more galling, a few of these pages request donations within the title of the deceased.
It’s not clear what number of Fb customers fall for this rip-off, however it’s price noting that many of those pretend funeral teams appeal to subscribers from at the least a number of the deceased’s followers, suggesting these customers have subscribed to the teams in anticipation of the service being streamed. It’s additionally unclear how many individuals find yourself lacking a pal or liked one’s funeral as a result of they mistakenly thought it was being streamed on-line.
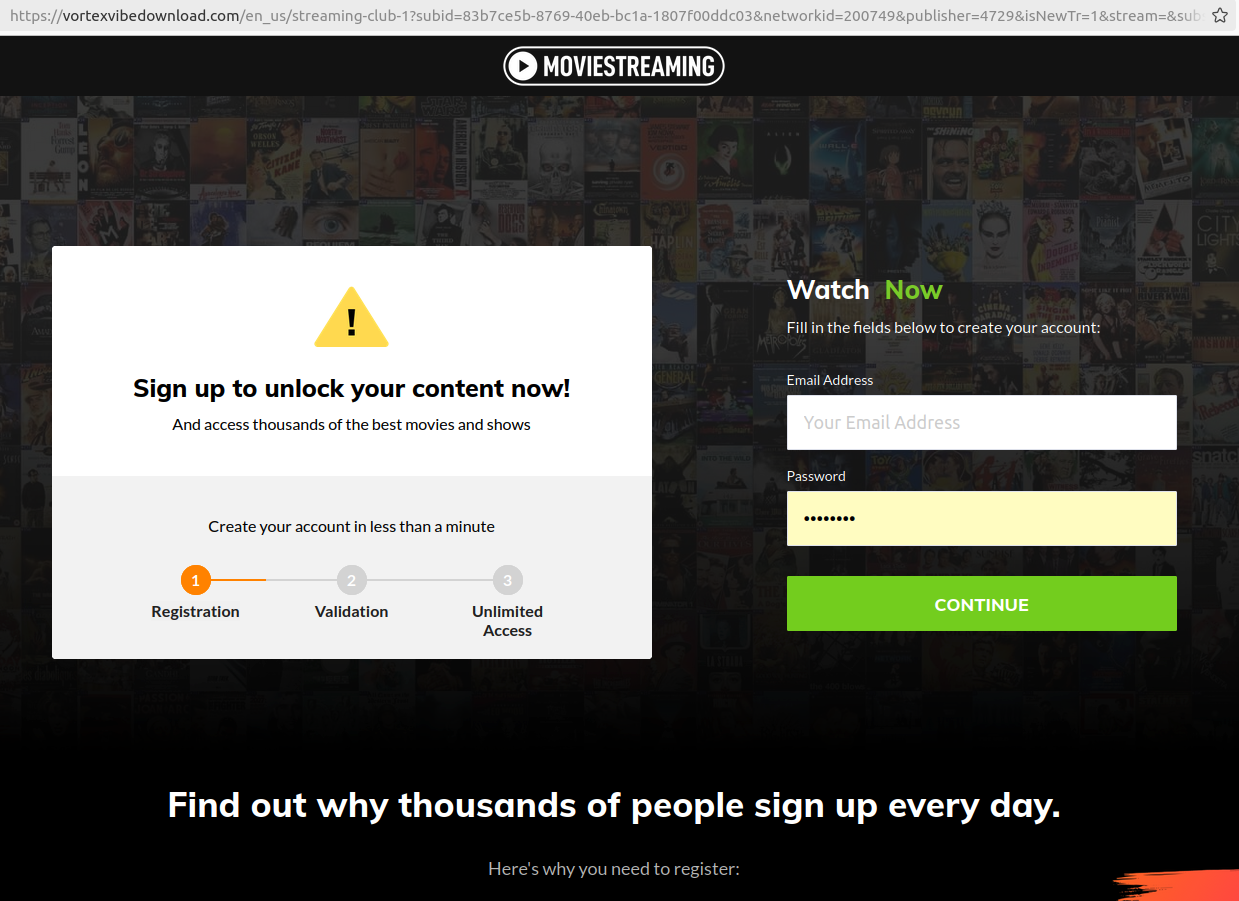
One among many look-alike touchdown pages for video streaming providers linked to rip-off Fb funeral teams.
George mentioned their pal’s funeral service web page on Fb included a hyperlink to the supposed live-streamed service at livestreamnow[.]xyz, a website registered in November 2023.
In accordance with DomainTools.com, the group that registered this area is named “apkdownloadweb,” relies in Rajshahi, Bangladesh, and makes use of the DNS servers of a Website hosting firm in Bangladesh referred to as webhostbd[.]web.
A search on “apkdownloadweb” in DomainTools exhibits three domains registered to this entity, together with live24sports[.]xyz and onlinestreaming[.]xyz. Each of these domains additionally used webhostbd[.]web for DNS. Apkdownloadweb has a Fb web page, which exhibits various “dwell video” teasers for sports activities occasions which have already occurred, and says its area is apkdownloadweb[.]com.
Livestreamnow[.]xyz is presently hosted at a Bangladeshi website hosting supplier named cloudswebserver[.]com, however historic DNS information present this web site additionally used DNS servers from webhostbd[.]web.
The Web tackle of livestreamnow[.]xyz is 148.251.54.196, on the internet hosting big Hetzner in Germany. DomainTools exhibits this similar Web tackle is residence to almost 6,000 different domains (.CSV), together with a whole bunch that reference video streaming phrases, like watchliveon24[.]com and foxsportsplus[.]com.
There are millions of domains at this IP tackle that embrace or finish within the letters “bd,” the nation code top-level area for Bangladesh. Though many domains correspond to web sites for electronics shops or blogs about IT subjects, simply as many comprise a good quantity of placeholder content material (assume “lorem ipsum” textual content on the “contact” web page). In different phrases, the websites seem reliable at first look, however upon nearer inspection it’s clear they don’t seem to be presently utilized by energetic companies.
The passive DNS information for 148.251.54.196 present a stunning variety of outcomes which are principally two domains mushed collectively. For instance, there’s watchliveon24[.]com.playehq4ks[.]com, which shows hyperlinks to a number of funeral service streaming teams on Fb.
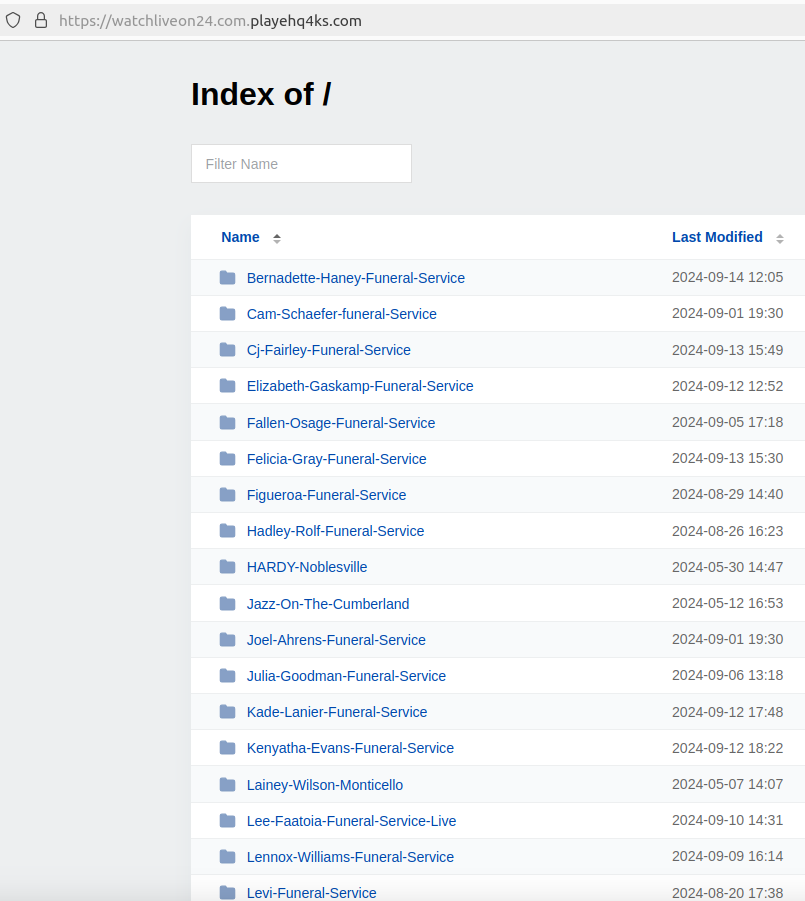
One other mixed area on the identical Web tackle — livestreaming24[.]xyz.allsportslivenow[.]com — lists dozens of hyperlinks to Fb teams for funerals, but in addition for just about all varieties of occasions which are introduced or posted about by Fb customers, together with graduations, concert events, award ceremonies, weddings, and rodeos.
Even neighborhood occasions promoted by state and native police departments on Fb are honest sport for these scammers. A Fb web page maintained by the police power in Plympton, Mass. for a city social occasion this summer season referred to as Plympton Night time Out was shortly made into two completely different Fb teams that knowledgeable guests they may stream the festivities at both espnstreamlive[.]co or skysports[.]dwell.
WHO’S BEHIND THE FAKEBOOK FUNERALS?
Recall that the registrant of livestreamnow[.]xyz — the bogus streaming website linked within the Fb group for George’s late pal — was a corporation referred to as “Apkdownloadweb.” That entity’s area — apkdownloadweb[.]com — is registered to a Mazidul Islam in Rajshahi, Bangladesh (this area can also be utilizing Webhostbd[.]web DNS servers).
Mazidul Islam’s LinkedIn web page says he’s the organizer of a now defunct IT weblog referred to as gadgetsbiz[.]com, which DomainTools finds was registered to a Mehedi Hasan from Rajshahi, Bangladesh.
To convey this full circle, DomainTools finds the area title for the DNS supplier on all the above-mentioned websites — webhostbd[.]web — was initially registered to a Md Mehedi, and to the e-mail tackle webhostbd.web@gmail.com (“MD” is a standard abbreviation for Muhammad/Mohammod/Muhammed).
A search on that e-mail tackle at Constella finds a breached file from the info dealer Apollo.io saying its proprietor’s full title is Mohammod Mehedi Hasan. Sadly, this isn’t a very distinctive title in that area of the world.
However as luck would have it, someday final 12 months the administrator of apkdownloadweb[.]com managed to contaminate their Home windows PC with password-stealing malware. We all know this as a result of the uncooked logs of knowledge stolen from this administrator’s PC have been listed by the breach monitoring service Constella Intelligence [full disclosure: As of this month, Constella is an advertiser on this website].
These so-called “stealer logs” are principally generated by opportunistic infections from information-stealing trojans which are offered on cybercrime markets. A typical set of logs for a compromised PC will embrace any usernames and passwords saved in any browser on the system, in addition to a listing of latest URLs visited and information downloaded.
Malware purveyors will typically deploy infostealer malware by bundling it with “cracked” or pirated software program titles. Certainly, the stealer logs for the administrator of apkdownloadweb[.]com present this person’s PC turned contaminated instantly after they downloaded a booby-trapped cellular utility growth toolkit.
These stolen credentials point out Apkdownloadweb[.]com is maintained by a 20-something native of Dhaka, Bangladesh named Mohammod Abdullah Khondokar.
The “browser historical past” folder from the admin of Apkdownloadweb exhibits Khondokar lately left a touch upon the Fb web page of Mohammod Mehedi Hasan, and Khondokar’s Fb profile says the 2 are pals.
Neither MD Hasan nor MD Abdullah Khondokar responded to requests for remark. KrebsOnSecurity additionally sought remark from Meta.










