The Division of Homeland Safety (DHS) is urging states and localities to beef up safety round proprietary gadgets that connect with the Emergency Alert System — a nationwide public warning system used to ship necessary emergency info, reminiscent of extreme climate and AMBER alerts. The DHS warning got here prematurely of a workshop to be held this weekend on the DEFCON safety convention in Las Vegas, the place a safety researcher is slated to display a number of weaknesses within the nationwide alert system.

A Digital Alert Methods EAS encoder/decoder that Pyle stated he acquired off eBay in 2019. It had the username and password for the system printed on the machine.
The DHS warning was prompted by safety researcher Ken Pyle, a accomplice at safety agency Cybir. Pyle stated he began buying outdated EAS tools off of eBay in 2019, and that he rapidly recognized plenty of critical safety vulnerabilities in a tool that’s broadly utilized by states and localities to encode and decode EAS alert indicators.
“I discovered all types of issues again then, and reported it to the DHS, FBI and the producer,” Pyle stated in an interview with KrebsOnSecurity. “However nothing ever occurred. I made a decision I wasn’t going to inform anybody about it but as a result of I wished to provide individuals time to repair it.”
Pyle stated he took up the analysis once more in earnest after an indignant mob stormed the U.S. Capitol on Jan. 6, 2021.
“I used to be sitting there pondering, ‘Holy shit, somebody may begin a civil warfare with this factor,”’ Pyle recalled. “I went again to see if this was nonetheless an issue, and it seems it’s nonetheless a really massive drawback. So I made a decision that until somebody truly makes this public and talks about it, clearly nothing goes to be accomplished about it.”
The EAS encoder/decoder gadgets Pyle acquired have been made by Lyndonville, NY-based Digital Alert Methods (previously Monroe Electronics, Inc.), which issued a safety advisory this month saying it launched patches in 2019 to repair the issues reported by Pyle, however that some clients are nonetheless working outdated variations of the gadget’s firmware. Which may be as a result of the patches have been included in model 4 of the firmware for the EAS gadgets, and plenty of older fashions apparently don’t assist the brand new software program.
“The vulnerabilities recognized current a probably critical threat, and we consider each have been addressed in software program updates issued starting Oct 2019,” EAS stated in a written assertion. “We additionally supplied attribution for the researcher’s accountable disclosure, permitting us to rectify the issues earlier than making any public statements. We’re conscious that some customers haven’t taken corrective actions and up to date their software program and may instantly take motion to replace the most recent software program model to make sure they don’t seem to be in danger. Something decrease than model 4.1 ought to be up to date instantly. On July 20, 2022, the researcher referred to different potential points, and we belief the researcher will present extra element. We’ll consider and work to situation any vital mitigations as rapidly as doable.”
However Pyle stated an awesome many EAS stakeholders are nonetheless ignoring fundamental recommendation from the producer, reminiscent of altering default passwords and inserting the gadgets behind a firewall, in a roundabout way exposing them to the Web, and proscribing entry solely to trusted hosts and networks.

Pyle, in a selfie that’s closely redacted as a result of the EAS gadget behind him had its person credentials printed on the lid.
Pyle stated the largest menace to the safety of the EAS is that an attacker would solely must compromise a single EAS station to ship out alerts domestically that may be picked up by different EAS methods and retransmitted throughout the nation.
“The method for alerts is automated most often, therefore, acquiring entry to a tool will will let you pivot round,” he stated. “There’s no centralized management of the EAS as a result of these gadgets are designed such that somebody domestically can situation an alert, however there’s no central management over whether or not I’m the one one that can ship or no matter. If you’re a neighborhood operator, you’ll be able to ship out nationwide alerts. That’s how straightforward it’s to do that.”
One of many Digital Alert Methods gadgets Pyle sourced from an electronics recycler earlier this yr was non-functioning, however whoever discarded it uncared for to wipe the onerous drive embedded within the machine. Pyle quickly found the gadget contained the non-public cryptographic keys and different credentials wanted to ship alerts via Comcast, the nation’s third-largest cable firm.
“I can situation and create my very own alert right here, which has all of the legitimate checks or no matter for being an actual alert station,” Pyle stated in an interview earlier this month. “I can create a message that can begin propagating via the EAS.”
Comcast informed KrebsOnSecurity that “a third-party gadget used to ship EAS alerts was misplaced in transit by a trusted delivery supplier between two Comcast areas and subsequently obtained by a cybersecurity researcher.
“We’ve performed an intensive investigation of this matter and have decided that no buyer information, and no delicate Comcast information, have been compromised,” Comcast spokesperson David McGuire stated.
The corporate stated it additionally confirmed that the knowledge included on the gadget can now not be used to ship false messages to Comcast clients or used to compromise gadgets inside Comcast’s community, together with EAS gadgets.
“We’re taking steps to additional guarantee safe switch of such gadgets going ahead,” McGuire stated. “Individually, we’ve performed an intensive audit of all EAS gadgets on our community and confirmed that they’re up to date with at present obtainable patches and are due to this fact not weak to lately reported safety points. We’re grateful for the accountable disclosure and to the safety analysis group for persevering with to interact and share info with our groups to make our merchandise and applied sciences ever safer. Mr. Pyle knowledgeable us promptly of his analysis and labored with us as we took steps to validate his findings and make sure the safety of our methods.”
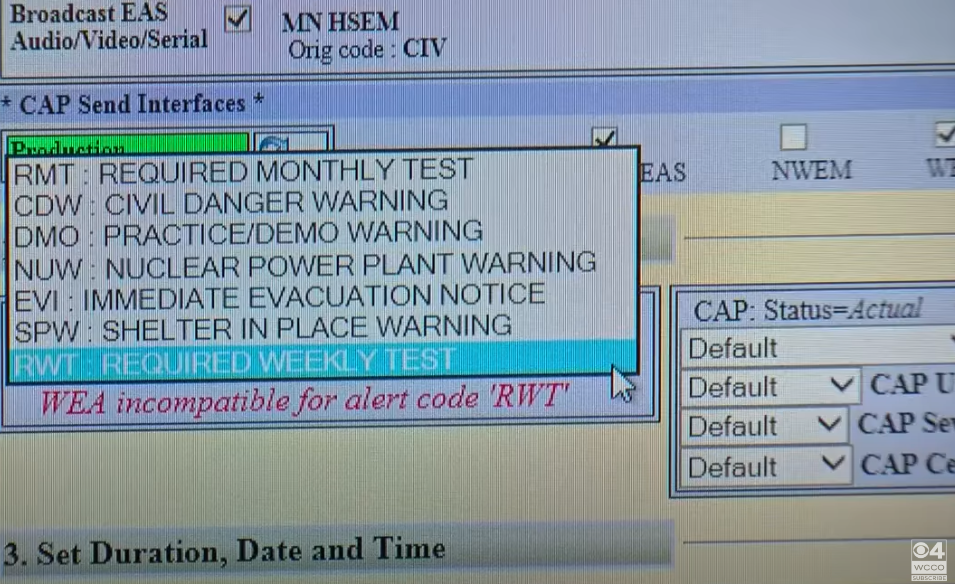
The person interface for an EAS gadget.
Unauthorized EAS broadcast alerts have occurred sufficient that there’s a chronicle of EAS compromises over at fandom.com. Fortunately, most of those incidents have concerned pretty apparent hoaxes.
In keeping with the EAS wiki, in February 2013, hackers broke into the EAS networks in Nice Falls, Mt. and Marquette, Mich. to broadcast an alert that zombies had risen from their graves in a number of counties. In Feb. 2017, an EAS station in Indiana additionally was hacked, with the intruders enjoying the identical “zombies and lifeless our bodies” audio from the 2013 incidents.
“On February 20 and February 21, 2020, Wave Broadband’s EASyCAP tools was hacked because of the tools’s default password not being modified,” the Wiki states. “4 alerts have been broadcasted, two of which consisted of a Radiological Hazard Warning and a Required Month-to-month Check enjoying components of the Hip Hop music Scorching by artist Younger Thug.”
In January 2018, Hawaii despatched out an alert to cell telephones, televisions and radios, warning everybody within the state {that a} missile was headed their method. It took 38 minutes for Hawaii to let individuals know the alert was a misfire, and {that a} draft alert was inadvertently despatched. The information video clip beneath in regards to the 2018 occasion in Hawaii does a very good job of strolling via how the EAS works.










