Most completed cybercriminals exit of their method to separate their actual names from their hacker handles. However amongst sure old-school Russian hackers it isn’t unusual to search out main gamers who’ve completed little to forestall individuals from determining who they’re in actual life. A case examine on this phenomenon is “x999xx,” the nickname chosen by a commemorated Russian hacker who makes a speciality of offering the preliminary community entry to numerous ransomware teams.
x999xx is a widely known “entry dealer” who continuously sells entry to hacked company networks — normally within the type of distant entry credentials — in addition to compromised databases containing giant quantities of non-public and monetary information.
In an evaluation revealed in February 2019, cyber intelligence agency Flashpoint referred to as x999xx probably the most senior and prolific members of the top-tier Russian-language cybercrime discussion board Exploit, the place x999xx might be seen continuously promoting the sale of stolen databases and community credentials.
In August 2023, x999xx offered entry to an organization that develops software program for the actual property business. In July 2023, x999xx marketed the sale of Social Safety numbers, names, and birthdays for the citizenry of a whole U.S. state (unnamed within the public sale).
A month earlier, x999xx posted a gross sales thread for 80 databases taken from Australia’s largest retail firm. “You could use this information to demand a ransom or do one thing completely different with it,” x999xx wrote on Exploit. “Sadly, the flaw was patched quick. [+] nobody has used the info but [+] the info hasn’t been used to ship spam [+] the info is ready for its time.”
In October 2022, x999xx offered administrative entry to a U.S. healthcare supplier.
ALIAS: MAXNM
The oldest account by the identify x999xx appeared in 2009 on the Russian language cybercrime discussion board Verified, below the e-mail tackle maxnm@ozersk.com. Ozersk is a metropolis within the Chelyabinsk area of west-central Russia.
In response to the breach monitoring service Constella Intelligence, the tackle maxnm@ozersk.com was used greater than a decade in the past to create an account at Vktontakte (the Russian reply to Fb) below the identify Maxim Kirtsov from Ozersk. Mr. Kirtsov’s profile — “maxnm” — says his birthday is September 5, 1991.
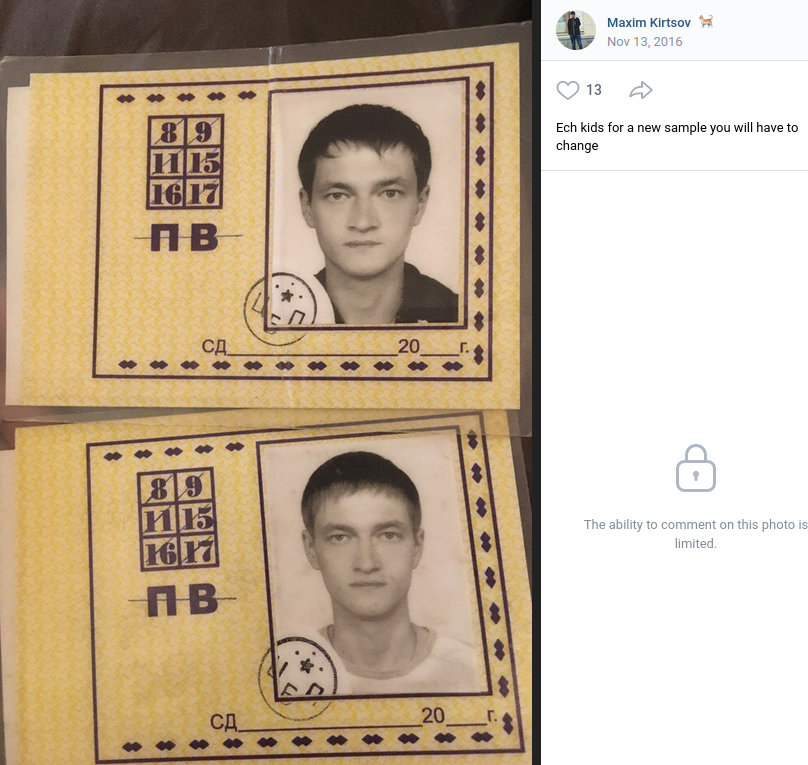
Private images Maxnm shared on Vktontakte in 2016. The caption has been machine translated from Russian.
The consumer x999xx registered on the Russian language cybercrime neighborhood Zloy in 2014 utilizing the e-mail tackle maxnmalias-1@yahoo.com. Constella says this e-mail tackle was utilized in 2022 on the Russian delivery service cdek.ru by a Maksim Georgievich Kirtsov from Ozersk.
Further searches on these contact particulars reveal that previous to 2009, x999xx favored the deal with Maxnm on Russian cybercrime boards. Cyber intelligence firm Intel 471 finds the consumer Maxnm registered on Zloy in 2006 from an Web tackle in Chelyabinsk, utilizing the e-mail tackle kirtsov@telecom.ozersk.ru.
That very same e-mail tackle was used to create Maxnm accounts on a number of different crime boards, together with Spamdot and Exploit in 2005 (additionally from Chelyabinsk), and Damagelab in 2006.
A search in Constella for the Russian model of Kirtsov’s full identify — Кирцов Максим Георгиевич — brings up a number of accounts registered to maksya@icloud.com.
A assessment of the digital footprint for maksya@icloud.com at osint.industries reveals this tackle was used a decade in the past to register a still-active account at imageshack.com below the identify x999xx. That account options quite a few screenshots of economic statements from varied banks, chat logs with different hackers, and even hacked web sites.
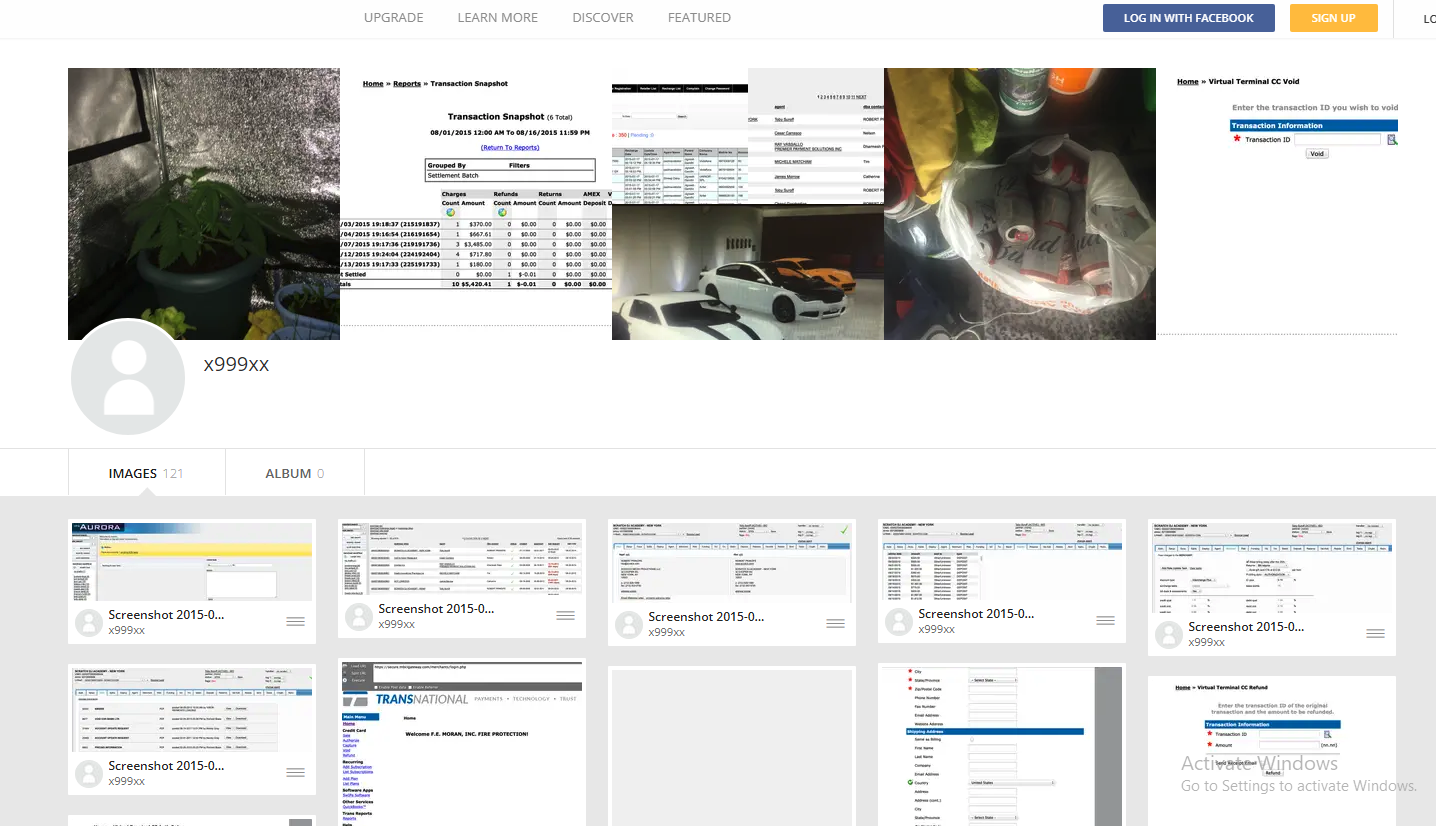
x999xx’s Imageshack account consists of screenshots of checking account balances from dozens of economic establishments, in addition to chat logs with different hackers and footage of homegrown weed.
A few of the images in that Imageshack account additionally seem on Kirtsov’s Vkontakte web page, together with photos of autos he owns, in addition to footage of potted marijuana crops. Kirtsov’s Vkontakte profile says that in 2012 he was a college member of the Ozersk Technological Institute Nationwide Analysis Nuclear College.
The Vkontakte web page lists Kirtsov’s occupation as a web site referred to as ozersk[.]at the moment, which on the floor seems to be a weblog about life in Ozersk. Nonetheless, in 2019 the safety agency Recorded Future revealed a weblog publish which discovered this area was getting used to host a malicious Cobalt Strike server.
Cobalt Strike is a industrial community penetration testing and reconnaissance instrument that’s offered solely to vetted companions. However stolen or ill-gotten Cobalt Strike licenses are continuously abused by cybercriminal gangs to assist lay the groundwork for the set up of ransomware on a sufferer community.
In August 2023, x999xx posted a message on Exploit saying he was all in favour of shopping for a licensed model of Cobalt Strike. A month earlier, x999xx filed a criticism on Exploit in opposition to one other discussion board member named Cobaltforce, an obvious onetime associate whose sudden and extended disappearance from the neighborhood left x999xx and others within the lurch. Cobaltforce recruited individuals skilled in utilizing Cobalt Strike for ransomware operations, and provided to monetize entry to hacked networks for a share of the earnings.
DomainTools.com finds ozersk[.]at the moment was registered to the e-mail tackle dashin2008@yahoo.com, which additionally was used to register roughly two dozen different domains, together with x999xx[.]biz. Nearly all of these domains had been registered to Maxim Kirtsov from Ozersk. Beneath is a thoughts map used to trace the identities talked about on this story.
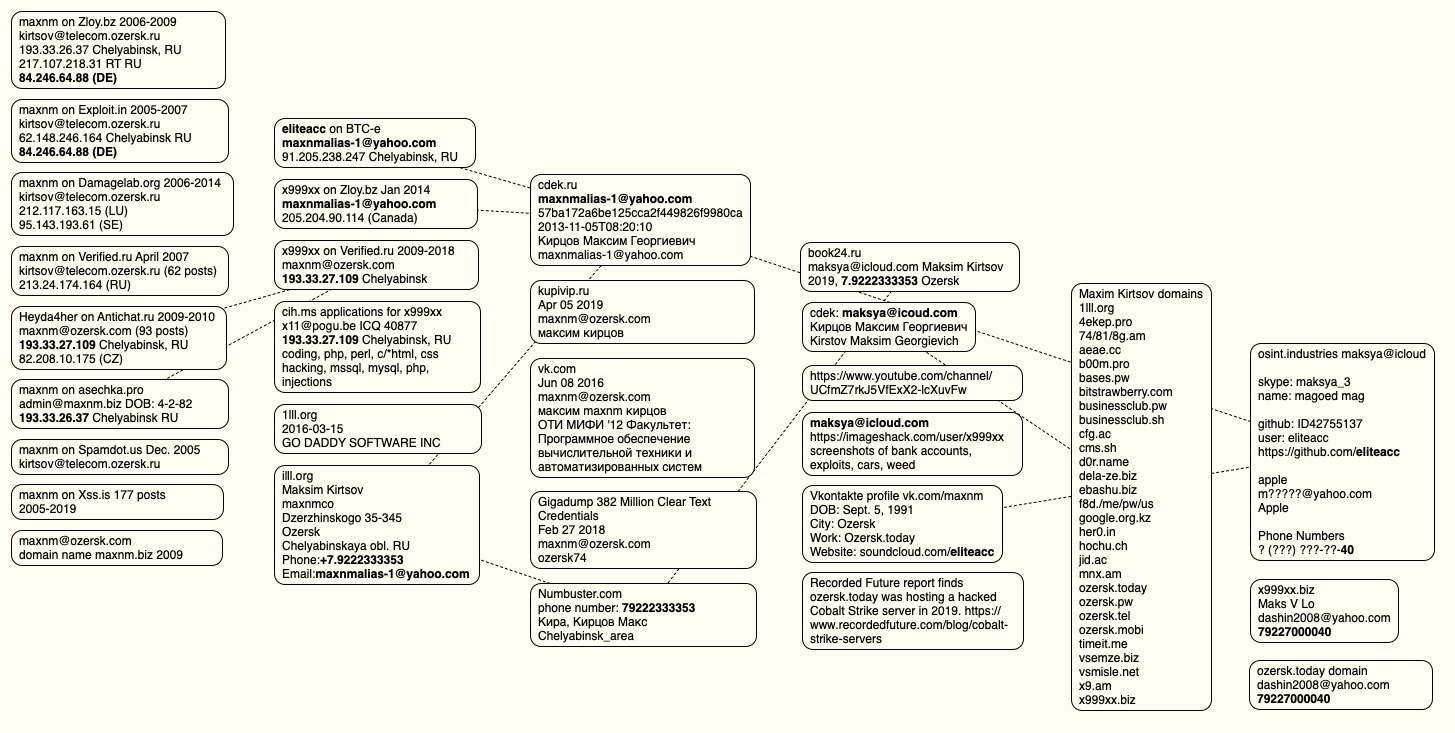
A visible depiction of the info factors connecting x999xx to Max Kirtsov.
x999xx is a prolific member of the Russian webmaster discussion board “Gofuckbiz,” with greater than 2,000 posts over almost a decade, based on Intel 471. In a single publish from 2016, x999xx requested whether or not anybody knew the place he might purchase a warmth lamp that simulates daylight, explaining that one his pet rabbits had lately perished for lack of sufficient mild and warmth. Mr. Kirtsov’s Vkontakte web page consists of a number of footage of caged rabbits from 2015 and earlier.
CONFIRMATION
Reached by way of e-mail, Mr. Kirtsov acknowledged that he’s x999xx. Kirtsov stated he and his workforce are additionally common readers of KrebsOnSecurity.
“We’re glad to listen to and skim you,” Kirtsov replied.
Requested whether or not he was involved in regards to the authorized and ethical implications of his work, Kirtsov downplayed his function in ransomware intrusions, saying he was extra centered on harvesting information.
“I contemplate myself as dedicated to moral practices as you’re,” Kirtsov wrote. “I’ve additionally launched into analysis and am at the moment mentoring college students. You could have observed my actions on a discussion board, which I assume you already know of by info gathered from public sources, presumably utilizing the brand new instrument you reviewed.”
“Relating to my posts about promoting entry, I need to actually admit, upon reviewing my very own actions, I recall such mentions however imagine they had been by no means actualized,” he continued. “Many use the discussion board for self-serving functions, which explains why listings of targets on the market have dwindled — they merely ceased being viable.”
Kirtsov asserted that he’s not all in favour of harming healthcare establishments, simply in stealing their information.
“As for health-related issues, I used to be as soon as acquainted with prosperous site owners who would pay as much as $50 for each 1000 health-themed emails,” Kirtsov stated. “Due to this fact, I had no real interest in the extra delicate information from medical establishments like X-rays, insurance coverage numbers, and even names; I centered solely on emails. I’m proficient in SQL, therefore my ease with dealing with information like IDs and emails. And that i by no means doing spam or one thing like this.”
On the Russian crime boards, x999xx stated he by no means targets something or anybody in Russia, and that he has little to concern from home legislation enforcement companies supplied he stays centered on international adversaries.
x999xx’s lackadaisical strategy to non-public safety mirrors that of Wazawaka, one other prime Russian entry dealer who offered entry to numerous organizations and even operated his personal ransomware affiliate applications.
“Don’t shit the place you reside, journey native, and don’t go overseas,” Wazawaka stated of his personal private mantra. “Mom Russia will enable you to. Love your nation, and you’ll all the time get away with every thing.”
In January 2022, KrebsOnSecurity adopted clues left behind by Wazawaka to establish him as 32-year-old Mikhail Matveev from Khakassia, Russia. In Could 2023, the U.S. Division of Justice indicted Matveev as a key determine in a number of ransomware teams that collectively extorted a whole lot of tens of millions of {dollars} from sufferer organizations. The U.S. State Division is providing a $10 million reward for info resulting in the seize and/or prosecution of Matveev.
Maybe in recognition that many prime ransomware criminals are largely untouchable as long as they continue to be in Russia, western legislation enforcement companies have begun focusing extra on getting contained in the heads of these people. These so-called “psyops” are aimed toward infiltrating ransomware-as-a-service operations, disrupting main cybercrime providers, and reducing belief inside cybercriminal communities.
When authorities within the U.S. and U.Ok. introduced in February 2024 that they’d infiltrated and seized the infrastructure utilized by the notorious LockBit ransomware gang, they borrowed the present design of LockBit’s sufferer shaming web site to hyperlink as an alternative to press releases in regards to the takedown, and included a countdown timer that was finally changed with the non-public particulars of LockBit’s alleged chief.
In Could 2024, legislation enforcement companies in the US and Europe introduced Operation Endgame, a coordinated motion in opposition to a few of the hottest cybercrime platforms for delivering ransomware and data-stealing malware. The Operation Endgame web site additionally included a countdown timer, which served to tease the discharge of a number of animated movies that mimic the identical form of flashy, quick ads that established cybercriminals typically produce to advertise their providers on-line.