Distant Desktop Protocol (RDP) was developed by Microsoft to permit customers, directors, and others to connect with distant computer systems over a community connection utilizing a useful graphical person interface (GUI). The instruments required for this come as normal on Microsoft Home windows; to provoke and arrange an RDP connection, all of the instruments required to do this are current by default. Because of this RDP is used extensively all through networks by customers and directors to entry distant machines.
Sadly, it’s additionally generally abused by ransomware teams – so generally, in reality, that in our common Energetic Adversary Studies our editors are compelled to deal with RDP in a different way in graphics so different findings are even seen. And RDP abuse is on the rise, as we see in Determine 1 — numbers from the previous few years of incident-response information as collected by the Energetic Adversary Report workforce. Within the version of the report we’ll be releasing subsequent month, you’ll see that RDP has now cracked the 90 % mark – that’s, 9 out of ten IR instances embody RDP abuse.
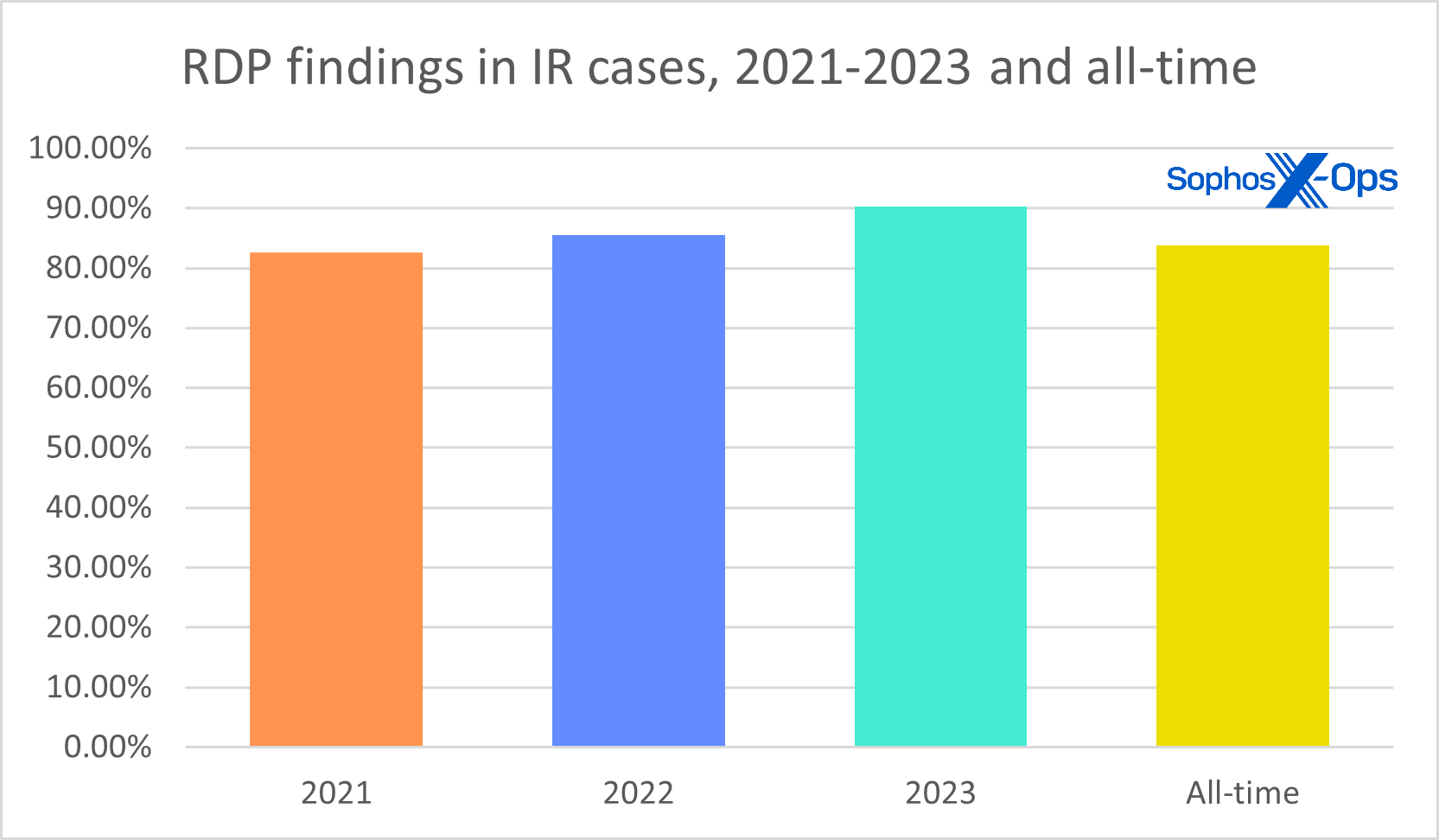
Determine 1: A primary have a look at the total Energetic Adversary dataset from 2023 reveals that RDP abuse is getting worse
As we speak, to supply context and recommendation for directors and responders seeking to cope with RDP, we’re publishing a complete bundle of sources – movies, companion articles with extra data, and a constellation of extra scripts and data on our GitHub repository. We’re doing this each to share our Energetic Adversary workforce’s analysis past the same old long-form stories we subject, and to supply what we hope is a helpful set of sources for dealing with certainly one of infosec’s extra annoying persistent illnesses.
From an attacker’s standpoint, concentrating on RDP is a pure selection. Most importantly, it’s a Microsoft-provided instrument (so, a living-off-the-land binary, or LOLBin) that blends in with typical person and administrative habits. Its utilization alone isn’t apt to attract consideration if nobody’s holding an eye fixed out for it, and an attacker needn’t herald extra instruments that could be detected by EDR or different anti-intrusion instruments. RDP additionally has a comparatively nice graphical person interface that lowers the talent barrier for attackers to browse recordsdata for exfiltration, and to put in and use numerous purposes.
Attackers additionally know that RDP is usually misconfigured or misused inside an atmosphere, each on servers and sometimes on endpoints themselves. The subsequent article on this RDP assortment seems at simply how widespread such publicity is, and whether or not measures akin to switching off RDP’s ordinary 3389 port makes a distinction. (Spoiler: No.)
Rounding out the dismal RDP image, we see self-owns akin to lack of segregation, use of weak credentials, disabling (by directors) of potential protections akin to NLA (network-level authentication), and flagrant disregard for greatest practices akin to least privilege. On the brighter aspect, there are helpful, sturdy queries that can provide nice perception into exactly how RDP is in use in your community… if you understand the place to look.
So, to supply context and recommendation for directors and responders seeking to cope with RDP, we’re beginning with a complete bundle of sources – six movies, six companion articles with extra data, and a constellation of extra scripts and data on our GitHub – with extra to be added over time as occasions dictate.
Distant Desktop Protocol: The Sequence
Half 1: Distant Desktop Protocol: Introduction ([you are here], video)
Half 2: Distant Desktop Protocol: Uncovered RDP (is harmful) (put up, video)
Half 3: RDP: Queries for Investigation (put up, video)
Half 4: RDP Time Zone Bias (put up, video)
Half 5: Executing the Exterior RDP Question (put up, video)
Half 6: Executing the 4624_4625 Login Question (put up, video)
GitHub question repository: SophosRapidResponse/OSQuery
Transcript repository: sophoslabs/video-transcripts
YouTube playlist: Distant Desktop Protocol: The Sequence