Microsoft Workplace information, significantly Excel and Phrase information, have been focused by some cybercriminals for a very long time. By means of completely different strategies, attackers have used embedded Visible Fundamental for Functions macros to contaminate computer systems with completely different sorts of malware for cybercrime and cyberespionage.
Generally, customers nonetheless wanted to click on their settlement when executing code inside these purposes, however some social engineering methods have enticed unsuspecting victims to click on and permit the execution of the malicious macros themselves. Direct exploitation of vulnerabilities with none consumer interplay can be potential to launch malware.
SEE: Cell machine safety coverage (TechRepublic Premium)
Leap to:
.XLL malicious exploitation within the wild
As uncovered in new analysis from Cisco Talos, menace actors may leverage occasion dealing with features in Excel information as a way to robotically launch .XLL information. The commonest methodology to realize that is to execute the malicious code when the Excel Add-In supervisor calls the xlAutoOpen or xlAutoClose features.
Cisco Talos researchers have leveraged particular queries in VirusTotal to seek out malicious .XLL information and supply YARA guidelines to hunt for such information. They separated native .XLL samples constructed with the same old Microsoft .XLL SDK and samples generated utilizing the ExcelDNA framework, as it’s free and tends to be the one most utilized by menace actors (Determine A).
Determine A

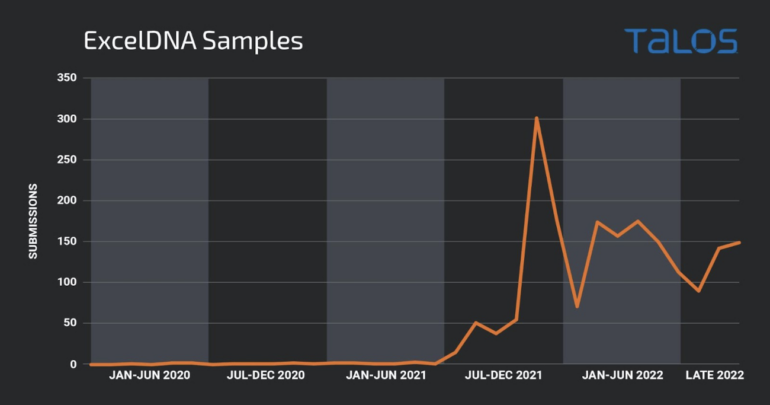
The charts above reveal that menace actors have been exploiting .XLL file vulnerabilities lengthy earlier than Microsoft began blocking paperwork containing VBA macros.
The Cisco Talos researchers established that no probably malicious samples have been submitted till July 2017. The primary .XLL payload discovered on the VirusTotal platform launched calc.exe, which is a ordinary testing methodology for penetration testers and cybercriminals. The second pattern, submitted in the identical month, launched a Meterpreter reverse shell, which can be used for penetration testing or malicious intent.
After that exercise, .XLL information appeared sporadically, nevertheless it didn’t enhance till the top of 2021 when notorious malware households akin to Dridex and FormBook started utilizing it.
Which menace actors exploit .XLL information?
A number of menace actors at the moment are utilizing .XLL information to contaminate computer systems.
APT10, also referred to as Crimson Apollo, menuPass, Stone Panda or Potassium, is a cyberespionage menace actor that has been working since 2006 and is related to the Chinese language Ministry of State Safety, based on the Division of Justice.
A file leveraging .XLL to inject a malware unique to APT10 dubbed Anel was present in December 2017 by the researchers.
TA410 is one other menace actor who targets U.S. utilities and diplomatic organizations and is loosely linked to APT10. They make use of a toolkit that additionally contains an .XLL stage found in 2020.
The DoNot group focusing on Kashmiri nonprofit organizations and Pakistani authorities officers additionally appeared to make use of this methodology: An .XLL file containing two exports, the primary one referred to as pdteong and the second xlAutoOpen, make it a totally purposeful .XLL payload. The pdteong export title has been used solely by the DoNot group.
FIN7 is a cybercrime menace actor working from Russia. In 2022, the menace actor began utilizing .XLL information despatched as attachment information in malicious e mail campaigns. When these information are executed, they act as downloaders for the following an infection stage.
The most important spike within the .XLL detections in VirusTotal, nonetheless, comes primarily from Dridex malware campaigns. These .XLL information are used as downloaders for the following an infection stage, which is chosen from a big checklist of potential payloads accessible through the Discord software program utility.
The second most typical payload is FormBook, an data stealer out there as a service for an inexpensive value on-line. It makes use of e mail campaigns to unfold the .XLL downloader, which fetches the following an infection stage — the FormBook malware itself.
A current AgentTesla and Lokibot marketing campaign focusing on Hungary exploited .XLL information through e mail. The e-mail pretended to return from Hungarian police departments (Determine B).
Determine B
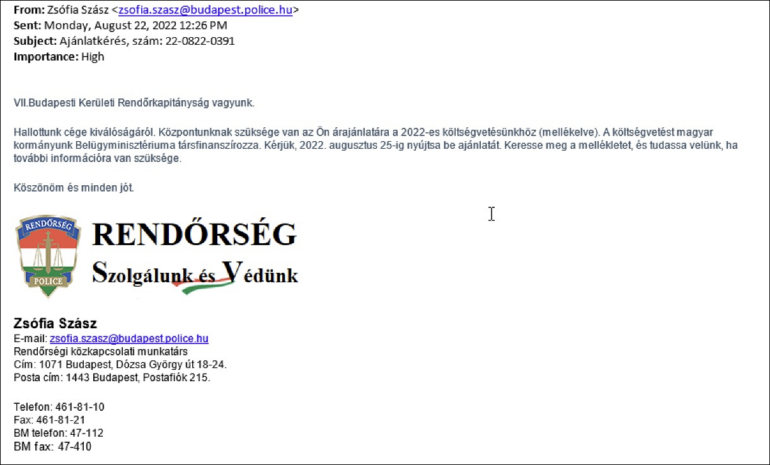
The textual content has been translated by Cisco Talos:
“We’re the VII Budapest District Police Division.
Now we have heard in regards to the excellence of your organization. Our heart wants your quote for our 2022 funds (connected). The funds is co-financed by the Ministry of the Inside of our Hungarian authorities. Please submit your provide by Aug. 25, 2022. Please discover the attachment and tell us in case you want extra data.”
As well as, the Ducktail malware, an data stealer malware run by a Vietnam-operating menace actor, makes use of .XLL. The menace actor used a file named “Particulars of Venture Advertising Plan and Fb Google Adverts Outcomes Report.xll” to contaminate its targets with the Ducktail malware.
Default Microsoft Workplace habits modifications for the great
To assist struggle infections through using VBA macros, Microsoft determined to vary the default habits of its Workplace merchandise to dam macros in information downloaded from the web.
Workplace Add-Ins are items of executable code that may be added to Workplace purposes to enhance functionalities or improve the appliance’s look. Workplace Add-Ins may include VBA code or modules embedding compiled functionalities in .NET bytecode. This may very well be within the type of COM servers or a Dynamic Hyperlink Library renamed with a selected file extension.
Add-Ins for the Microsoft Phrase utility should be in a location specified by a registry worth, relying on the Workplace model. A file put in that folder with a file extension .WLL will probably be loaded into the Phrase course of house.
For Microsoft Excel, any file with the .XLL extension that’s clicked by the consumer will robotically try and run Excel because the opener for the .XLL file. In any case, the Excel software program will set off a show message about potential malware or safety issues, however that is ineffective with normal customers, who are inclined to disregard such warnings.
.XLL add-ins are usually developed within the C/C++ programming language utilizing the Microsoft Excel .XLL Software program Growth Package, however some frameworks akin to Add-In Categorical and Excel-DNA enable using .NET languages like C# or VB.NET.
Tips on how to defend in opposition to the .XLL safety menace
The usage of .XLL information is just not widespread in company environments; companies that don’t want it ought to block any try and execute .XLL information of their setting. If your organization does enable using .XLL information, cautious monitoring have to be run at endpoints and servers as a way to detect any suspicious exercise and examine it.
Electronic mail gateways mustn’t settle for .XLL information by default, and lift consciousness for company customers. In the event that they see a warning message from Excel about working Add-Ins and have no idea why it occurs, they need to not enable the execution and name their IT/safety division.
This safety consciousness and coaching coverage and IT e mail safety alert templates from TechRepublic Premium are nice sources to assist forestall a cybersecurity catastrophe from hanging.
Disclosure: I work for Pattern Micro, however the views expressed on this article are mine.