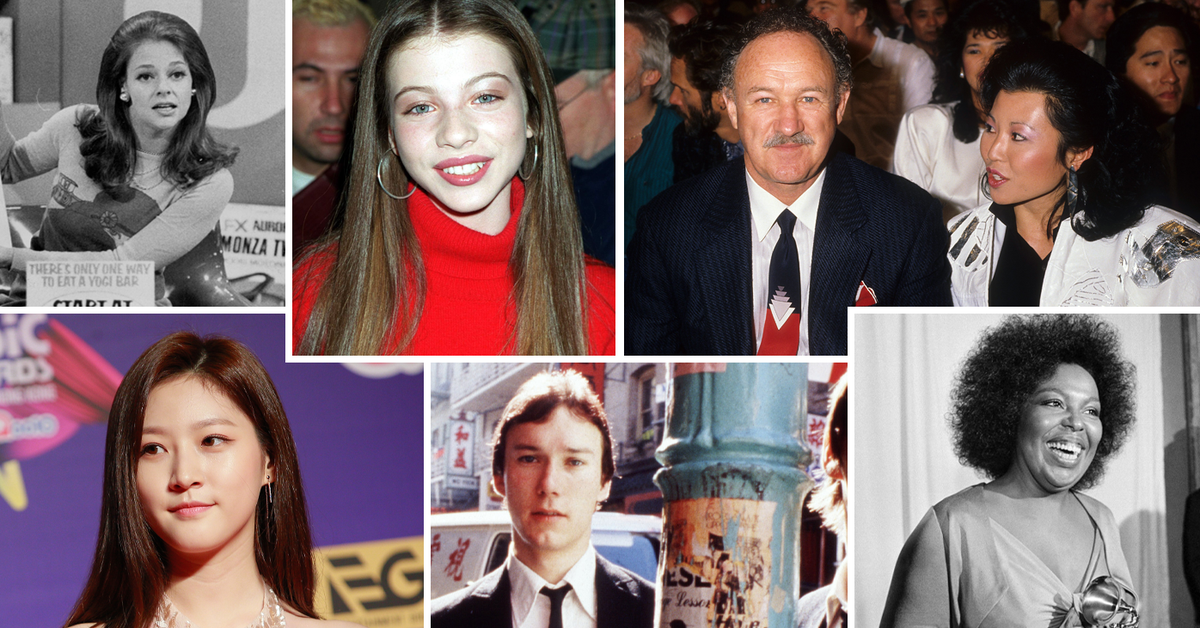
Vyacheslav “Tank” Penchukov, the accused 40-year-old Ukrainian chief of a prolific cybercriminal group that stole tens of thousands and thousands of {dollars} from small to mid-sized companies in america and Europe, has been arrested in Switzerland, in accordance with a number of sources.
Wished Ukrainian cybercrime suspect Vyacheslav “Tank” Penchukov (proper) was arrested in Geneva, Switzerland. Tank was the day-to-day supervisor of a cybercriminal group that stole tens of thousands and thousands of {dollars} from small to mid-sized companies.
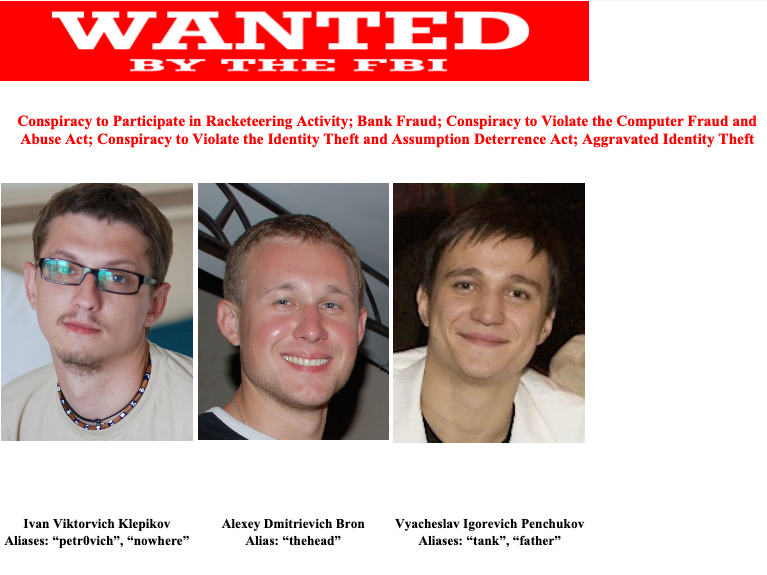
Penchukov was named in a 2014 indictment by the U.S. Division of Justice as a high determine within the JabberZeus Crew, a small however potent cybercriminal collective from Ukraine and Russia that attacked sufferer firms with a strong, custom-made model of the Zeus banking trojan.
The U.S. Federal Bureau of Investigation (FBI) declined to remark for this story. However in accordance with a number of sources, Penchukov was arrested in Geneva, Switzerland roughly three weeks in the past as he was touring to fulfill up together with his spouse there.
Penchukov is from Donetsk, a historically Russia-leaning area in Jap Ukraine that was not too long ago annexed by Russia. In his hometown, Penchukov was a well known deejay (“DJ Slava Wealthy“) who loved being seen driving round in his high-end BMWs and Porsches. Extra not too long ago, Penchukov has been investing fairly a bit in native companies.
The JabberZeus crew’s identify is derived from the malware they used, which was configured to ship them a Jabber prompt message every time a brand new sufferer entered a one-time password code right into a phishing web page mimicking their financial institution. The JabberZeus gang focused principally small to mid-sized companies, they usually had been an early pioneer of so-called “man-in-the-browser” assaults, malware that may silently siphon any knowledge that victims submit by way of a web-based kind.
As soon as inside a sufferer firm’s financial institution accounts, the crooks would modify the agency’s payroll so as to add dozens of “cash mules,” individuals recruited by work-at-home schemes to deal with financial institution transfers. The mules in flip would ahead any stolen payroll deposits — minus their commissions — by way of wire switch abroad.

Tank, a.ok.a. “DJ Slava Wealthy,” seen right here performing as a DJ in Ukraine in an undated picture from social media.
The JabberZeus malware was custom-made for the crime group by the alleged writer of the Zeus trojan — Evgeniy Mikhailovich Bogachev, a high Russian cybercriminal with a $3 million bounty on his head from the FBI. Bogachev is accused of working the Gameover Zeus botnet, an enormous crime machine of 500,000 to 1 million contaminated PCs that was used for giant DDoS assaults and for spreading Cryptolocker — a peer-to-peer ransomware risk that was years forward of its time.
Investigators knew Bogachev and JabberZeus had been linked as a result of for a few years they had been studying the personal Jabber chats between and amongst members of the JabberZeus crew, and Bogachev’s monitored aliases had been in semi-regular contact with the group about updates to the malware.
Gary Warner, director of analysis in pc forensics on the College of Alabama at Birmingham, famous in his weblog from 2014 that Tank advised co-conspirators in a JabberZeus chat on July 22, 2009 that his daughter, Miloslava, had been born and gave her start weight.
“A search of Ukrainian start information solely confirmed one woman named Miloslava with that start weight born on that day,” Warner wrote. This was sufficient to positively establish Tank as Penchukov, Warner stated.
Finally, Penchukov’s political connections helped him evade prosecution by Ukrainian cybercrime investigators for a few years. The late son of former Ukrainian President Victor Yanukovych (Victor Yanukovych Jr.) would function godfather to Tank’s daughter Miloslava. By means of his connections to the Yanukovych household, Tank was capable of set up contact with key insiders in high tiers of the Ukrainian authorities, together with legislation enforcement.
Sources briefed on the investigation into Penchukov stated that in 2010 — at a time when the Safety Service of Ukraine (SBU) was making ready to serve search warrants on Tank and his crew — Tank obtained a tip that the SBU was coming to raid his residence. That warning gave Tank ample time to destroy essential proof towards the group, and to keep away from being residence when the raids occurred. These sources additionally stated Tank used his contacts to have the investigation into his crew moved to a unique unit that was headed by his corrupt SBU contact.
Writing for Know-how Evaluation, Patrick Howell O’Neil recounted how SBU brokers in 2010 had been trailing Tank across the metropolis, watching carefully as he moved between nightclubs and his residence.
“In early October, the Ukrainian surveillance workforce stated they’d misplaced him,” he wrote. “The People had been sad, and a little bit shocked. However they had been additionally resigned to what they noticed because the realities of working in Ukraine. The nation had a infamous corruption drawback. The working joke was that it was straightforward to seek out the SBU’s anticorruption unit—simply search for the parking zone filled with BMWs.”
AUTHOR’S NOTE/BACKGROUND
I first encountered Tank and the JabberZeus crew roughly 14 years in the past as a reporter for The Washington Submit, after a trusted supply confided that he’d secretly gained entry to the group’s personal Jabber conversations.
From studying these discussions every day, it grew to become clear Tank was nominally accountable for the Ukrainian crew, and that he spent a lot of his time overseeing the actions of the cash mule recruiters — which had been an integral a part of their sufferer cashout scheme.
It was quickly found that the phony company web sites the cash mule recruiters used to handle new hires had a safety weak point that allowed anybody who signed up on the portal to view messages for each different person. A scraping software was constructed to reap these cash mule recruitment messages, and on the peak of the JabberZeus gang’s exercise in 2010 that scraper was monitoring messages on near a dozen completely different cash mule recruitment websites, every managing tons of of “staff.”
Every mule was given busy work or menial duties for a couple of days or even weeks previous to being requested to deal with cash transfers. I imagine this was an effort to weed out unreliable cash mules. In spite of everything, those that confirmed up late for work tended to price the crooks some huge cash, because the sufferer’s financial institution would often attempt to reverse any transfers that hadn’t already been withdrawn by the mules.
When it got here time to switch stolen funds, the recruiters would ship a message by the pretend firm web site saying one thing like: “Good morning [mule name here]. Our shopper — XYZ Corp. — is sending you some cash at present. Please go to your financial institution now and withdraw this cost in money, after which wire the funds in equal funds — minus your fee — to those three people in Jap Europe.”
Solely, in each case the corporate talked about because the “shopper” was in truth a small enterprise whose payroll accounts they’d already hacked into.
So, every day for a number of years my morning routine went as follows: Make a pot of espresso; shuffle over to the pc and look at the messages Tank and his co-conspirators had despatched to their cash mules over the earlier 12-24 hours; lookup the sufferer firm names in Google; decide up the telephone to warn every that they had been within the means of being robbed by the Russian Cyber Mob.
My spiel on all of those calls was roughly the identical: “You most likely do not know who I’m, however right here’s all my contact information and what I do. Your payroll accounts have been hacked, and also you’re about to lose a substantial amount of cash. You must contact your financial institution instantly and have them put a maintain on any pending transfers earlier than it’s too late. Be happy to name me again afterwards if you’d like extra details about how I do know all this, however for now please simply name or go to your financial institution.”
In lots of situations, my name would are available simply minutes or hours earlier than an unauthorized payroll batch was processed by the sufferer firm’s financial institution, and a few of these notifications prevented what in any other case would have been monumental losses — typically a number of instances the quantity of the group’s regular weekly payroll. In some unspecified time in the future I finished counting what number of tens of 1000’s of {dollars} these calls saved victims, however over a number of years it was most likely within the thousands and thousands.
Simply as typically, the sufferer firm would suspect that I used to be one way or the other concerned within the theft, and shortly after alerting them I’d obtain a name from an FBI agent or from a police officer within the sufferer’s hometown. These had been all the time fascinating conversations.
Collectively, these notifications to victims led to dozens of tales over a number of years about small companies battling their monetary establishments to recuperate their losses. I by no means wrote a few single sufferer that wasn’t okay with my calling consideration to their plight and to the sophistication of the risk dealing with different firms.
This incessant meddling on my half very a lot aggravated Tank, who on a couple of event expressed mystification as to how I knew a lot about their operations and victims. Right here’s a snippet from one in all their Jabber chats in 2009, after I’d written a narrative for The Washington Submit about their efforts to steal $415,000 from the coffers of Bullitt County, Kentucky. Within the chat beneath, “lucky12345” is the Zeus writer Bogachev:
tank: Are you there?
tank: That is what they rattling wrote about me.
tank: http://voices.washingtonpost.com/securityfix/2009/07/an_odyssey_of_fraud_part_ii.html#extra
tank: I’ll take a fast have a look at historical past
tank: Originator: BULLITT COUNTY FISCAL Firm: Bullitt County Fiscal Court docket
tank: Properly, you bought [it] from that cash-in.
lucky12345: From 200K?
tank: Properly, they don’t seem to be the best quantities and the money out from that account was shitty.
tank: Levak was written there.
tank: As a result of now the whole USA is aware of about Zeus.
tank: 😀
lucky12345: It’s fucked.
On Dec. 13, 2009, one in all Tank’s high cash mule recruiters — a criminal who used the pseudonym “Jim Rogers” — advised his boss one thing I hadn’t shared past a couple of trusted confidants at that time: That The Washington Submit had eradicated my job within the means of merging the newspaper’s Website online (the place I labored on the time) with the useless tree version.
jim_rogers: There’s a rumor that our favourite (Brian) didn’t get his contract extension at Washington Submit. We’re giddily awaiting affirmation 🙂 Excellent news anticipated precisely by the New Yr! Moreover us nobody reads his column 🙂
tank: Mr. Fucking Brian Fucking Kerbs!
One other member of the JabberZeus crew — Ukrainian-born Maksim “Aqua” Yakubets — is also presently needed by the FBI, which is providing a $5 million reward for info resulting in his arrest and conviction.
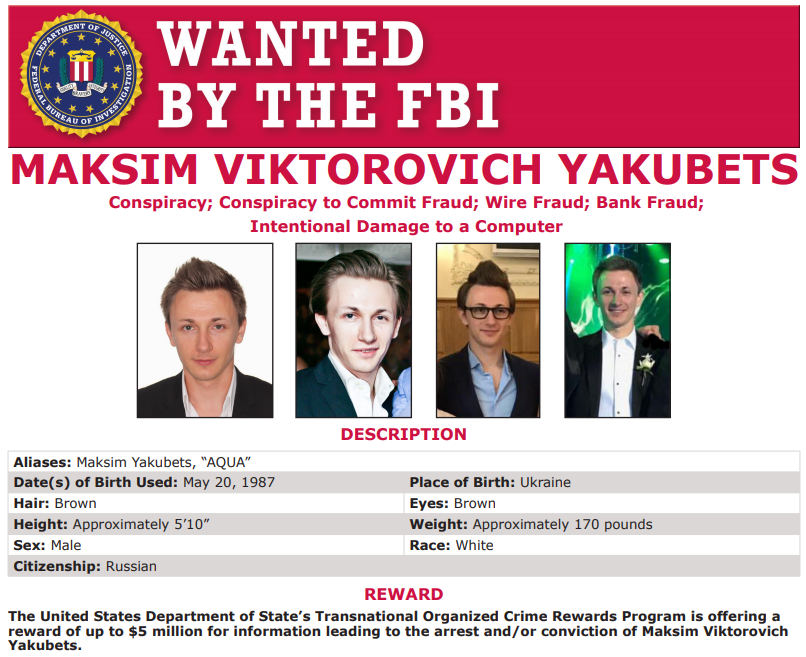
Alleged “Evil Corp” bigwig Maksim “Aqua” Yakubets. Picture: FBI

/cdn.vox-cdn.com/uploads/chorus_asset/file/24195246/dreamup_creation_by_thedextriarchy_dfhwouu_pre.jpeg)