The US joined the UK and Australia in the present day in sanctioning 31-year-old Russian nationwide Dmitry Yuryevich Khoroshev because the alleged chief of the notorious ransomware group LockBit. The U.S. Division of Justice additionally indicted Khoroshev and charged him with utilizing Lockbit to assault greater than 2,000 victims and extort no less than $100 million in ransomware funds.

Picture: U.Okay. Nationwide Crime Company.
Khoroshev (Дмитрий Юрьевич Хорошев), a resident of Voronezh, Russia, was charged in a 26-count indictment by a grand jury in New Jersey.
“Dmitry Khoroshev conceived, developed, and administered Lockbit, probably the most prolific ransomware variant and group on the planet, enabling himself and his associates to wreak havoc and trigger billions of {dollars} in harm to 1000’s of victims across the globe,” U.S. Lawyer Philip R. Sellinger stated in a press release launched by the Justice Division.
The indictment alleges Khoroshev acted because the LockBit ransomware group’s developer and administrator from its inception in September 2019 by way of Might 2024, and that he usually acquired a 20 p.c share of every ransom cost extorted from LockBit victims.
The federal government says LockBit victims included people, small companies, multinational companies, hospitals, colleges, nonprofit organizations, crucial infrastructure, and authorities and law-enforcement businesses.
“Khoroshev and his co-conspirators extracted no less than $500 million in ransom funds from their victims and induced billions of {dollars} in broader losses, similar to misplaced income, incident response, and restoration,” the DOJ stated. “The LockBit ransomware group attacked greater than 2,500 victims in no less than 120 nations, together with 1,800 victims in america.”
The unmasking of LockBitSupp comes practically three months after U.S. and U.Okay. authorities seized the darknet web sites run by LockBit, retrofitting it with press releases in regards to the legislation enforcement motion and free instruments to assist LockBit victims decrypt contaminated methods.
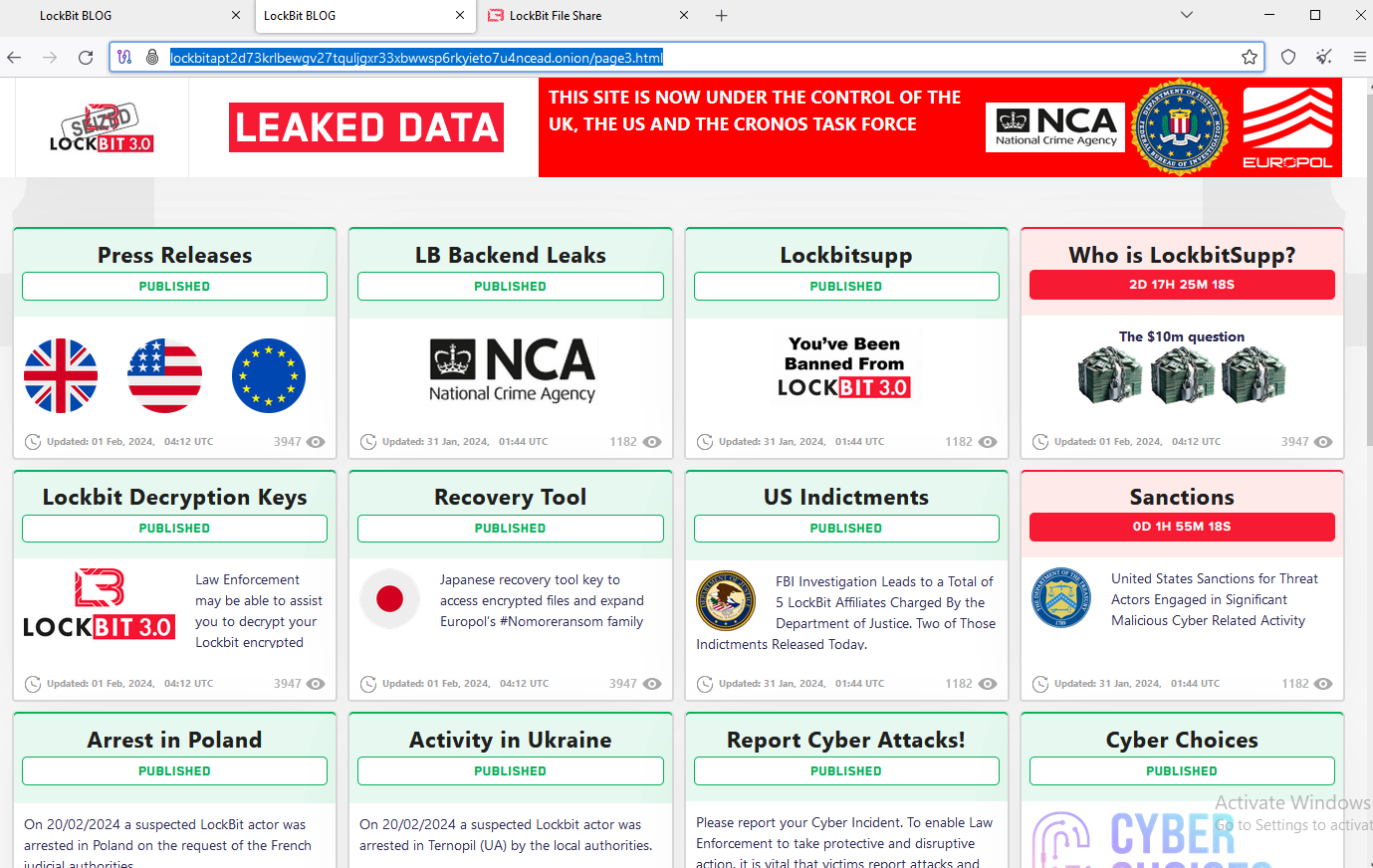
The feds used the prevailing design on LockBit’s sufferer shaming web site to function press releases and free decryption instruments.
One of many weblog captions that authorities left on the seized web site was a teaser web page that learn, “Who’s LockbitSupp?,” which promised to disclose the true id of the ransomware group chief. That merchandise featured a countdown clock till the large reveal, however when the location’s timer expired no such particulars had been supplied.
Following the FBI’s raid, LockBitSupp took to Russian cybercrime boards to guarantee his companions and associates that the ransomware operation was nonetheless totally operational. LockBitSupp additionally raised one other set of darknet web sites that quickly promised to launch knowledge stolen from various LockBit victims ransomed previous to the FBI raid.
One of many victims LockBitSupp continued extorting was Fulton County, Ga. Following the FBI raid, LockbitSupp vowed to launch delicate paperwork stolen from the county court docket system except paid a ransom demand earlier than LockBit’s countdown timer expired. However when Fulton County officers refused to pay and the timer expired, no stolen data had been ever revealed. Specialists stated it was seemingly the FBI had in reality seized all of LockBit’s stolen knowledge.
LockBitSupp additionally bragged that their actual id would by no means be revealed, and at one level supplied to pay $10 million to anybody who might uncover their actual identify.
KrebsOnSecurity has been in intermittent contact with LockBitSupp for a number of months over the course of reporting on completely different LockBit victims. Reached on the similar ToX immediate messenger id that the ransomware group chief has promoted on Russian cybercrime boards, LockBitSupp claimed the authorities named the fallacious man.
“It’s not me,” LockBitSupp replied in Russian. “I don’t perceive how the FBI was capable of join me with this poor man. The place is the logical chain that it’s me? Don’t you’re feeling sorry for a random harmless individual?”
LockBitSupp, who now has a $10 million bounty for his arrest from the U.S. Division of State, has been recognized to be versatile with the reality. The Lockbit group routinely practiced “double extortion” in opposition to its victims — requiring one ransom cost for a key to unlock hijacked methods, and a separate cost in change for a promise to delete knowledge stolen from its victims.
However Justice Division officers say LockBit by no means deleted its sufferer knowledge, no matter whether or not these organizations paid a ransom to maintain the knowledge from being revealed on LockBit’s sufferer shaming web site.
Khoroshev is the sixth individual formally indicted as lively members of LockBit. The federal government says Russian nationwide Artur Sungatov used LockBit ransomware in opposition to victims in manufacturing, logistics, insurance coverage and different corporations all through america.
Ivan Gennadievich Kondratyev, a.okay.a. “Bassterlord,” allegedly deployed LockBit in opposition to targets in america, Singapore, Taiwan, and Lebanon. Kondratyev can be charged (PDF) with three felony counts arising from his alleged use of the Sodinokibi (aka “REvil“) ransomware variant to encrypt knowledge, exfiltrate sufferer info, and extort a ransom cost from a company sufferer primarily based in Alameda County, California.
In Might 2023, U.S. authorities unsealed indictments in opposition to two alleged LockBit associates, Mikhail “Wazawaka” Matveev and Mikhail Vasiliev. In January 2022, KrebsOnSecurity revealed Who’s the Community Entry Dealer ‘Wazawaka,’ which adopted clues from Wazawaka’s many pseudonyms and phone particulars on the Russian-language cybercrime boards again to a 31-year-old Mikhail Matveev from Abaza, RU.
Matveev stays at giant, presumably nonetheless in Russia. In the meantime, the U.S. Division of State has a standing $10 million reward provide for info resulting in Matveev’s arrest.
Vasiliev, 35, of Bradford, Ontario, Canada, is in custody in Canada awaiting extradition to america (the criticism in opposition to Vasiliev is at this PDF).
In June 2023, Russian nationwide Ruslan Magomedovich Astamirov was charged in New Jersey for his participation within the LockBit conspiracy, together with the deployment of LockBit in opposition to victims in Florida, Japan, France, and Kenya. Astamirov is at the moment in custody in america awaiting trial.
The Justice Division is urging victims focused by LockBit to contact the FBI at https://lockbitvictims.ic3.gov/ to file an official criticism, and to find out whether or not affected methods will be efficiently decrypted.










