DUCK. Hey, everyone.
Welcome to this particular mini-episode of the Bare Safety podcast.
My identify is Paul Ducklin, and I’m joined at present by my buddy and colleague Chester Wisniewski.
Chester, I believed we should always say one thing about what has was the large story of the week… it’ll in all probability be the large story of the month!
I’ll simply learn you the headline I used on Bare Safety:
“UBER HAS BEEN HACKED, boasts hacker – how one can cease it taking place to you.”
So!
Inform us all about it….
CHET. Effectively, I can affirm that the vehicles are nonetheless driving.
I’m coming to you from Vancouver, I’m downtown, I’m looking the window, and there’s truly an Uber sitting outdoors the window…
DUCK. It hasn’t been there all day?
CHET. No, it hasn’t. [LAUGHS]
Should you press the button to hail a automobile contained in the app, relaxation assured: for the time being, it seems that you’ll even have somebody come and provide you with a journey.
Nevertheless it’s not essentially so assured, for those who’re an worker at Uber, that you simply’re going to be doing a lot of something for the following few days, contemplating the affect on their methods.
We don’t know a whole lot of particulars, truly, Duck, of precisely what occurred.
However, at a really excessive degree, the consensus seems to be that there was some social engineering of an Uber worker that allowed somebody to get a foothold within Uber’s community.
They usually had been in a position to transfer laterally, as we are saying, or pivot, as soon as they bought inside with a purpose to discover some administrative credentials that finally led them to have the keys to the Uber kingdom.
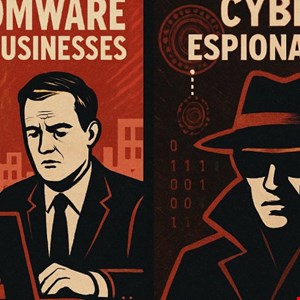
DUCK. So this doesn’t appear like a conventional information stealing, or nation state, or ransomware assault, does it?
CHET. No.
That’s to not say another person might not even have been of their community utilizing related methods – you by no means actually know.
In truth, when our Speedy Response group responds to incidents, we frequently discover that there’s been multiple menace actor inside a community, as a result of they exploited related strategies of entry.
DUCK. Sure… we even had a narrative of two ransomware crooks, mainly unknown to one another, who bought in on the identical time.
So, a number of the information had been encrypted with ransomware-A-then-ransomware-B, and a few with ransomware-B-followed-by-ransomware-A.
That was an unholy mess…
CHET. Effectively, that’s previous information, Duck. [LAUGHS]
We’ve since printed one other one the place *three* totally different ransomwares had been on the identical community.
DUCK. Oh, expensive! [BIG LAUGH] I hold laughing at this, however that’s flawed. [LAUGHS]
CHET. It’s not unusual for a number of menace actors to be in, as a result of, as you say, if one particular person is ready to uncover a flaw in your strategy to defending your community, there’s nothing to counsel that different folks might not have found the identical flaw.
However on this case, I believe you’re proper, in that it appears to be “for the lulz”, if you’ll.
I imply, the one that did it was principally accumulating trophies as they bounced by the community – within the type of screenshots of all these totally different instruments and utilities and applications that had been in use round Uber – and posting them publicly, I suppose for the road cred.
DUCK. Now, in an assault finished by any individual who *didn’t* need bragging rights, that attacker may have been an IAB, an preliminary entry dealer, couldn’t they?
During which case, they wouldn’t have made a giant noise about it.
They’d have collected all of the passwords after which bought out and stated, “Who wish to purchase them?”
CHET. Sure, that’s super-super harmful!
As dangerous because it appears to be Uber proper now, particularly somebody on Uber’s PR or inside safety groups, it’s truly the absolute best consequence…
…which is simply that the end result of that is going to be embarrassment, in all probability some fines for dropping delicate worker info, that form of factor.
However the fact of the matter is for nearly everybody else that this sort of an assault victimises, the top consequence finally ends up being ransomware or a number of ransomwares, mixed with cryptominers and different kinds of knowledge theft.
That’s far, much more expensive to the organisation than merely being embarrassed.
DUCK. So this concept of crooks getting in and having the ability to wander round at will and choose and select the place they go…
…is unfortunately commonplace.
CHET. It actually emphasises the significance of actively on the lookout for issues, versus ready for alerts.
Clearly, this particular person was in a position to breach Uber safety with out triggering any alerts initially, which allowed them the time to wander round.
That’s why menace looking, because the terminology goes, is so vital nowadays.
As a result of the nearer to minute-zero or day-zero you can detect the suspicious exercise of individuals poking round in file shares and instantly logging into an entire bunch of methods serially in a row – these kinds of actions, or a number of RDP connections flying across the community from accounts that aren’t usually related to that exercise…
…these kinds of suspicious issues may help you restrict the quantity of injury that particular person could cause, by limiting the period of time they should unravel some other safety errors you could have made that allowed them to realize entry to these administrative credentials.
It is a factor that a whole lot of groups are actually combating: how one can see these authentic instruments being abused?
That’s an actual problem right here.
As a result of, on this instance, it feels like an Uber worker was tricked into inviting somebody in, in a disguise that seemed like them in the long run.
You’ve now bought a authentic worker’s account, one which unintentionally invited a felony into their pc, working round doing issues that worker might be not usually related to.
So that basically must be a part of your monitoring and menace looking: realizing what regular actually is so, you can detect “anomalous regular”.
As a result of they didn’t deliver malicious instruments with them – they’re utilizing instruments which can be already there.
We all know they checked out PowerShell scripts, that form of factor – the stuff you in all probability have already got.
What’s uncommon is that this particular person interacting with that PowerShell, or this particular person interacting with that RDP.
And people are issues which can be a lot tougher to be careful for than merely ready for an alert to pop up in your dashboard.
DUCK. So, Chester, what’s your recommendation for corporations that don’t need to discover themselves in Uber’s place?
Though this assault has understandably bought a large quantity of publicity, due to the screenshots which can be circulating, as a result of it appears to be, “Wow, the crooks bought completely in all places”…
…the truth is, it’s not a novel story so far as information breaches go.
CHET. You requested concerning the recommendation, what would I inform an organisation?
And I’ve to assume again to an excellent buddy of mine who was a CISO of a serious college in america about ten years in the past.
I requested him what his safety technique was and he stated: “It’s quite simple. Assumption of breach.”
I assume I’m breached, and that persons are in my community that I don’t need in my community.
So I’ve to construct every thing with the belief that any individual’s already in right here who shouldn’t be, and ask, “Do I’ve the safety in place although the decision is coming from inside the home?”
Immediately we have now a buzzword for that: Zero Belief, which most of us are sick of claiming already. [LAUGHS]
However that’s the strategy: assumption of breach; zero belief.
You shouldn’t have the liberty to easily roam round since you placed on a disguise that seems to be an worker of the organisation.
DUCK. And that’s actually the important thing of Zero Belief, isn’t it?
It doesn’t imply, “Uou must not ever belief anyone to do something.”
It’s form of a metaphor for saying, “Assume nothing”, and, “Don’t authorise folks to do greater than they should do for the duty in hand.”
CHET. Exactly.
On the belief that your attackers don’t get as a lot pleasure from outing the truth that you had been hacked as occurred on this case…
…you in all probability need to ensure you have a great way for employees members to report anomalies when one thing doesn’t appear proper, to make it possible for they can provide a heads-up to your safety group.
As a result of speaking about information breach dwell instances from our Energetic Adversary Playbook, the criminals most frequently are in your community for at the least ten days:
So that you’ve bought a stable week-to-ten-days, sometimes, the place for those who simply have some eagle eyes which can be recognizing issues, you’ve bought an actual good probability at shutting it down earlier than the worst occurs.
DUCK. Certainly, as a result of if you consider how a typical phishing assault works, it’s very uncommon that the crooks will succeed on the primary try.
And in the event that they don’t succeed on the primary try, they don’t simply pack up their baggage and wander away.
They struggle the following particular person, and the following particular person, and the following particular person.
In the event that they’re solely going to succeed after they strive the assault on the fiftieth particular person, then If any of the earlier 49 noticed it and stated one thing, you would have intervened and glued the issue.
CHET. Completely – that’s vital!
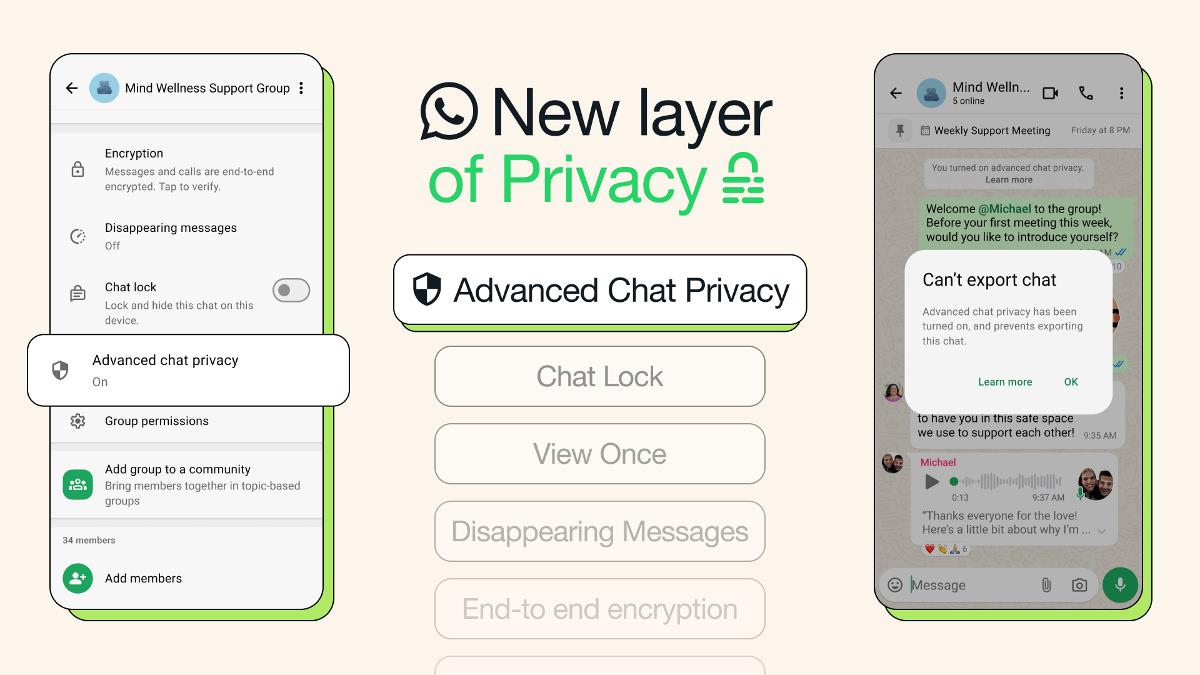
And also you talked about tricking folks into freely giving 2FA tokens.
That’s an vital level right here – there was multi-factor authentication at Uber, however the particular person appears to have been satisfied to bypass it.
And we don’t know what that methodology was, however most multi-factor technique, sadly, do have the power to be bypassed.
All of us are acquainted with the time-based tokens, the place you get the six digits on the display screen and also you’re requested to place these six digits into the app to authenticate.
In fact, there’s nothing stopping you from giving the six digits to the flawed particular person in order that they’ll authenticate.
So, two issue authentication isn’t an all-purpose drugs that cures all illness.
It’s merely a velocity bump that’s one other step alongside the trail to changing into safer.
DUCK. A well-determined criminal who’s bought the time and the persistence to maintain on attempting might ultimately get in.
And such as you say, your objective is to minimise the time they’ve to maximise the return on the truth that they bought within the first place…
CHET. And that monitoring must occur on a regular basis.
Firms like Uber are giant sufficient to have their very own 24/7 safety operations centre to watch issues, although we’re not fairly certain what occurred right here, and the way lengthy this particular person was in, and why they weren’t stopped
However most organizations will not be essentially ready to have the ability to do this in-house.
It’s super-handy to have exterior sources obtainable that may monitor – *repeatedly* monitor – for this malicious behaviour, shortening even additional the period of time that the malicious exercise is occurring.
For people that perhaps have common IT tasks and different work to do, it may be fairly exhausting to see these authentic instruments getting used, and spot one explicit sample of them getting used as a malicious factor…
DUCK. The buzzword that you simply’re speaking about there’s what we all know as MDR, brief for Managed Detection and Response, the place you get a bunch of consultants both to do it for you or that can assist you.
And I believe there are nonetheless fairly lots of people on the market who think about, “If I’m seen to do this, doesn’t it appear like I’ve abrogated my accountability? Isn’t it an admission that I completely don’t know what I’m doing?”
And it isn’t, is it?
In truth, you would argue it’s truly doing issues in a extra managed means, since you’re selecting folks that can assist you take care of your community *who do this and solely that* for a residing.
And that signifies that your common IT group, and even your individual safety group… within the occasion of an emergency, they’ll truly stick with it doing all the opposite issues that want doing anyway, even for those who’re below assault.
CHET. Completely.
I suppose the final thought I’ve is that this…
Don’t understand a model like Uber being hacked as which means that it’s unattainable so that you can defend your self.
Massive firm names are nearly large trophy trying to find folks just like the particular person concerned on this explicit hack.
And simply because a giant firm perhaps didn’t have the safety they need to doesn’t imply you possibly can’t!
There was a whole lot of defeatist chatter amongst a whole lot of organisations I talked to after some earlier large hacks, like Goal, and Sony, and a few of these hacks that we had within the information ten years in the past.
And folks had been like, “Aaargh… if with all of the sources of Goal they’ll’t defend themselves, what hope is there for me?”
And I don’t actually assume that’s true in any respect.
In most of those circumstances, they had been focused as a result of they had been very giant organizations, and there was a really small gap of their strategy that any individual was in a position to get in by.
That doesn’t imply that you simply don’t have an opportunity at defending your self.
This was social engineering, {followed} by some questionable practices of storing passwords in PowerShell information.
These are issues you can very simply look ahead to, and educate your staff on, to make sure that you’re not making the identical errors.
Simply because Uber can’t do it doesn’t imply you possibly can’t!
DUCK. Certainly – I believe that’s very nicely put, Chester.
Do you thoughts if I finish with one among my conventional cliches?
(The factor about cliches is that they often turn out to be cliches by being true and helpful.)
After incidents like this: “Those that can’t bear in mind historical past are condemned to repeat it – don’t be that particular person!”
Chester, thanks a lot for taking day trip of your busy schedule, as a result of I do know you even have a web-based discuss to do tonight.
So, thanks a lot for that.
And allow us to end in our customary means by saying, “Till subsequent time, keep safe.”
[MUSICAL MODEM]